IEEE Account
- Change Username/Password
- Update Address

Purchase Details
- Payment Options
- Order History
- View Purchased Documents
Profile Information
- Communications Preferences
- Profession and Education
- Technical Interests
- US & Canada: +1 800 678 4333
- Worldwide: +1 732 981 0060
- Contact & Support
- About IEEE Xplore
- Accessibility
- Terms of Use
- Nondiscrimination Policy
- Privacy & Opting Out of Cookies
A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity. © Copyright 2024 IEEE - All rights reserved. Use of this web site signifies your agreement to the terms and conditions.
Subscribe to the PwC Newsletter
Join the community, add a new evaluation result row, cloud computing.
89 papers with code • 0 benchmarks • 0 datasets
Benchmarks Add a Result
Latest papers, cluster-wide task slowdown detection in cloud system.

To tackle these challenges, we propose SORN (i. e., Skimming Off subperiods in descending amplitude order and Reconstructing Non-slowing fluctuation), which consists of a Skimming Attention mechanism to reconstruct the compound periodicity and a Neural Optimal Transport module to distinguish cluster-wide slowdowns from other exceptional fluctuations.
Adaptive Two-Stage Cloud Resource Scaling via Hierarchical Multi-Indicator Forecasting and Bayesian Decision-Making
The surging demand for cloud computing resources, driven by the rapid growth of sophisticated large-scale models and data centers, underscores the critical importance of efficient and adaptive resource allocation.
Comparing Deep Learning Models for Rice Mapping in Bhutan Using High Resolution Satellite Imagery
For this independent model evaluation, the U-Net RGBN, RGBNE, RGBNES, and RGBN models displayed the F1-scores of 0. 5935, 0. 6154, 0. 5882, and 0. 6582, suggesting U-Net RGBNES as the best model.
Privacy-Preserving Deep Learning Using Deformable Operators for Secure Task Learning
To address these challenges, we propose a novel Privacy-Preserving framework that uses a set of deformable operators for secure task learning.
IMPaCT: Interval MDP Parallel Construction for Controller Synthesis of Large-Scale Stochastic Systems
kiguli/impact • 7 Jan 2024
This paper is concerned with developing a software tool, called IMPaCT, for the parallelized verification and controller synthesis of large-scale stochastic systems using interval Markov chains (IMCs) and interval Markov decision processes (IMDPs), respectively.
LiPar: A Lightweight Parallel Learning Model for Practical In-Vehicle Network Intrusion Detection
Through experiments, we prove that LiPar has great detection performance, running efficiency, and lightweight model size, which can be well adapted to the in-vehicle environment practically and protect the in-vehicle CAN bus security.
CloudEval-YAML: A Practical Benchmark for Cloud Configuration Generation
alibaba/cloudeval-yaml • 10 Nov 2023
We develop the CloudEval-YAML benchmark with practicality in mind: the dataset consists of hand-written problems with unit tests targeting practical scenarios.
Deep learning based Image Compression for Microscopy Images: An Empirical Study
In the end, we hope the present study could shed light on the potential of deep learning based image compression and the impact of image compression on downstream deep learning based image analysis models.
MLatom 3: Platform for machine learning-enhanced computational chemistry simulations and workflows
MLatom 3 is a program package designed to leverage the power of ML to enhance typical computational chemistry simulations and to create complex workflows.
Federated learning compression designed for lightweight communications
Federated Learning (FL) is a promising distributed method for edge-level machine learning, particularly for privacysensitive applications such as those in military and medical domains, where client data cannot be shared or transferred to a cloud computing server.
Advances, Systems and Applications
- Open access
- Published: 06 August 2022
Big data analytics in Cloud computing: an overview
- Blend Berisha 1 ,
- Endrit Mëziu 1 &
- Isak Shabani 1
Journal of Cloud Computing volume 11 , Article number: 24 ( 2022 ) Cite this article
38k Accesses
42 Citations
10 Altmetric
Metrics details
Big Data and Cloud Computing as two mainstream technologies, are at the center of concern in the IT field. Every day a huge amount of data is produced from different sources. This data is so big in size that traditional processing tools are unable to deal with them. Besides being big, this data moves fast and has a lot of variety. Big Data is a concept that deals with storing, processing and analyzing large amounts of data. Cloud computing on the other hand is about offering the infrastructure to enable such processes in a cost-effective and efficient manner. Many sectors, including among others businesses (small or large), healthcare, education, etc. are trying to leverage the power of Big Data. In healthcare, for example, Big Data is being used to reduce costs of treatment, predict outbreaks of pandemics, prevent diseases etc. This paper, presents an overview of Big Data Analytics as a crucial process in many fields and sectors. We start by a brief introduction to the concept of Big Data, the amount of data that is generated on a daily bases, features and characteristics of Big Data. We then delve into Big Data Analytics were we discuss issues such as analytics cycle, analytics benefits and the movement from ETL to ELT paradigm as a result of Big Data analytics in Cloud. As a case study we analyze Google’s BigQuery which is a fully-managed, serverless data warehouse that enables scalable analysis over petabytes of data. As a Platform as a Service (PaaS) supports querying using ANSI SQL. We use the tool to perform different experiments such as average read, average compute, average write, on different sizes of datasets.
Introduction
We live in the data age. We see them everywhere and this is due to the great technological developments that have taken place in recent years. The rate of digitalization has increased significantly and now we are rightly talking about” digital information societies”. If 20 or 30 years ago only 1% of the information produced was digital, now over 94% of this information is digital and it comes from various sources such as our mobile phones, servers, sensor devices on the Internet of Things, social networks, etc. [ 1 ]. The year 2002 is considered the” beginning of the digital age” where an explosion of digitally produced equipment and information was seen.
The number and amount of information collected has increased significantly due to the increase of devices that collect this information such as mobile devices, cheap and numerous sensor devices on the Internet of Things (IoT), remote sensing, software logs, cameras, microphones, RFID readers, wireless sensor networks, etc. [ 2 ]. According to statistics, the amount of data generated / day is about 44 zettabytes (44 × 10 21 bytes). Every second, 1.7 MB of data is generated per person [ 3 ]. Based on International Data Group forecasts, the global amount of data will increase exponentially from 2020 to 2025, with a move from 44 to 163 zettabytes [ 4 ]. Figure 1 shows the amount of global data generated, copied and consumed. As can be seen, in the years 2010–2015, the rate of increase from year to year has been smaller, while since 2018, this rate has increased significantly thus making the trend exponential in nature [ 3 ].
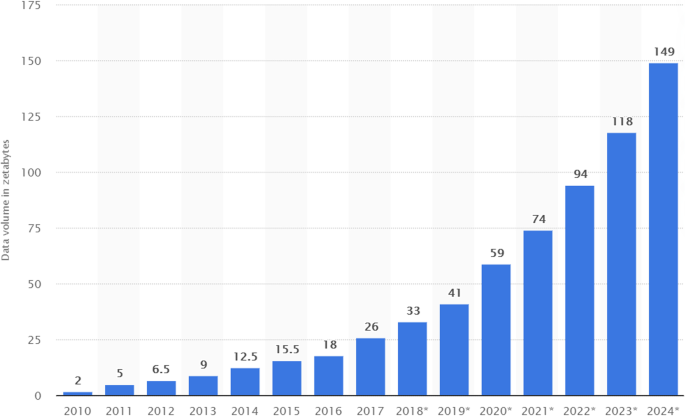
Volume of data/information created, captured, copied, and consumed worldwide from 2010 to 2024 (estimated) [ 3 ]
To get a glimpse of the amount of data that is generated on a daily basis, let’s see a portion of data that different platforms produce. On the Internet, there is so much information at our fingertips. We add to the stockpile everytime we look for answers from our search engines. As a results Google now produces more than 500,000 searches every second (approximately 3.5 billion search per day) [ 5 ]. By the time of writing this article, this number must have changed! Social media on the other hand is a massive data producer.
People’s ‘love affair’ with social media certainly fuels data creation. Every minute, Snapchat users share 527,760 photos, more than 120 professionals join LinkedIn, users watch 4,146,6000 Youtube videos, 456,000 are sent to Twitter and Instagram users post 46,740 photos [ 5 ]. Facebook remains the largest social media platform, with over 300 million photos uploaded every day with more than 510,000 comments posted and 293,000 statuses updated every minute.
With the increase in the number and quantity of data, there have been advantages but also challenges as systems for managing relational databases and other traditional systems have difficulties in processing and analyzing this quantity. For this reason, the term ‘big data’ arose not only to describe the amount of data but also the need for new technologies and ways of processing and analyzing this data. Cloud Computing has facilitated data storage, processing and analysis. Using Cloud we have access to almost limitless storage and computer power offered by different vendors. Cloud delivery models such as: IAAS (Infrastructure as a Service), PAAS (Platform as a Service) can help organisations across different sectors handle Big Data easier and faster. The aim of this paper is to provide an overview of how analytics of Big Data in Cloud Computing can be done. For this we use Google’s platform BigQuery which is a serverless data warehouse with built-in machine learning capabilities. It’s very robust and has plenty of features to help with the analytics of different size and type of data.
What is big data?
Many authors and organizations have tried to provide a definition of ‘Big Data’. According to [ 6 ] “Big Data refers to data volumes in the range of exabytes and beyond”. In Wikipedia [ 7 ] big data is defined as an accumulation of datasets so huge and complex that it becomes hard to process using database management tools or traditional data processing applications, while the challenges include capture, storage, search, sharing, transfer, analysis, and visualization.
Sam Madden from Massachusetts Institute of Technology (MIT) considers” Big Data” to be data that is too big, too fast, or too hard for existing tools to process [ 8 ]. By too big, it means data that is at the petabyte level and that comes from various sources. By ‘too fast’ it means data growth which is fast and should also be processed quickly. By too hard it means the difficulty that arises as a result the data not adapting to the existing processing tools [ 9 ]. In PCMag (one of the most popular journals on technological trends), Big data refers to the massive amounts of data that is collected over time that are difficult to analyze and handle using common database management tools [ 10 ]. There are many other definitions for Big Data, but we consider that these are enough to gain an impression on this concept.
Features and characteristics of big data
One question that researchers have struggled to answer is what might qualify as ‘big data’? For this reason, in 2001 industry analyst Doug Laney from Gartner introduced the 3 V model which are three features that must complement the data to be considered” big data”: volume, velocity, variety . Volume is a property or characteristic that determines the size of data, usually reported in Terabyte or Petabyte. For example, social networks like Facebook store among others photos of users. Due to the large number of users, it is estimated that Facebook stores about 250 billion photos and over 2.5 trillion posts of its users. This is an extremely large amount of data that needs to be stored and processed. Volume is the most representative feature of ‘big data’ [ 8 ]. In terms of volume, tera or peta level data is usually considered ‘big’ although this depends on the capacity of those analyzing this data and the tools available to them [ 8 ]. Figure 2 shows what each of the three V's represent.
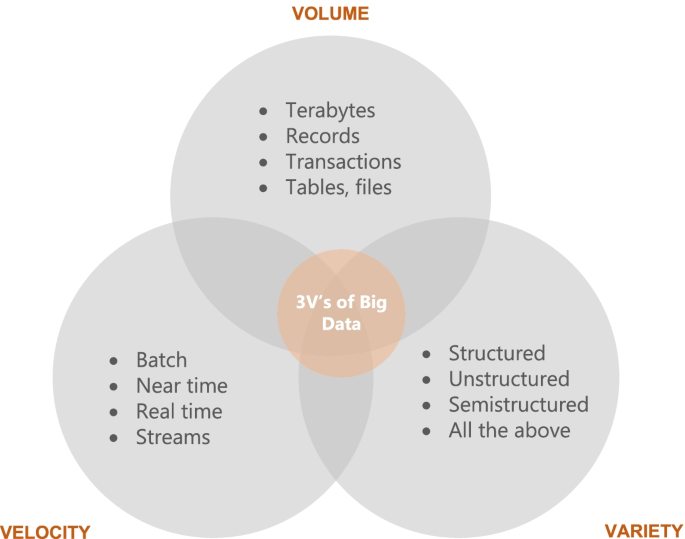
3 V’s of Big Data [ 6 ]
The second property or characteristic is velocity . This refers to the degree to which data is generated or the speed at which this data must be processed and analyzed [ 8 ]. For example, Facebook users upload more than 900 million photos a day, which is approximately 104 uploaded photos per second. In this way, Facebook needs to process, store and retrieve this information to its users in real time. Figure 3 shows some statistics obtained from [ 11 ] which show the speed of data generation from different sources. As can be seen, social media and the Internet of Things (IoT) are the largest data generators, with a growing trend.
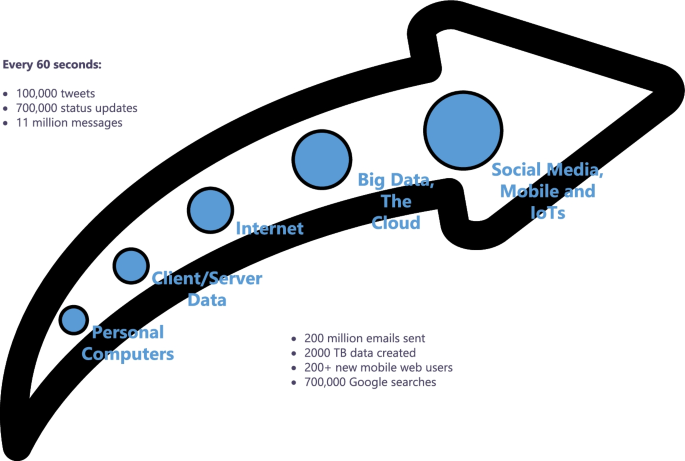
Examples of the velocity of Big Data [ 9 ]
There are two main types of data processing: batch and stream. In batch, processing happens in blocks of data that have been stored over a period of time. Usually data processed in batch are big, so they will take longer to process. Hadoop MapReduce is considered to be the best framework for processing data in batches [ 11 ]. This approach works well in situations where there is no need for real-time analytics and where it is important to process large volumes of data to get more detailed insights.
Stream processing, on the other hand, is a key to the processing and analysis of data in real time. Stream processing allows for data processing as they arrive. This data is immediately fed into analytics tools so the results are generated instantly. There are many scenarios where such an approach can be useful such as fraud detection, where anomalies that signal fraud are detected in real time. Another use case would be online retailers, where real-time processing would enable them to compile large histories of costumer interactions so that additional purchases could be recommended for the costumers in real time [ 11 ].
The third property is variety , which refers to different types of data which are generated from different sources. “Big Data” is usually classified into three major categories: structured data (transactional data, spreadsheets, relational databases etc.), semi-structured (Extensible Markup Language - XML, web server logs etc) and unstructured (social media posts, audio, images, video etc.). In the literature, as a fourth category is also mentioned ‘meta-data’ which represents data about data. This is also shown in Fig. 4 . Most of the data today belong to the category of unstructured data (80%) [ 11 ].

Main categories of data variety in Big Data [ 9 ]
Over time, the tree features of big data have been complemented by two additional ones: veracity and value . Veracity is equivalent to quality, which means data that are clean and accurate and that have something to offer [ 12 ]. The concept is also related to the reliability of data that is extracted (e.g., costumer sentiments in social media are not highly reliable data). Value of the data is related to the social or economic value data can generate. The degree of value data can produce depends also on the knowledge of those that make use of it.
Big data analytics in cloud computing
Cloud Computing is the delivery of computing services such as servers, storage, databases, networking, software, analytics etc., over the Internet (“the cloud”) with the aim of providing flexible resources, faster innovation and economies of scale [ 13 ]. Cloud computing has revolutionized the way computing infrastructure is abstracted and used. Cloud paradigms have been extended to include anything that can be considered as a service (hence x a service). The many benefits of cloud computing such as elasticity, pay-as-you-go or pay-per-use model, low upfront investment etc., have made it a viable and desirable choice for big data storage, management and analytics [ 13 ]. Because big data is now considered vital for many organizations and fields, service providers such as Amazon, Google and Microsoft are offering their own big data systems in a cost-efficient manner. These systems offer scalability for business of all sizes. This had led to the prominence of the term Analytics as a Service (AaaS) as a faster and efficient way to integrate, transform and visualize different types of data. Data Analytics.
Big data analytics cycle
According to [ 14 ] processing big data for analytics differs from processing traditional transactional data. In traditional environments, data is first explored then a model design as well as a database structure is created. Figure 5 . depicts the flow of big data analysis. As can be seen, it starts by gathering data from multiple sources, such as multiple files, systems, sensors and the Web. This data is then stored in the so called” landing zone” which is a medium capable of handling the volume, variety and velocity of data. This is usually a distributed file system. After data is stored, different transformations occur in this data to preserve its efficiency and scalability. Afer that, they are integrated into particular analytical tasks, operational reporting, databases or raw data extracts [ 14 ].
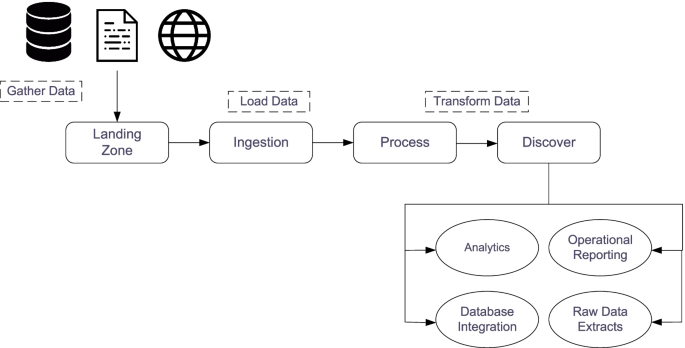
Flow in the processing of Big Data [ 11 ]
Moving from ETL to ELT paradigm
ETL (Extract, Transform, Load) is about taking data from a data source, applying the transformations that might be required and then load it into a data warehouse to run reports and queries against them. The downside of this approach or paradigm is that is characterized by a lot of I/O activity, a lot of string processing, variable transformation and a lot of data parsing [ 15 ].
ELT (Extract, Load, Transform) is about taking the most compute-intensive activity (transformation) and doing it not in an on-premise service which is already under pressure with regular transaction-handling but instead taking it to the cloud [ 15 ]. This means that there is no need for data staging because data warehousing solution is used for different types.
of data including those that are structured, semi-structured, unstructured and raw. This approach employs the concept of” data lakes” that are different from OLAP (Online Analytical Processing) data warehouses because they do not require the transformation of data before loading them [ 15 ]. Figure 6 illustrates the differences between the two paradigms. As seen, the main difference is where transformation process takes place.
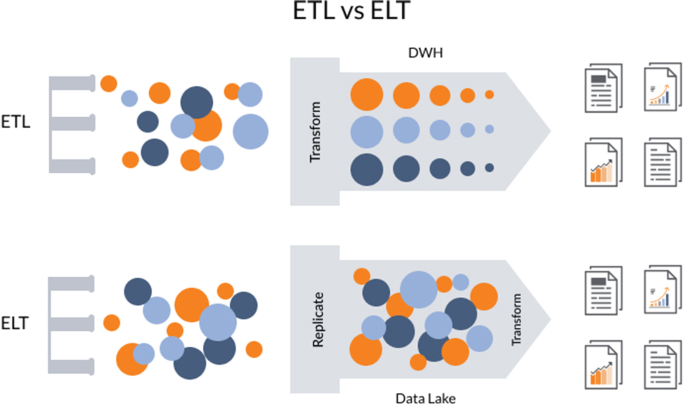
Differences between ETL and ELT [ 15 ]
ELT has many benefits over traditional ETL paradigm. The most crucial, as mentioned, is the fact that data of any format can be ingested as soon as it becomes available. Another one is the fact that only the data required for particular analysis can be transformed. In ETL, the entire pipeline and structure of the data in the OLAP may require modification if the previous structure does not allow for new types of analysis [ 16 ].
Some advantages of big data analytics
As mentioned, companies across various sectors in the industry are leveraging Big Data in order to promote decision making that is data-driven. Besides tech industry, the usage and popularity of Big Data has expanded to include healthcare, governance, retail, supply chain management, education etc. Some of the benefits of Big Data Analytics mentioned in [ 17 ] include:
Data accumulation from different sources including the Internet, online shopping sites, social media, databases, external third-party sources etc.
Identification of crucial points that are hidden within large datasets in order to influence business decisions.
Identification of the issues regarding systems and business processes in real time.
Facilitation of service/product delivery to meet or exceed client expecations.
Responding to customer requests, queries and grievances in real time.
Some other benefits according to [ 16 ] are related to:
Cost optimization - One of the biggest advantages of Big Data tools such as Hadoop or Spark is that they offer cost advantages to businesses regarding the storage, processing and analysis of large amounts of data. Authors mention the logistics industry as an example to highlight the cost-reduction benefits of Big Data. In this industry, the cost of product returns is 1.5 times higher than that of actual shipping costs. With Big Data Analytics, companies can minimize product return costs by predicting the likelihood of product returns. By doing so, they can then estimate which products are most likely to be returned and thus enable the companies to take suitable measures to reduce losses on returns.
Efficiency improvements - Big Data can improve operational efficiency by a margin. Big Data tools can amass large amounts of useful costumer data by interacting and gaining their feedback. This data can then be analyzed and interpreted to extract some meaningful patterns hidden within such as customer taste and preferences, buying behaviors etc. This in turn allows companies to create personalized or tailored products/services.
Innovation - Insights from Big Data can be used to tweak business strategies, develop new products/services, optimize service delivery, improve productivity etc. These can all lead to more innovation.
As seen, Big Data Analytics has been mostly leveraged by businesses, but other sectors have also benefited. For example, in healthcare many states are now utilizing the power of Big Data to predict and also prevent epidemics, cure diseases, cut down costs etc. This data has also been used to establish many efficient treatment models. With Big Data more comprehensive reports were generated and these were then converted into relevant critical insights to provide better care [ 17 ].
In education, Big Data has also been used extensively. They have enabled teachers to measure, monitor and respond in real-time to student’s understanding of the material. Professors have created tailor-made materials for students with different knowledge levels to increase their interest [ 18 ].
Case study: GOOGLE’S big query for data processing and analytics
Google Cloud Platform contains a number of services designed to analyze and process big data. Throughout this paper we have described and discussed the architecture and main components of Biguery as one of the most used big data processing tools in GCP. BigQuery is a fully-managed, serverless data warehouse that enables scalable analysis over petabytes of data. It is a Platform as a Service (PaaS) that supports querying using ANSI SQL. It also has built-in machine learning capabilities. Since its launch in 2011 it has gained a lot of popularity and many big companies have utilized it for their data analytics [ 19 ].
From a user perspective, BigQuery has an intuitive user interface which can be accessed in a number of ways depending on user needs. The simplest way to interact with this tool is to use its graphical web interface as shown in Fig. 7 . Slightly more complicated but faster approaches include using cloud console or Bigquery APIs. From Fig. 7 Bigquery web interface offers you the options to add or select existing datasets, schedule and construct queries or transfer data and display results.

BigQuery Interface
Data processing and query construction occurs under the sql workspace section, Bigquery offers a rich sql-like syntax to compute and process large sets of data, it operates on relational datasets with well-defined structure including tables with specified columns and types. Figure 8 shows a simple query construction syntax and highlights its execution details. Data displayed under query results shows main performance components of the executed query starting from elapsed time, consumed slot time, size of data processed, average and maximum wait, write and compute times. Query defined in Fig. 8 combines three datasets which contain information regarding Covid-19 reported cases, deaths and recoveries from more than 190 countries through year 2020 till January 2021. Google BigQuery is flexible in a way that allows you to use and combine various datasets suitable for your task easily and with small delays. It contains an ever growing list of public datasets at your disposal and also offers the options to create, edit and import your own. Figure 9 shows the process of adding a table to the newly created dataset. From the Fig. 9 , we see that for table creation as a source we have used a local csv file, this file will be used to create table schema and populate it with data, aside from local upload option as a source to create the table we can use Google BigTable, Google Cloud Storage or Google Drive. The newly created table with its respective data then is ready to be used to construct queries and obtain new insights as shown in Fig. 8 .
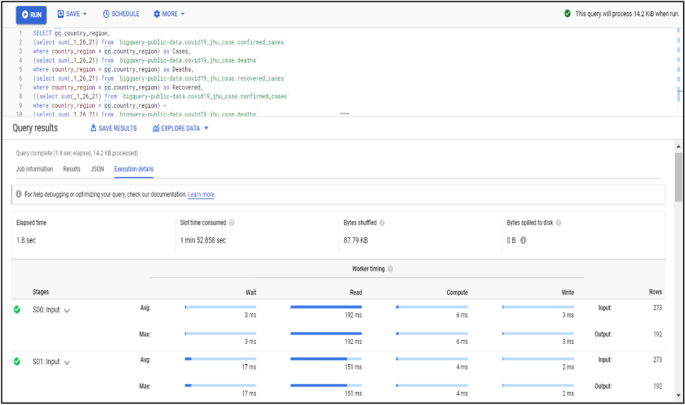
BigQuery execution details
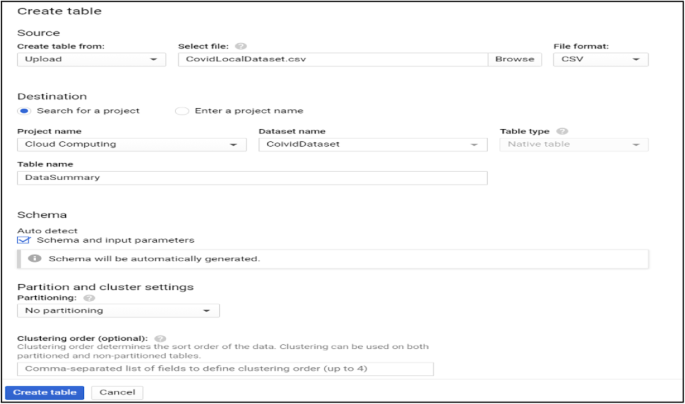
Adding table to the created dataset
One advantage of using imported data in the cloud is the option to manage its access and visibility in the cloud project and cloud members scope. Depending from the way of use, queried data can be saved directly to the local computer through the use of “save results” option from Fig. 8 which offers a variety of formats and data extensions settings to choose from but can also be explored in different configurations using “explore data” option. You can also save constructed queries for later use or schedule query execution interval for more accurate data transmutation through API endpoints. Figure 10 shows how much the average compute time will change/increase with the increase in the size of the dataset used.
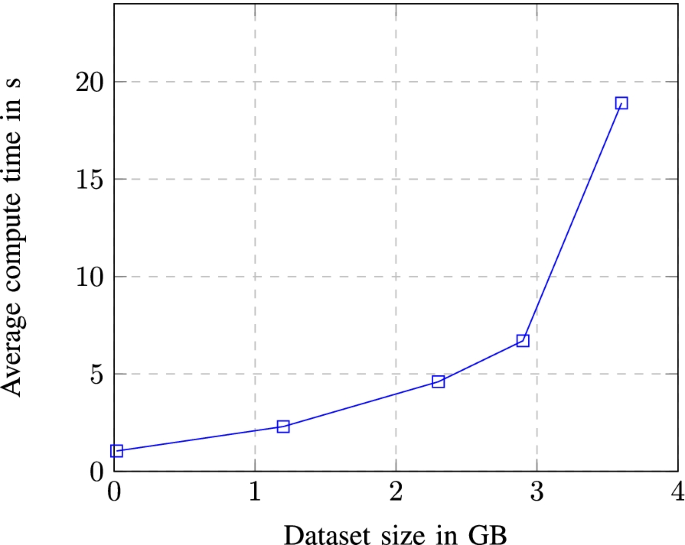
Average compute time dependence in dataset size
Experiments with different dataset sizes
Before moving to data exploration lets analyze performance results of BigQuery in simple queries with variable dataset sizes. In Table 1 we have shown the query execution details of five simple select queries done on five different datasets. The results are displayed against six different performance categories, from the data we see a correlation between size of the dataset and its average read, write and compute.
From the graph we see that the dependence between dataset size and average compute size is exponential, meaning that with the increase in data size, average compute time is exponentially increased.
Data returned from constructed queries aside from being displayed in a simple tabular form or as a JSON object can also be transferred to data studio which is an integrated tool to better display and visualize gathered information. One way of displaying queried data from Fig. 8 with data studio tool is shown in Fig. 11 . In this case a bar table chart visualization option is chosen.
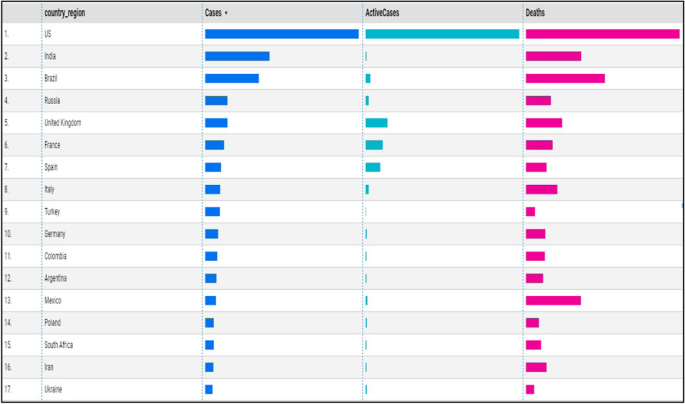
Using data studio for data visualization
Big Data is not a new term but has gained its spotlight due to the huge amounts of data that are produced daily from different sources. From our analysis we saw that big data is increasing in a fast pace, leading to benefits but also challenges. Cloud Computing is considered to be the best solution for storing, processing and analyzing Big Data. Companies like Amazon, Google and Microsoft offer their public services to facilitate the process of dealing with Big Data. From the analysis we saw that there are multiple benefits that Big Data analytics provides for many different fields and sectors such as healthcare, education and business. We also saw that because of the interaction of Big Data with Cloud Computing there is a shift in the way data is processed and analyzed. In traditional settings, ETL is used whereas in Big Data, ELT is used. We saw that the latter has clear advantages when compared to the former.
From our case study we saw that BigQuery is very good for running complex analytical queries, which means there is no point in running queries that are doing simple aggregation or filtering. BigQuery is suitable for heavy queries, those that operate using a big set of data. The bigger the dataset, the more it is likely to gain in performance. This is when compared to the traditional relational databases,as BigQuery implements different parallel schemas to speed up the execution time.
BigQuery doesn’t like joins and merging data into one table gets a better execution time. It is good for scenarios where data does not change often as it has built-in cache. BigQuery can also be used when one wants to reduce the load on the relational database as it offers different options and configurations to improve query performance. Also pay as you go service can be used where charges are made based on usage or flat rate service which offers a specific slot rate and charges in daily, monthly or yearly plan.
Availability of data and materials
The datasets used during the current study are available from the corresponding author on reasonable request. The authors declare that they have no funder.
Hillbert M, Lopez P (2011) The world’s technological capacity to store, communicate and compute information. Science III:62–65
Google Scholar
J. Hellerstein,“ Gigaom Blog,”2019. Available: https://gigaom.com/2008/11/09/mapreduce-leads-the-way-for-parallelprogramming/ . Accessed 20 Jan 2021
Statista,“Statista,“2020. Available: https://www.statista.com/statistics/871513/worldwide-data-created/ . Accessed 21 Jan 2021
Reinsel D, Gantz J, Rydning J (2017) Data age 2025: the evolution of data to-life critical. International Data Corporation, Framingham
Forbes, “Forbes”, 2020. Available: https://www.forbes.com/sites/bernardmarr/2018/05/21/how-muchdata-do-we-create-every-day-the-mind-blowing-stats-everyone-shouldread/?sh=5936b00460ba
Kaisler S, Armour F, Espinosa J (2013) Big data: issues and challenges moving forward, Wailea, Maui, HI, s.n, pp 995–1004
Wikipedia,“ Wikipedia,” 2018. Available: https://www.en.wikipedia.org/wiki/Bigdata/ . Accessed 4 Jan 2021
D. Gewirtz,“ ZDNet,” 2018. Available: https://www.zdnet.com/article/volume-velocity-and-varietyunderstanding-the-three-vs-of-big-data/ . Accessed 1 Jan 2021
Weathington J (2012) Big Data Defined. Tech Republic. https://www.techrepublic.com/article/big-data-defined/
PCMagazine,“ PC Magazine,” 2018. Available: http://www.pcmag.com/encyclopedia/term/62849/big-data . Accessed 9 Jan 2021
Akhtar SMF (2018) Big Data Architect’s Handbook, Packt
WhishWorks, “WhishWorks”, 2019. Available: https://www.whishworks.com/blog/data-analytics/understanding-the3-vs-of-big-data-volume-velocity-and-variety/ . Accessed 23 Jan 2021
Yadav S, Sohal A (2017) Review paper on big data analytics in Cloud computing. Int J Comp Trends Technol (IJCTT) IX. 49(3);156-160
Kimball R, Ross M (2013) The data warehouse toolkit: the definitive guide to dimensional modeling, 3rd edn. John Wiley & Sons
LaprinthX, “LaprinthX,”2018. Available: https://laptrinhx.com/better-faster-smarter-elt-vs-etl-2084402419/ . Accessed 22 Jan 2021
Xplenty, “XPlenty, ”, 2019. Available: https://www.xplenty.com/blog/etl-vs-elt/# . Accessed 20 Jan 2021
Forbes,“Forbes,”,2018. Available: https://www.forbes.com/sites/forbestechcouncil/2019/11/06/fivebenefits-of-big-data-analytics-and-how-companies-can-getstarted/?sh=7e1b901417e4 . Accessed 13 Jan 202
EDHEC, “EDHEC, ”, 2019. Available: https://master.edhec.edu/news/three-ways-educators-are-using-bigdata-analytics-improve-learning-process# . Accessed 6 Jan 2021
Google Cloud, “BigQuery, ”, 2020. Available: https://cloud.google.com/bigquery . Accessed 5 Jan 2021
Download references
Acknowledgements
The authors would like to thank the colleageous and professors from the University of Prishtina for their insightful comments and suggestions that helped in improving the quality of the paper.
The authors declare that they have no funder.
Author information
Authors and affiliations.
Faculty of Electrical and Computer Engineering, Department of Computer Engineering, University of Prishtina, 10000, Prishtina, Kosovo
Blend Berisha, Endrit Mëziu & Isak Shabani
You can also search for this author in PubMed Google Scholar
Contributions
Blend Berisha wrote the Introduction, Features and characteristics of Big Data and Conclusions. Endrit Meziu wrote Big Data¨ Analytics in Cloud Computing and part of the case study. Isak Shabani has contributed in the methodology, resources and in supervising the work process. All authors prepared the figures and also reviewed the manuscript. The author(s) read and approved the final manuscript.
Corresponding author
Correspondence to Isak Shabani .
Ethics declarations
Ethics approval and consent to participate.
Not applicable.
Consent for publication
Competing interests.
The authors declare that they have no competing interests.
Additional information
Publisher’s note.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article's Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/ .
Reprints and permissions
About this article
Cite this article.
Berisha, B., Mëziu, E. & Shabani, I. Big data analytics in Cloud computing: an overview. J Cloud Comp 11 , 24 (2022). https://doi.org/10.1186/s13677-022-00301-w
Download citation
Received : 08 April 2022
Accepted : 24 July 2022
Published : 06 August 2022
DOI : https://doi.org/10.1186/s13677-022-00301-w
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Cloud computing
cloud computing Recently Published Documents
Total documents.
- Latest Documents
- Most Cited Documents
- Contributed Authors
- Related Sources
- Related Keywords
Simulation and performance assessment of a modified throttled load balancing algorithm in cloud computing environment
<span lang="EN-US">Load balancing is crucial to ensure scalability, reliability, minimize response time, and processing time and maximize resource utilization in cloud computing. However, the load fluctuation accompanied with the distribution of a huge number of requests among a set of virtual machines (VMs) is challenging and needs effective and practical load balancers. In this work, a two listed throttled load balancer (TLT-LB) algorithm is proposed and further simulated using the CloudAnalyst simulator. The TLT-LB algorithm is based on the modification of the conventional TLB algorithm to improve the distribution of the tasks between different VMs. The performance of the TLT-LB algorithm compared to the TLB, round robin (RR), and active monitoring load balancer (AMLB) algorithms has been evaluated using two different configurations. Interestingly, the TLT-LB significantly balances the load between the VMs by reducing the loading gap between the heaviest loaded and the lightest loaded VMs to be 6.45% compared to 68.55% for the TLB and AMLB algorithms. Furthermore, the TLT-LB algorithm considerably reduces the average response time and processing time compared to the TLB, RR, and AMLB algorithms.</span>
An improved forensic-by-design framework for cloud computing with systems engineering standard compliance
Reliability of trust management systems in cloud computing.
Cloud computing is an innovation that conveys administrations like programming, stage, and framework over the web. This computing structure is wide spread and dynamic, which chips away at the compensation per-utilize model and supports virtualization. Distributed computing is expanding quickly among purchasers and has many organizations that offer types of assistance through the web. It gives an adaptable and on-request administration yet at the same time has different security dangers. Its dynamic nature makes it tweaked according to client and supplier’s necessities, subsequently making it an outstanding benefit of distributed computing. However, then again, this additionally makes trust issues and or issues like security, protection, personality, and legitimacy. In this way, the huge test in the cloud climate is selecting a perfect organization. For this, the trust component assumes a critical part, in view of the assessment of QoS and Feedback rating. Nonetheless, different difficulties are as yet present in the trust the board framework for observing and assessing the QoS. This paper talks about the current obstructions present in the trust framework. The objective of this paper is to audit the available trust models. The issues like insufficient trust between the supplier and client have made issues in information sharing likewise tended to here. Besides, it lays the limits and their enhancements to help specialists who mean to investigate this point.
Cloud Computing Adoption in the Construction Industry of Singapore: Drivers, Challenges, and Strategies
An extensive review of web-based multi granularity service composition.
The paper reviews the efforts to compose SOAP, non-SOAP and non-web services. Traditionally efforts were made for composite SOAP services, however, these efforts did not include the RESTful and non-web services. A SOAP service uses structured exchange methodology for dealing with web services while a non-SOAP follows different approach. The research paper reviews the invoking and composing a combination of SOAP, non-SOAP, and non-web services into a composite process to execute complex tasks on various devices. It also shows the systematic integration of the SOAP, non-SOAP and non-web services describing the composition of heterogeneous services than the ones conventionally used from the perspective of resource consumption. The paper further compares and reviews different layout model for the discovery of services, selection of services and composition of services in Cloud computing. Recent research trends in service composition are identified and then research about microservices are evaluated and shown in the form of table and graphs.
Integrated Blockchain and Cloud Computing Systems: A Systematic Survey, Solutions, and Challenges
Cloud computing is a network model of on-demand access for sharing configurable computing resource pools. Compared with conventional service architectures, cloud computing introduces new security challenges in secure service management and control, privacy protection, data integrity protection in distributed databases, data backup, and synchronization. Blockchain can be leveraged to address these challenges, partly due to the underlying characteristics such as transparency, traceability, decentralization, security, immutability, and automation. We present a comprehensive survey of how blockchain is applied to provide security services in the cloud computing model and we analyze the research trends of blockchain-related techniques in current cloud computing models. During the reviewing, we also briefly investigate how cloud computing can affect blockchain, especially about the performance improvements that cloud computing can provide for the blockchain. Our contributions include the following: (i) summarizing the possible architectures and models of the integration of blockchain and cloud computing and the roles of cloud computing in blockchain; (ii) classifying and discussing recent, relevant works based on different blockchain-based security services in the cloud computing model; (iii) simply investigating what improvements cloud computing can provide for the blockchain; (iv) introducing the current development status of the industry/major cloud providers in the direction of combining cloud and blockchain; (v) analyzing the main barriers and challenges of integrated blockchain and cloud computing systems; and (vi) providing recommendations for future research and improvement on the integration of blockchain and cloud systems.
Cloud Computing and Undergraduate Researches in Universities in Enugu State: Implication for Skills Demand
Cloud building block chip for creating fpga and asic clouds.
Hardware-accelerated cloud computing systems based on FPGA chips (FPGA cloud) or ASIC chips (ASIC cloud) have emerged as a new technology trend for power-efficient acceleration of various software applications. However, the operating systems and hypervisors currently used in cloud computing will lead to power, performance, and scalability problems in an exascale cloud computing environment. Consequently, the present study proposes a parallel hardware hypervisor system that is implemented entirely in special-purpose hardware, and that virtualizes application-specific multi-chip supercomputers, to enable virtual supercomputers to share available FPGA and ASIC resources in a cloud system. In addition to the virtualization of multi-chip supercomputers, the system’s other unique features include simultaneous migration of multiple communicating hardware tasks, and on-demand increase or decrease of hardware resources allocated to a virtual supercomputer. Partitioning the flat hardware design of the proposed hypervisor system into multiple partitions and applying the chip unioning technique to its partitions, the present study introduces a cloud building block chip that can be used to create FPGA or ASIC clouds as well. Single-chip and multi-chip verification studies have been done to verify the functional correctness of the hypervisor system, which consumes only a fraction of (10%) hardware resources.
Study On Social Network Recommendation Service Method Based On Mobile Cloud Computing
Cloud-based network virtualization in iot with openstack.
In Cloud computing deployments, specifically in the Infrastructure-as-a-Service (IaaS) model, networking is one of the core enabling facilities provided for the users. The IaaS approach ensures significant flexibility and manageability, since the networking resources and topologies are entirely under users’ control. In this context, considerable efforts have been devoted to promoting the Cloud paradigm as a suitable solution for managing IoT environments. Deep and genuine integration between the two ecosystems, Cloud and IoT, may only be attainable at the IaaS level. In light of extending the IoT domain capabilities’ with Cloud-based mechanisms akin to the IaaS Cloud model, network virtualization is a fundamental enabler of infrastructure-oriented IoT deployments. Indeed, an IoT deployment without networking resilience and adaptability makes it unsuitable to meet user-level demands and services’ requirements. Such a limitation makes the IoT-based services adopted in very specific and statically defined scenarios, thus leading to limited plurality and diversity of use cases. This article presents a Cloud-based approach for network virtualization in an IoT context using the de-facto standard IaaS middleware, OpenStack, and its networking subsystem, Neutron. OpenStack is being extended to enable the instantiation of virtual/overlay networks between Cloud-based instances (e.g., virtual machines, containers, and bare metal servers) and/or geographically distributed IoT nodes deployed at the network edge.
Export Citation Format
Share document.
Academia.edu no longer supports Internet Explorer.
To browse Academia.edu and the wider internet faster and more securely, please take a few seconds to upgrade your browser .
- We're Hiring!
- Help Center
Cloud Computing
- Most Cited Papers
- Most Downloaded Papers
- Newest Papers
- Last »
- Access Control Follow Following
- VoIP/SIP/IMS Follow Following
- Distributed Information Systems Follow Following
- Cyber Physical Systems Follow Following
- Semantic Computing Follow Following
- P2P/Overlay Networks Follow Following
- Smart spaces Follow Following
- Complex Event Processing Follow Following
- Cyber Security Follow Following
- Data Mining Follow Following
Enter the email address you signed up with and we'll email you a reset link.
- Academia.edu Journals
- We're Hiring!
- Help Center
- Find new research papers in:
- Health Sciences
- Earth Sciences
- Cognitive Science
- Mathematics
- Computer Science
- Academia ©2024
Information
- Author Services
Initiatives
You are accessing a machine-readable page. In order to be human-readable, please install an RSS reader.
All articles published by MDPI are made immediately available worldwide under an open access license. No special permission is required to reuse all or part of the article published by MDPI, including figures and tables. For articles published under an open access Creative Common CC BY license, any part of the article may be reused without permission provided that the original article is clearly cited. For more information, please refer to https://www.mdpi.com/openaccess .
Feature papers represent the most advanced research with significant potential for high impact in the field. A Feature Paper should be a substantial original Article that involves several techniques or approaches, provides an outlook for future research directions and describes possible research applications.
Feature papers are submitted upon individual invitation or recommendation by the scientific editors and must receive positive feedback from the reviewers.
Editor’s Choice articles are based on recommendations by the scientific editors of MDPI journals from around the world. Editors select a small number of articles recently published in the journal that they believe will be particularly interesting to readers, or important in the respective research area. The aim is to provide a snapshot of some of the most exciting work published in the various research areas of the journal.
Original Submission Date Received: .
- Active Journals
- Find a Journal
- Proceedings Series
- For Authors
- For Reviewers
- For Editors
- For Librarians
- For Publishers
- For Societies
- For Conference Organizers
- Open Access Policy
- Institutional Open Access Program
- Special Issues Guidelines
- Editorial Process
- Research and Publication Ethics
- Article Processing Charges
- Testimonials
- Preprints.org
- SciProfiles
- Encyclopedia

Article Menu

- Subscribe SciFeed
- Recommended Articles
- Google Scholar
- on Google Scholar
- Table of Contents
Find support for a specific problem in the support section of our website.
Please let us know what you think of our products and services.
Visit our dedicated information section to learn more about MDPI.
JSmol Viewer
Forensic investigation, challenges, and issues of cloud data: a systematic literature review.

1. Introduction
2. background.
- Detecting cloud crimes related to data and activities conducted through cloud services, such as security breaches, electronic fraud, data theft, and espionage.
- Providing legal evidence that can be used in courts to help solve crimes.
- Maintaining cloud stability by identifying weaknesses in the cloud infrastructure to prevent future attacks.
- Supporting international legal investigations by analyzing cloud user data and tracking illicit activities online.
2.1. Overview of Cloud Computing
2.1.1. cloud deployment models.
- Public Cloud: This is considered the most common of the deployment models because it is accessible to the general public, as its name implies, and available to everyone. In other words, companies lease resources to users based on their needs only, on a pay-as-you-go principle. Some offer free services but with limitations. There is a demand for them because they do not require maintenance or hardware changes on the part of the client [ 15 ].
- Private Cloud: We are not differentiating in the cloud infrastructure as all models are similar, and the technical structure of the private cloud is similar to the public cloud. However, the main difference lies in cloud ownership as it falls under the control of the company owner only. Maintenance and setup are carried out in a dedicated location belonging to the owning company. However, it is considered better in terms of security as it achieves high-level access authorization management. Only authorized personnel designated by the company are allowed access to the stored resources [ 16 ].
- Hybrid Cloud: This is considered a blend of the benefits of both public and private clouds, with high-quality management and protection policies applied. It provides a fundamental level of security and substantial resources. The hybrid cloud operates on the principle of segmentation, where there is a portion for protecting sensitive information from loss or damage and another portion for public deployment and general use. This cloud is typically owned by the company owner who leases it [ 16 ].
2.1.2. Cloud Service Models
- Ease of access and use by customers.
- Automatic updates are performed by the service provider.
- Customers are not restricted to a specific type of device to access the service.
- Cost savings for the client, as they pay a monthly subscription instead of purchasing the service.
- It is highly suitable for developers as it promotes a collaborative environment among them.
- It relieves developers from the burden of updates by means of an automatic system and software updates.
- It offers responsiveness and seamless integration with other cloud services.
- It allows resource consumption to be tailored to the specific needs of each client or developer.
- Scalable Resource Provisioning: Instead of purchasing resources, this model offers resource expansion based on the company’s needs. Resources are provided as a service in exchange for a monthly subscription.
- High-Level Security and Data Protection: This enhances client information and data with a high level of security and protection.
- Deployment Flexibility: This type of cloud service makes it possible to deploy in the region desired by the client, as providers typically own data centers in various regions.
2.2. Digital Forensics
2.3. cloud forensic analysis assists in conducting cloud forensic investigations, 2.4. cloud forensics.
- Gathering information from cloud service providers.
- Auditing activities that occurred within the cloud.
- Obtaining evidence related to unauthorized access or any breaches.
- Analyzing all the aforementioned points to identify suspects.
- Investigating and obtaining the outcome.
2.4.1. The Impact on Forensic Strategies
- Impact of the Cloud Deployment Models. Utilization of the public cloud involves the sharing of resources among numerous tenants, creating challenges in effectively segregating forensics data without impacting others. It is important to include forensic strategies to separate each tenant accurately. The legal agreement with cloud service providers plays a crucial role in ensuring access to forensics data [ 20 ]. The private cloud offers a high level of control and customization, but this comes at a significant cost and results in management complexity. The organization must ensure robust security measures and implement effective forensic strategies. These strategies should have the most control over the infrastructure to enforce various policies. Consequently, the organization can develop and deploy specialized tools and protocols within the private cloud for forensic purposes [ 21 ]. Integrating both private and public cloud services into the hybrid cloud may lead to challenges in conducting forensic investigations due to varying levels of control over data and infrastructure. Investigators must navigate through different policies and forensic tools utilized across the data sources [ 20 ]. The community cloud facilitates data sharing between organizations with similar interests and simplifies forensic efforts through standardized policies and procedures. The nature of the infrastructure presents similar challenges to those encountered in public cloud environments when separating data [ 20 ].
- Impact of Service Models. Investigators in the IaaS models have access to resources at a lower level, such as virtual machines and storage systems. This simplifies detailed forensic analysis, but requires a deep understanding of the virtual environment and the ability to manage and analyze a vast amount of data [ 20 ]. In the PaaS models, most of the infrastructure is abstracted, making it difficult to access primary data for forensic purposes. Investigators must collaborate closely with cloud service providers to obtain the required logs and other evidence, potentially causing delays in the investigation [ 20 ]. The SaaS model presents a significant challenge for the forensic field, with a high level of obfuscation and limited visibility into the infrastructure. Service providers control access to forensic data, leading to legal procedures to obtain the necessary evidence [ 20 ].
2.4.2. Challenges in Cloud Forensics
2.5. need for cloud forensics, 2.5.1. cases requiring cloud analysis, 2.5.2. the need for cloud forensic investigation arises from several factors, 2.6. cloud security concerns, 2.7. process of cloud forensics, 2.8. valuable practical and innovative perspectives of cloud forensics, 2.9. discussion, 3. methodology, 4. related works, literature reviews, 5. findings and insights, 5.1. challenges in cloud forensics.
- Technical Issues Cloud computing presents various technical challenges when it comes to preserving digital evidence, one of which involves safeguarding the evidence against any unauthorized modifications.
- Legal Issues The issue at hand pertains to privacy, which poses a significant obstacle for investigators. Consequently, investigators must meticulously and lawfully store the data they have collected.
- Resource Issues Conducting investigations in a cloud environment presents a range of challenges for investigators, including limitations that impact various aspects of digital forensics.
5.2. Techniques That Are Used to Solve the Challenges
6. comparison of systematic literature review with another paper, 7. conclusions, 8. future works.
- Addressing security vulnerabilities: Given the constantly evolving nature of cybersecurity threats, future research could concentrate on identifying and mitigating security vulnerabilities in cloud environments. This could involve developing strategies to detect and prevent insider attacks, data breaches, and other security incidents that may impact forensic investigations.
- Improving forensic analysis techniques: Research efforts could be directed towards enhancing forensic analysis techniques to overcome the unique challenges posed by cloud environments. This could involve exploring advanced methods for data recovery, memory forensics, and network traffic analysis techniques that are specifically optimized for cloud-based data.
- Promoting collaboration and knowledge sharing: Encouraging collaboration and knowledge sharing among researchers, practitioners, law enforcement agencies, and cloud service providers is crucial for advancing the field of cloud forensics. Future research could explore mechanisms for facilitating collaboration, such as establishing interdisciplinary research networks, organizing workshops and conferences, and creating repositories of best practices and case studies.
- Implement comprehensive logging and monitoring: It is important to verify that all cloud services have been set up to produce comprehensive logs and to consistently review and analyze these logs.
- Data preservation and collection: Create uniform protocols for safeguarding and gathering digital evidence within cloud settings to guarantee the reliability and acceptability of information.
- Ensure forensic readiness: Get ready for possible forensic investigations by integrating forensic readiness into the corporate culture and cloud deployment plan.
Data Availability Statement
Acknowledgments, conflicts of interest.
- Mell, P.; Grance, T. The NIST Definition of Cloud Computing ; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2011; pp. 800–1457. [ CrossRef ]
- Bhardwaj, A.K.; Garg, L.; Garg, A.; Gajpa, Y. E-Learning during COVID-19 Outbreak: Cloud Computing Adoption in Indian Public Universities. Comput. Mater. Contin. 2021 , 66 , 2471–2492. [ Google Scholar ] [ CrossRef ]
- Njenga, K.; Garg, L.; Bhardwaj, A.K.; Prakash, V.; Bawa, S. The cloud computing adoption in higher learning institutions in Kenya: Hindering factors and recommendations for the way forward. Telemat. Inform. 2019 , 38 , 225–246. [ Google Scholar ] [ CrossRef ]
- Karagiannis, C.; Vergidis, K. Digital Evidence and Cloud Forensics: Contemporary Legal Challenges and the Power of Disposal. Information 2021 , 12 , 181. [ Google Scholar ] [ CrossRef ]
- Ali, K.M. Digital Forensics Best Practices and Managerial Implications. In Proceedings of the 2012 Fourth International Conference on Computational Intelligence, Communication Systems and Networks, Phuket, Thailand, 24–26 July 2012; IEEE: Piscataway, NJ, USA, 2012; pp. 196–199. [ Google Scholar ] [ CrossRef ]
- Ruan, K.; Carthy, J.; Kechadi, T.; Baggili, I. Cloud forensics definitions and critical criteria for cloud forensic capability: An overview of survey results. Digit. Investig. 2013 , 10 , 34–43. [ Google Scholar ] [ CrossRef ]
- Simou, S.; Kalloniatis, C.; Gritzalis, S.; Mouratidis, H. A survey on cloud forensics challenges and solutions. Secur. Commun. Netw. 2016 , 9 , 6285–6314. [ Google Scholar ] [ CrossRef ]
- Martini, B.; Choo, K.K.R. Cloud storage forensics: OwnCloud as a case study. Digit. Investig. 2013 , 10 , 287–299. [ Google Scholar ] [ CrossRef ]
- Taylor, M.; Haggerty, J.; Gresty, D.; Lamb, D. Forensic investigation of cloud computing systems. Netw. Secur. 2011 , 2011 , 4–10. [ Google Scholar ] [ CrossRef ]
- Marty, R. Cloud application logging for forensics. In ACM Symposium on Applied Computing, Proceedings of the SAC’11: The 2011 ACM Symposium on Applied Computing, TaiChung, Taiwan, 21–24 March 2011 ; Association for Computing Machinery: New York, NY, USA, 2011; pp. 178–184. [ Google Scholar ] [ CrossRef ]
- Dykstra, J.; Sherman, A.T. Design and implementation of FROST: Digital forensic tools for the OpenStack cloud computing platform. Digit. Investig. 2013 , 10 , S87–S95. [ Google Scholar ] [ CrossRef ]
- Vadetay Saraswathi Bai, T.S. A Systematic Literature Review on Cloud Forensics in Cloud Environment. Int. J. Intell. Syst. Appl. Eng. 2023 , 11 , 565–578. [ Google Scholar ]
- Ruan, K.; Baggili, I.; Prof, J.; Carthy, P.; Kechadi, T. Survey on cloud forensics and critical criteria for cloud forensic capability: A preliminary analysis. Researchate . 2011. Available online: https://www.researchgate.net/publication/228419717_Survey_on_cloud_forensics_and_critical_criteria_for_cloud_forensic_capability_A_preliminary_analysis (accessed on 11 July 2024).
- Casino, F.; Dasaklis, T.K.; Spathoulas, G.P.; Anagnostopoulos, M.; Ghosal, A.; Borocz, I.; Solanas, A.; Conti, M.; Patsakis, C. Research Trends, Challenges, and Emerging Topics in Digital Forensics: A Review of Reviews. IEEE Access 2022 , 10 , 25464–25493. [ Google Scholar ] [ CrossRef ]
- Bamiah, M.; Brohi, S. Exploring the Cloud Deployment and Service Delivery Models. Int. J. Res. Rev. Inf. Sci. 2011 , 3 , 2046–6439. Available online: https://www.researchgate.net/publication/257995661_Exploring_the_Cloud_Deployment_and_Service_Delivery_Models (accessed on 3 July 2024).
- Gill, S.S.; Wu, H.; Patros, P.; Ottaviani, C.; Arora, P.; Pujol, V.C.; Haunschild, D.; Parlikad, A.K.; Cetinkaya, O.; Lutfiyya, H.; et al. Modern computing: Vision and challenges. Telemat. Inform. Rep. 2024 , 13 , 100116. [ Google Scholar ] [ CrossRef ]
- Alqahtany, S.; Clarke, N.; Furnell, S.; Reich, C. Cloud Forensics: A Review of Challenges, Solutions and Open Problems. In Proceedings of the 2015 International Conference on Cloud Computing (ICCC), Riyadh, Saudi Arabia, 26–29 April 2015; pp. 1–9. [ Google Scholar ]
- Sandhu, A.K. Big Data with Cloud Computing: Discussions and Challenges. Big Data Min. Anal. 2022 , 5 , 32–40. [ Google Scholar ] [ CrossRef ]
- Almulla, S.; Iraqi, Y.; Jones, A. Cloud forensics: A research perspective. In Proceedings of the 2013 9th International Conference on Innovations in Information Technology (IIT), Al Ain, United Arab Emirates, 17–19 March 2013; pp. 66–71. [ Google Scholar ] [ CrossRef ]
- Alazab, A.; Khraisat, A.; Singh, S. A Review on the Internet of Things (IoT) Forensics: Challenges, Techniques, and Evaluation of Digital Forensic Tools ; Intechopen: London, UK, 2023. [ Google Scholar ] [ CrossRef ]
- Abdulsalam, Y.S.; Hedabou, M. Security and Privacy in Cloud Computing: Technical Review. Future Internet 2022 , 14 , 11. [ Google Scholar ] [ CrossRef ]
- Microsoft. Microsoft Corp. v. United States. Supremecourt 2018 . Available online: https://www.supremecourt.gov/opinions/17pdf/16-402_h315.pdf (accessed on 11 July 2024).
- Dykstra, J.; Sherman, A.T. Acquiring forensic evidence from infrastructure-as-a-service cloud computing: Exploring and evaluating tools, trust, and techniques. Digit. Investig. 2012 , 9 , S90–S98. [ Google Scholar ] [ CrossRef ]
- Farina, J.; Scanlon, M.; Le-Khac, N.A.; Kechadi, M.T. Overview of the Forensic Investigation of Cloud Services. In Proceedings of the 2015 10th International Conference on Availability, Reliability and Security, Toulouse, France, 24–27 August 2015; pp. 556–565. [ Google Scholar ] [ CrossRef ]
- Malik, A.; Park, T.J.; Ishtiaq, H.; Ryou, J.C.; Kim, K.I. Cloud Digital Forensics: Beyond Tools, Techniques, and Challenges. Sensors 2024 , 24 , 433. [ Google Scholar ] [ CrossRef ] [ PubMed ]
- Chinedu, P.; Nwankwo, W.; Daniel; Shaba, M.; Momoh, M. Cloud Security Concerns: Assessing the Fears of Service Adoption. Arch. Sci. Technol. 2020 , 1 , 164–174. Available online: https://www.researchgate.net/publication/349607793_Cloud_Security_Concerns_Assessing_the_Fears_of_Service_Adoption (accessed on 13 July 2024).
- Ruan, K.; Carthy, J.; Kechadi, T.; Crosbie, M. Cloud forensics: An overview. ResearchGate 2011 . Available online: https://www.researchgate.net/publication/229021339_Cloud_forensics_An_overview (accessed on 11 July 2024).
- Microsoft. Governance, Security, and Compliance in Azure. Cloud Adoption Framework 2024 . Available online: https://learn.microsoft.com/en-us/azure/cloud-adoption-framework/ready/azure-setup-guide/govern-org-compliance?tabs=AzureSecurityCenter (accessed on 25 July 2024).
- AWS. AWS Security Best Practices. AWS Whitepaper 2016 . Available online: https://docs.aws.amazon.com/whitepapers/latest/aws-security-best-practices/welcome.html (accessed on 25 July 2024).
- Catteddu, D. Cloud Computing: Benefits, Risks and Recommendations for Information Security. In Web Application Security: Iberic Web Application Security Conference, IBWAS ; Springer: Berlin/Heidelberg, Germany, 2010; Volume 72, pp. 93–113. [ Google Scholar ] [ CrossRef ]
- Purnaye, P.; Kulkarni, V. A Comprehensive Study of Cloud Forensics. Arch. Comput. Methods Eng. 2021 , 29 , 33–46. [ Google Scholar ] [ CrossRef ]
- Mohammmed, S.; Sridevi, R. A Survey on Digital Forensics Phases, Tools and Challenges. In Proceedings of the Third International Conference on Computational Intelligence and Informatics: ICCII 2018, Hyderabad, India, 28–29 December 2018; Volume 1090, pp. 237–248. Available online: https://api.semanticscholar.org/CorpusID:215834965 (accessed on 24 July 2024).
- Yassin, W.M.; Abdollah, M.F.; Ahmad, R.; Yunos, Z.; Ariffin, A.F.M. Cloud Forensic Challenges and Recommendations: A Review. OIC-CERT J. Cyber Secur. 2020 , 2 . Available online: https://api.semanticscholar.org/CorpusID:216175392 (accessed on 9 July 2024).
- Fernando, V. Cyber Forensics Tools: A Review on Mechanism and Emerging Challenges. In Proceedings of the 2021 11th IFIP International Conference on New Technologies, Mobility and Security (NTMS), Paris, France, 19–21 April 2021; pp. 1–7. [ Google Scholar ] [ CrossRef ]
- Pandi (Jain), G.S.; Shah, S.; Wandra, K. Exploration of Vulnerabilities, Threats and Forensic Issues and its impact on the Distributed Environment of Cloud and its mitigation. Procedia Comput. Sci. 2020 , 167 , 163–173. [ Google Scholar ] [ CrossRef ]
- CHOI, D.H. Digital forensic: Challenges and solution in the protection of corporate crime. J. Ind. Distrib. Bus. 2021 , 12 , 47–55. [ Google Scholar ] [ CrossRef ]
- Sharma, P.; Arora, D.; Sakthivel, T. Enhanced Forensic Process for Improving Mobile Cloud Traceability in Cloud-Based Mobile Applications. Procedia Comput. Sci. 2020 , 167 , 907–917. [ Google Scholar ] [ CrossRef ]
- Vaidya, N. Cloud Forensics: Trends and Challenges. Int. J. Eng. Res. Technol. 2020 , 9 . Available online: https://www.ijert.org/research/cloud-forensics-trends-and-challenges-IJERTV9IS090415.pdf (accessed on 20 June 2024).
- Isaac Abiodun, O.; Alawida, M.; Esther Omolara, A.; Alabdulatif, A. Data provenance for cloud forensic investigations, security, challenges, solutions and future perspectives: A survey. J. King Saud Univ.-Comput. Inf. Sci. 2022 , 34 , 10217–10245. [ Google Scholar ] [ CrossRef ]
- Deebak, B.; AL-Turjman, F. Lightweight authentication for IoT/Cloud-based forensics in intelligent data computing. Future Gener. Comput. Syst. 2021 , 116 , 406–425. [ Google Scholar ] [ CrossRef ]
- Sharma, P.; Goel, S. A Practical Guide on Security and Privacy in Cyber-Physical Systems: Foundations, Applications and Limitations. World Sci. Ser. Digit. Forensics Cybersecur. 2023 , 3 , 264. [ Google Scholar ] [ CrossRef ]
- Alenezi, A.M. Digital and Cloud Forensic Challenges. arXiv 2023 , arXiv:2305.03059. [ Google Scholar ] [ CrossRef ]
- Kaleem, H.; Ahmed, I. Cloud Forensics: Challenges and Solutions (Blockchain Based Solutions). Innov. Comput. Rev. 2021 , 1 , 1–26. [ Google Scholar ] [ CrossRef ]
- Alouffi, B.; Hassnain, M.; Alharbi, A.; Alosaimi, W.; Alyami, H.; Ayaz, M. A Systematic Literature Review on Cloud Computing Security: Threats and Mitigation Strategies. IEEE Access 2021 , 9 , 57792–57807. [ Google Scholar ] [ CrossRef ]
- Ali, S.A.; Memon, S.; Sahito, F. Challenges and Solutions in Cloud Forensics. In Proceedings of the 2018 2nd International Conference on Cloud and Big Data Computing, Barcelona, Spain, 3–5 August 2018; pp. 6–10. [ Google Scholar ] [ CrossRef ]
- Prakash, V.; Williams, A.; Garg, L.; Savaglio, C.; Bawa, S. Cloud and Edge Computing-Based Computer Forensics: Challenges and Open Problems. Electronics 2021 , 10 , 1229. [ Google Scholar ] [ CrossRef ]
- Hemdan, E.E.D.; Manjaiah, D. An efficient digital forensic model for cybercrimes investigation in cloud computing. Multimedia Tools and Applications. In Multimedia Tools and Applications, Proceedings of the ICCBDC’18: 2018 2nd International Conference on Cloud and Big Data Computing, Barcelona, Spain, 3–5 August 2018 ; Association for Computing Machinery: New York, NY, USA, 2018; Volume 80, pp. 14255–14282. [ Google Scholar ] [ CrossRef ]
- Joshi, S.N.; Chillarge, G.R. Secure Log Scheme for Cloud Forensics. In Proceedings of the 2020 Fourth International Conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud) (I-SMAC), Palladam, India, 7–9 October 2020; pp. 188–193. [ Google Scholar ] [ CrossRef ]
- Javed, A.R.; Ahmed, W.; Alazab, M.; Jalil, Z.; Kifayat, K.; Gadekallu, T.R. A Comprehensive Survey on Computer Forensics: State-of-the-Art, Tools, Techniques, Challenges, and Future Directions. IEEE Access 2022 , 10 , 11065–11089. [ Google Scholar ] [ CrossRef ]
Click here to enlarge figure
| Cloud Deployment Models | Features | Drawbacks |
|---|---|---|
| Public Cloud | ||
| Private Cloud | ||
| Hybrid Cloud |
| Tool | Description |
|---|---|
| Data Recovery Software | Used to retrieve deleted or lost data from digital devices such as computers and smartphones. |
| Digital Analysis Software | Utilized for analyzing various forms of digital data, including images, videos, and text files. |
| Network Extraction and Analysis Tools | Employed to analyze network traffic and extract data related to network communications and online activities. |
| Encryption and Decryption Software | Utilized for analyzing encrypted data and decrypting it to extract analyzable information. |
| Image and Video Recovery Tools | Assist in recovering deleted or hidden images and video clips from digital devices. |
| Smart Analysis and Pattern Recognition Software | Used for intelligent data analysis and detecting unusual patterns and trends that may indicate illicit activities. |
| Characteristics of Cloud | Forensics Challenge |
|---|---|
| Scalability | Ensuring data integrity and maintaining chain of custody during dynamic resource scaling. |
| Accessibility | Investigating unauthorized access and data breaches across remote locations with different access levels. |
| Shared Resources | Managing data combination challenges and isolating digital evidence within a shared infrastructure. |
| Virtualization | Addressing forensic analysis problem in virtualized systems and abstracted hardware environments. |
| Data Distribution | Handling the challenges associated with legal jurisdictions and data locations in cloud storage systems spread across multiple geographic regions. |
| Ref. | Techniques | Challenges | Main Finding |
|---|---|---|---|
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] | |||
| [ ] |
| Technical Challenges | Resource Challenges | Legal Challenges |
|---|---|---|
| Challenge | Type | Potential Security Solution |
|---|---|---|
| Identification/gathering of evidence | Technical | Implement advanced data collection tools and techniques for efficient evidence gathering. |
| Architectural support | Technical | Develop forensic tools that are compatible with various cloud architectures. |
| Data privacy and security | Technical | Utilize strong encryption methods and access controls to protect data integrity and confidentiality. |
| Protecting evidence | Technical | Establish secure storage mechanisms and access controls to prevent tampering with evidence. |
| Customer’s knowledge and lack of control | Resource | Provide training and education to users to enhance their understanding of cloud security best practices. |
| Restricted authority over access | Resource | Implement role-based access controls and privilege management to restrict unauthorized access. |
| Accuracy | Resource | Implement data validation and integrity checks to ensure the accuracy of forensic findings. |
| Duplication of data | Resource | Establish data deduplication processes to eliminate redundant data and improve storage efficiency. |
| Absence of analysis and collection of evidence | Legal | Establish clear legal procedures for evidence collection and analysis in cloud environments. |
| Integrity | Legal | Ensure data integrity throughout the forensic investigation process to maintain the credibility of evidence. |
| Multi-tenants | Legal | Develop protocols for handling data from multiple tenants in shared cloud environments to prevent data leakage. |
| Privacy | Legal | Implement privacy-enhancing technologies and policies to protect sensitive information during investigations. |
| The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
Share and Cite
Alshabibi, M.M.; Bu dookhi, A.K.; Hafizur Rahman, M.M. Forensic Investigation, Challenges, and Issues of Cloud Data: A Systematic Literature Review. Computers 2024 , 13 , 213. https://doi.org/10.3390/computers13080213
Alshabibi MM, Bu dookhi AK, Hafizur Rahman MM. Forensic Investigation, Challenges, and Issues of Cloud Data: A Systematic Literature Review. Computers . 2024; 13(8):213. https://doi.org/10.3390/computers13080213
Alshabibi, Munirah Maher, Alanood Khaled Bu dookhi, and M. M. Hafizur Rahman. 2024. "Forensic Investigation, Challenges, and Issues of Cloud Data: A Systematic Literature Review" Computers 13, no. 8: 213. https://doi.org/10.3390/computers13080213
Article Metrics
Article access statistics, further information, mdpi initiatives, follow mdpi.

Subscribe to receive issue release notifications and newsletters from MDPI journals

- Cloud Computing
Top 10 Cloud Computing Research Topics of 2024
Home Blog Cloud Computing Top 10 Cloud Computing Research Topics of 2024
Cloud computing is a fast-growing area in the technical landscape due to its recent developments. If we look ahead to 2024, there are new research topics in cloud computing that are getting more traction among researchers and practitioners. Cloud computing has ranged from new evolutions on security and privacy with the use of AI & ML usage in the Cloud computing for the new cloud-based applications for specific domains or industries. In this article, we will investigate some of the top cloud computing research topics for 2024 and explore what we get most out of it for researchers or cloud practitioners. To master a cloud computing field, we need to check these Cloud Computing online courses .
Why Cloud Computing is Important for Data-driven Business?
The Cloud computing is crucial for data-driven businesses because it provides scalable and cost-effective ways to store and process huge amounts of data. Cloud-based storage and analytical platform helps business to easily access their data whenever required irrespective of where it is located physically. This helps businesses to take good decisions about their products and marketing plans.
Cloud computing could help businesses to improve their security in terms of data, Cloud providers offer various features such as data encryption and access control to their customers so that they can protect the data as well as from unauthorized access.
Few benefits of Cloud computing are listed below:
- Scalability: With Cloud computing we get scalable applications which suits for large scale production systems for Businesses which store and process large sets of data.
- Cost-effectiveness : It is evident that Cloud computing is cost effective solution compared to the traditional on-premises data storage and analytical solutions due to its scaling capacity which leads to saving more IT costs.
- Security : Cloud providers offer various security features which includes data encryption and access control, that can help businesses to protect their data from unauthorized access.
- Reliability : Cloud providers ensure high reliability to their customers based on their SLA which is useful for the data-driven business to operate 24X7.
Top 10 Cloud Computing Research Topics
1. neural network based multi-objective evolutionary algorithm for dynamic workflow scheduling in cloud computing.
Cloud computing research topics are getting wider traction in the Cloud Computing field. These topics in the paper suggest a multi-objective evolutionary algorithm (NN-MOEA) based on neural networks for dynamic workflow scheduling in cloud computing. Due to the dynamic nature of cloud resources and the numerous competing objectives that need to be optimized, scheduling workflows in cloud computing is difficult. The NN-MOEA algorithm utilizes neural networks to optimize multiple objectives, such as planning, cost, and resource utilization. This research focuses on cloud computing and its potential to enhance the efficiency and effectiveness of businesses' cloud-based workflows.
The algorithm predicts workflow completion time using a feedforward neural network based on input and output data sizes and cloud resources. It generates a balanced schedule by taking into account conflicting objectives and projected execution time. It also includes an evolutionary algorithm for future improvement.
The proposed NN-MOEA algorithm has several benefits, such as the capacity to manage dynamic changes in cloud resources and the capacity to simultaneously optimize multiple objectives. The algorithm is also capable of handling a variety of workflows and is easily expandable to include additional goals. The algorithm's use of neural networks to forecast task execution times is a crucial component because it enables the algorithm to generate better schedules and more accurate predictions.
The paper concludes by presenting a novel multi-objective evolutionary algorithm-based neural network-based approach to dynamic workflow scheduling in cloud computing. In terms of optimizing multiple objectives, such as make span and cost, and achieving a better balance between them, these cloud computing dissertation topics on the proposed NN-MOEA algorithm exhibit encouraging results.
Key insights and Research Ideas:
Investigate the use of different neural network architectures for predicting the future positions of optimal solutions. Explore the use of different multi-objective evolutionary algorithms for solving dynamic workflow scheduling problems. Develop a cloud-based workflow scheduling platform that implements the proposed algorithm and makes it available to researchers and practitioners.
2. A systematic literature review on cloud computing security: threats and mitigation strategies
This is one of cloud computing security research topics in the cloud computing paradigm. The authors then provide a systematic literature review of studies that address security threats to cloud computing and mitigation techniques and were published between 2010 and 2020. They list and classify the risks and defense mechanisms covered in the literature, as well as the frequency and distribution of these subjects over time.
The paper suggests the data breaches, Insider threats and DDoS attack are most discussed threats to the security of cloud computing. Identity and access management, encryption, and intrusion detection and prevention systems are the mitigation techniques that are most frequently discussed. Authors depict the future trends of machine learning and artificial intelligence might help cloud computing to mitigate its risks.
The paper offers a thorough overview of security risks and mitigation techniques in cloud computing, and it emphasizes the need for more research and development in this field to address the constantly changing security issues with cloud computing. This research could help businesses to reduce the amount of spam that they receive in their cloud-based email systems.
Explore the use of blockchain technology to improve the security of cloud computing systems. Investigate the use of machine learning and artificial intelligence to detect and prevent cloud computing attacks. Develop new security tools and technologies for cloud computing environments.
3. Spam Identification in Cloud Computing Based on Text Filtering System
A text filtering system is suggested in the paper "Spam Identification in Cloud Computing Based on Text Filtering System" to help identify spam emails in cloud computing environments. Spam emails are a significant issue in cloud computing because they can use up computing resources and jeopardize the system's security.
To detect spam emails, the suggested system combines text filtering methods with machine learning algorithms. The email content is first pre-processed by the system, which eliminates stop words and stems the remaining words. The preprocessed text is then subjected to several filters, including a blacklist filter and a Bayesian filter, to identify spam emails.
In order to categorize emails as spam or non-spam based on their content, the system also employs machine learning algorithms like decision trees and random forests. The authors use a dataset of emails gathered from a cloud computing environment to train and test the system. They then assess its performance using metrics like precision, recall, and F1 score.
The findings demonstrate the effectiveness of the proposed system in detecting spam emails, achieving high precision and recall rates. By contrasting their system with other spam identification systems, the authors also show how accurate and effective it is.
The method presented in the paper for locating spam emails in cloud computing environments has the potential to improve the overall security and performance of cloud computing systems. This is one of the interesting clouds computing current research topics to explore and innovate. This is one of the good Cloud computing research topics to protect the Mail threats.
Create a stronger spam filtering system that can recognize spam emails even when they are made to avoid detection by more common spam filters. examine the application of artificial intelligence and machine learning to the evaluation of spam filtering system accuracy. Create a more effective spam filtering system that can handle a lot of emails quickly and accurately.
4. Blockchain data-based cloud data integrity protection mechanism
The "Blockchain data-based cloud data integrity protection mechanism" paper suggests a method for safeguarding the integrity of cloud data and which is one of the Cloud computing research topics. In order to store and process massive amounts of data, cloud computing has grown in popularity, but issues with data security and integrity still exist. For the proposed mechanism to guarantee the availability and integrity of cloud data, data redundancy and blockchain technology are combined.
A data redundancy layer, a blockchain layer, and a verification and recovery layer make up the mechanism. For availability in the event of server failure, the data redundancy layer replicates the cloud data across multiple cloud servers. The blockchain layer stores the metadata (such as access rights) and hash values of the cloud data and access control information
Using a dataset of cloud data, the authors assess the performance of the suggested mechanism and compare it to other cloud data protection mechanisms. The findings demonstrate that the suggested mechanism offers high levels of data availability and integrity and is superior to other mechanisms in terms of processing speed and storage space.
Overall, the paper offers a promising strategy for using blockchain technology to guarantee the availability and integrity of cloud data. The suggested mechanism may assist in addressing cloud computing's security issues and enhancing the dependability of cloud data processing and storage. This research could help businesses to protect the integrity of their cloud-based data from unauthorized access and manipulation.
Create a data integrity protection system based on blockchain that is capable of detecting and preventing data tampering in cloud computing environments. For enhancing the functionality and scalability of blockchain-based data integrity protection mechanisms, look into the use of various blockchain consensus algorithms. Create a data integrity protection system based on blockchain that is compatible with current cloud computing platforms. Create a safe and private data integrity protection system based on blockchain technology.
5. A survey on internet of things and cloud computing for healthcare
This article suggests how recent tech trends like the Internet of Things (IoT) and cloud computing could transform the healthcare industry. It is one of the Cloud computing research topics. These emerging technologies open exciting possibilities by enabling remote patient monitoring, personalized care, and efficient data management. This topic is one of the IoT and cloud computing research papers which aims to share a wider range of information.
The authors categorize the research into IoT-based systems, cloud-based systems, and integrated systems using both IoT and the cloud. They discussed the pros of real-time data collection, improved care coordination, automated diagnosis and treatment.
However, the authors also acknowledge concerns around data security, privacy, and the need for standardized protocols and platforms. Widespread adoption of these technologies faces challenges in ensuring they are implemented responsibly and ethically. To begin the journey KnowledgeHut’s Cloud Computing online course s are good starter for beginners so that they can cope with Cloud computing with IOT.
Overall, the paper provides a comprehensive overview of this rapidly developing field, highlighting opportunities to revolutionize how healthcare is delivered. New devices, systems and data analytics powered by IoT, and cloud computing could enable more proactive, preventative and affordable care in the future. But careful planning and governance will be crucial to maximize the value of these technologies while mitigating risks to patient safety, trust and autonomy. This research could help businesses to explore the potential of IoT and cloud computing to improve healthcare delivery.
Examine how IoT and cloud computing are affecting patient outcomes in various healthcare settings, including hospitals, clinics, and home care. Analyze how well various IoT devices and cloud computing platforms perform in-the-moment patient data collection, archival, and analysis. assessing the security and privacy risks connected to IoT devices and cloud computing in the healthcare industry and developing mitigation strategies.
6. Targeted influence maximization based on cloud computing over big data in social networks
Big data in cloud computing research papers are having huge visibility in the industry. The paper "Targeted Influence Maximization based on Cloud Computing over Big Data in Social Networks" proposes a targeted influence maximization algorithm to identify the most influential users in a social network. Influence maximization is the process of identifying a group of users in a social network who can have a significant impact or spread information.
A targeted influence maximization algorithm is suggested in the paper "Targeted Influence maximization based on Cloud Computing over Big Data in Social Networks" to find the most influential users in a social network. The process of finding a group of users in a social network who can make a significant impact or spread information is known as influence maximization.
Four steps make up the suggested algorithm: feature extraction, classification, influence maximization, and data preprocessing. The authors gather and preprocess social network data, such as user profiles and interaction data, during the data preprocessing stage. Using machine learning methods like text mining and sentiment analysis, they extract features from the data during the feature extraction stage. Overall, the paper offers a promising strategy for maximizing targeted influence using big data and Cloud computing research topics to look into. The suggested algorithm could assist companies and organizations in pinpointing their marketing or communication strategies to reach the most influential members of a social network.
Key insights and Research Ideas:
Develop a cloud-based targeted influence maximization algorithm that can effectively identify and influence a small number of users in a social network to achieve a desired outcome. Investigate the use of different cloud computing platforms to improve the performance and scalability of cloud-based targeted influence maximization algorithms. Develop a cloud-based targeted influence maximization algorithm that is compatible with existing social network platforms. Design a cloud-based targeted influence maximization algorithm that is secure and privacy-preserving.
7. Security and privacy protection in cloud computing: Discussions and challenges
Cloud computing current research topics are getting traction, this is of such topic which provides an overview of the challenges and discussions surrounding security and privacy protection in cloud computing. The authors highlight the importance of protecting sensitive data in the cloud, with the potential risks and threats to data privacy and security. The article explores various security and privacy issues that arise in cloud computing, including data breaches, insider threats, and regulatory compliance.
The article explores challenges associated with implementing these security measures and highlights the need for effective risk management strategies. Azure Solution Architect Certification course is suitable for a person who needs to work on Azure cloud as an architect who will do system design with keep security in mind.
Final take away of cloud computing thesis paper by an author points out by discussing some of the emerging trends in cloud security and privacy, including the use of artificial intelligence and machine learning to enhance security, and the emergence of new regulatory frameworks designed to protect data in the cloud and is one of the Cloud computing research topics to keep an eye in the security domain.
Develop a more comprehensive security and privacy framework for cloud computing. Explore the options with machine learning and artificial intelligence to enhance the security and privacy of cloud computing. Develop more robust security and privacy mechanisms for cloud computing. Design security and privacy policies for cloud computing that are fair and transparent. Educate cloud users about security and privacy risks and best practices.
8. Intelligent task prediction and computation offloading based on mobile-edge cloud computing
This Cloud Computing thesis paper "Intelligent Task Prediction and Computation Offloading Based on Mobile-Edge Cloud Computing" proposes a task prediction and computation offloading mechanism to improve the performance of mobile applications under the umbrella of cloud computing research ideas.
An algorithm for offloading computations and a task prediction model makes up the two main parts of the suggested mechanism. Based on the mobile application's usage patterns, the task prediction model employs machine learning techniques to forecast its upcoming tasks. This prediction is to decide whether to execute a specific task locally on the mobile device or offload the computation of it to the cloud.
Using a dataset of mobile application usage patterns, the authors assess the performance of the suggested mechanism and compare it to other computation offloading mechanisms. The findings demonstrate that the suggested mechanism performs better in terms of energy usage, response time, and network usage.
The authors also go over the difficulties in putting the suggested mechanism into practice, including the need for real-time task prediction and the trade-off between offloading computation and network usage. Additionally, they outline future research directions for mobile-edge cloud computing applications, including the use of edge caching and the integration of blockchain technology for security and privacy.
Overall, the paper offers a promising strategy for enhancing mobile application performance through mobile-edge cloud computing. The suggested mechanism might improve the user experience for mobile users while lowering the energy consumption and response time of mobile applications. These Cloud computing dissertation topic leads to many innovation ideas.
Develop an accurate task prediction model considering mobile device and cloud dynamics. Explore machine learning and AI for efficient computation offloading. Create a robust framework for diverse tasks and scenarios. Design a secure, privacy-preserving computation offloading mechanism. Assess computation offloading effectiveness in real-world mobile apps.
9. Cloud Computing and Security: The Security Mechanism and Pillars of ERPs on Cloud Technology
Enterprise resource planning (ERP) systems are one of the Cloud computing research topics in particular face security challenges with cloud computing, and the paper "Cloud Computing and Security: The Security Mechanism and Pillars of ERPs on Cloud Technology" discusses these challenges and suggests a security mechanism and pillars for protecting ERP systems on cloud technology.
The authors begin by going over the benefits of ERP systems and cloud computing as well as the security issues with cloud computing, like data breaches and insider threats. They then go on to present a security framework for cloud-based ERP systems that is built around four pillars: access control, data encryption, data backup and recovery, and security monitoring. The access control pillar restricts user access, while the data encryption pillar secures sensitive data. Data backup and recovery involve backing up lost or failed data. Security monitoring continuously monitors the ERP system for threats. The authors also discuss interoperability challenges and the need for standardization in securing ERP systems on the cloud. They propose future research directions, such as applying machine learning and artificial intelligence to security analytics.
Overall, the paper outlines a thorough strategy for safeguarding ERP systems using cloud computing and emphasizes the significance of addressing security issues related to this technology. Organizations can protect their ERP systems and make sure the Security as well as privacy of their data by implementing these security pillars and mechanisms.
Investigate the application of blockchain technology to enhance the security of cloud-based ERP systems. Look into the use of machine learning and artificial intelligence to identify and stop security threats in cloud-based ERP systems. Create fresh security measures that are intended only for cloud-based ERP systems. By more effectively managing access control and data encryption, cloud-based ERP systems can be made more secure. Inform ERP users about the security dangers that come with cloud-based ERP systems and how to avoid them.

10. Optimized data storage algorithm of IoT based on cloud computing in distributed system
The article proposes an optimized data storage algorithm for Internet of Things (IoT) devices which runs on cloud computing in a distributed system. In IoT apps, which normally generate huge amounts of data by various devices, the algorithm tries to increase the data storage and faster retrials of the same.
The algorithm proposed includes three main components: Data Processing, Data Storage, and Data Retrieval. The Data Processing module preprocesses IoT device data by filtering or compressing it. The Data Storage module distributes the preprocessed data across cloud servers using partitioning and stores it in a distributed database. The Data Retrieval module efficiently retrieves stored data in response to user queries, minimizing data transmission and enhancing query efficiency. The authors evaluated the algorithm's performance using an IoT dataset and compared it to other storage and retrieval algorithms. Results show that the proposed algorithm surpasses others in terms of storage effectiveness, query response time, and network usage.
They suggest future directions such as leveraging edge computing and blockchain technology for optimizing data storage and retrieval in IoT applications. In conclusion, the paper introduces a promising method to improve data archival and retrieval in distributed cloud based IoT applications, enhancing the effectiveness and scalability of IoT applications.
Create a data storage algorithm capable of storing and managing large amounts of IoT data efficiently. Examine the use of cloud computing to improve the performance and scalability of data storage algorithms for IoT. Create a secure and privacy-preserving data storage algorithm. Assess the performance and effectiveness of data storage algorithms for IoT in real-world applications.
How to Write a Perfect Research Paper?
- Choose a topic: Select the topic which is interesting to you so that you can share things with the viewer seamlessly with good content.
- Do your research: Read books, articles, and websites on your topic. Take notes and gather evidence to support your arguments.
- Write an outline: This will help you organize your thoughts and make sure your paper flows smoothly.
- Start your paper: Start with an introduction that grabs the reader's attention. Then, state your thesis statement and support it with evidence from your research. Finally, write a conclusion that summarizes your main points.
- Edit and proofread your paper. Make sure you check the grammatical errors and spelling mistakes.
Cloud computing is a rapidly evolving area with more interesting research topics being getting traction by researchers and practitioners. Cloud providers have their research to make sure their customer data is secured and take care of their security which includes encryption algorithms, improved access control and mitigating DDoS – Deniel of Service attack etc.,
With the improvements in AI & ML, a few features developed to improve the performance, efficiency, and security of cloud computing systems. Some of the research topics in this area include developing new algorithms for resource allocation, optimizing cloud workflows, and detecting and mitigating cyberattacks.
Cloud computing is being used in industries such as healthcare, finance, and manufacturing. Some of the research topics in this area include developing new cloud-based medical imaging applications, building cloud-based financial trading platforms, and designing cloud-based manufacturing systems.
Frequently Asked Questions (FAQs)
Data security and privacy problems, vendor lock-in, complex cloud management, a lack of standardization, and the risk of service provider disruptions are all current issues in cloud computing. Because data is housed on third-party servers, data security and privacy are key considerations. Vendor lock-in makes transferring providers harder and increases reliance on a single one. Managing many cloud services complicates things. Lack of standardization causes interoperability problems and restricts workload mobility between providers.
Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS) are the cloud computing scenarios where industries focusing right now.
The six major components of cloud infrastructure are compute, storage, networking, security, management and monitoring, and database. These components enable cloud-based processing and execution, data storage and retrieval, communication between components, security measures, management and monitoring of the infrastructure, and database services.

Vinoth Kumar P
Vinoth Kumar P is a Cloud DevOps Engineer at Amadeus Labs. He has over 7 years of experience in the IT industry, and is specialized in DevOps, GitOps, DevSecOps, MLOps, Chaos Engineering, Cloud and Cloud Native landscapes. He has published articles and blogs on recent tech trends and best practices on GitHub, Medium, and LinkedIn, and has delivered a DevSecOps 101 talk to Developers community , GitOps with Argo CD Webinar for DevOps Community. He has helped multiple enterprises with their cloud migration, cloud native design, CICD pipeline setup, and containerization journey.
Avail your free 1:1 mentorship session.
Something went wrong
Upcoming Cloud Computing Batches & Dates
| Name | Date | Fee | Know more |
|---|
- Trending Now
- Foundational Courses
- Data Science
- Practice Problem
- Machine Learning
- System Design
- DevOps Tutorial
Top 15 Cloud Computing Research Topics in 2024
Cloud computing has suddenly seen a spike in employment opportunities around the globe with tech giants like Amazon , Google , and Microsoft hiring people for their cloud infrastructure . Before the onset of cloud computing , companies and businesses had to set up their own data centers , and allocate resources and other IT professionals thereby increasing the cost. The rapid development of the cloud has led to more flexibility , cost-cutting , and scalability .

The Cloud Computing market is at an all-time high with the current market size at USD 371.4 billion and is expected to grow up to USD 832.1 billion by 2025 ! It’s quickly evolving and gradually realizing its business value along with attracting more and more researchers , scholars , computer scientists , and practitioners. Cloud computing is not a single topic but a composition of various techniques which together constitute the cloud . Below are 10 of the most demanded research topics in the field of cloud computing .
What is Cloud Computing?
Cloud computing is the practice of storing and accessing data and applications on remote servers hosted over the internet, as opposed to local servers or the computer’s hard drive. Cloud computing, often known as Internet-based computing, is a technique in which the user receives a resource as a service via the Internet. Files, photos, documents, and other storable documents can all be considered types of data that are stored.
Let us look at the latest in cloud computing research for 2024! We’ve compiled 15 important cloud computing research topics that are changing how cloud computing is used.
1. Big Data
Big data refers to the large amounts of data produced by various programs in a very short duration of time. It is quite cumbersome to store such huge and voluminous amounts of data in company-run data centers . Also, gaining insights from this data becomes a tedious task and takes a lot of time to run and provide results, therefore cloud is the best option. All the data can be pushed onto the cloud without the need for physical storage devices that are to be managed and secured. Also, some popular public clouds provide comprehensive big data platforms to turn data into actionable insights.
DevOps is an amalgamation of two terms, Development and Operations . It has led to Continuous Delivery , Integration, and Deployment therefore reducing boundaries between the development team and the operations team . Heavy applications and software need elaborate and complex tech stacks that demand extensive labor to develop and configure which can easily be eliminated by cloud computing . It offers a wide range of tools and technologies to build , test , and deploy applications within a few minutes and a single click. They can be customized as per the client’s requirements and can be discarded when not in use hence making the process seamless and cost-efficient for development teams .
3. Cloud Cryptography
Data in the cloud needs to be protected and secured from foreign attacks and breaches . To accomplish this, cryptography in the cloud is a widely used technique to secure data present in the cloud . It allows users and clients to easily and reliably access the shared cloud services since all the data is secured using either encryption techniques or by using the concept of the private key . It can make the plain text unreadable and limit the view of the data being transferred. Best cloud cryptographic security techniques are the ones that do not compromise the speed of data transfer and provide security without delaying the exchange of sensitive data.
4. Cloud Load Balancing
It refers to splitting and distributing the incoming load to the server from various sources. It permits companies and organizations to govern and supervise workload demands or application demands by redistributing, reallocating, and administering resources between different computers, networks, or servers. Cloud load balancing encompasses holding the circulation of traffic and demands that exist over the Internet. This reduces the problem of sudden outages, results in an improvement in overall performance, has rare chances of server crashes and also provides an advanced level of security. Cloud-based server farms can accomplish more precise scalability and accessibility using the server load balancing mechanism . Due to this, the workload demands can be easily distributed and controlled.
5. Mobile Cloud Computing
It is a mixture of cloud computing , mobile computing , and wireless network to provide services such as seamless and abundant computational resources to mobile users, network operators, and cloud computing professionals. The handheld device is the console and all the processing and data storage takes place outside the physical mobile device. Some advantages of using mobile cloud computing are that there is no need for costly hardware, battery life is longer, extended data storage capacity and processing power, improved synchronization of data, and high availability due to “store in one place, accessible from anywhere”. The integration and security aspects are taken care of by the backend that enables support to an abundance of access methods.
6. Green Cloud Computing
The major challenge in the cloud is the utilization of energy-efficient and hence develop economically friendly cloud computing solutions. Data centers that include servers , cables , air conditioners , networks , etc. in large numbers consume a lot of power and release enormous quantities of Carbon Dioxide in the atmosphere. Green Cloud Computing focuses on making virtual data centers and servers to be more environmentally friendly and energy-efficient. Cloud resources often consume so much power and energy leading to a shortage of energy and affecting the global climate. Green cloud computing provides solutions to make such resources more energy efficient and to reduce operational costs. This pivots on power management , virtualization of servers and data centers, recycling vast e-waste , and environmental sustainability .
7. Edge Computing
It is the advancement and a much more efficient form of Cloud computing with the idea that the data is processed nearer to the source. Edge Computing states that all of the computation will be carried out at the edge of the network itself rather than on a centrally managed platform or data warehouse. Edge computing distributes various data processing techniques and mechanisms across different positions. This makes the data deliverable to the nearest node and the processing at the edge . This also increases the security of the data since it is closer to the source and eliminates late response time and latency without affecting productivity
8. Containerization
Containerization in cloud computing is a procedure to obtain operating system virtualization . The user can work with a program and its dependencies utilizing remote resource procedures . The container in cloud computing is used to construct blocks, which aid in producing operational effectiveness , version control , developer productivity , and environmental stability . The infrastructure is upgraded since it provides additional control over the granular activities of the resources. The usage of containers in online services assists storage with cloud computing data security, elasticity, and availability. Containers provide certain advantages such as a steady runtime environment , the ability to run virtually anywhere, and the low overhead compared to virtual machines .
9. Cloud Deployment Model
There are four main cloud deployment models namely public cloud , private cloud , hybrid cloud , and community cloud . Each deployment model is defined as per the location of the infrastructure. The public cloud allows systems and services to be easily accessible to the general public . The public cloud could also be less reliable since it is open to everyone e.g. Email. A private cloud allows systems and services to be accessible inside an organization with no access to outsiders. It offers better security due to its access restrictions. A hybrid cloud is a mixture of private and public clouds with critical activities being performed using the private cloud and non-critical activities being performed using the public cloud. Community cloud allows systems and services to be accessible by a group of organizations.
10. Cloud Security
Since the number of companies and organizations using cloud computing is increasing at a rapid rate, the security of the cloud is a major concern. Cloud computing security detects and addresses every physical and logical security issue that comes across all the varied service models of code, platform, and infrastructure. It collectively addresses these services, however, these services are delivered in units, that is, the public, private, or hybrid delivery model. Security in the cloud protects the data from any leakage or outflow, theft, calamity, and removal. With the help of tokenization, Virtual Private Networks , and firewalls , data can be secured.
11. Serverless Computing
Serverless computing is a way of running computer programs without having to manage the underlying infrastructure. Instead of worrying about servers, networking, and scaling, you can focus solely on writing code to solve your problem. In serverless computing, you write small pieces of code called functions. These functions are designed to do specific tasks, like processing data, handling user requests, or performing calculations. When something triggers your function, like a user making a request to your website or a timer reaching a certain time, the cloud provider automatically runs your function for you. You don’t have to worry about setting up servers or managing resources.
12. Cloud-Native Applications
Modern applications built for the cloud , also known as cloud-native applications , are made so to take full advantage of cloud computing environments . Instead of bulky programs like monolithic systems , they’re built to prioritize flexibility , easy scaling , reliability , and constant updates . This modular approach allows them to adapt to changing needs by growing or shrinking on demand, making them perfect for the ever-shifting world of cloud environments. Deployed in various cloud environments like public, private, or hybrid clouds, they’re optimized to make the most of cloud-native technologies and methodologies . Instead of one big chunk, they’re made up of lots of smaller pieces called microservices .
13. Multi-Cloud Management
Multi-cloud management means handling and controlling your stuff (like software, data, and services) when they’re spread out across different cloud companies, like Amazon, Google, or Microsoft. It’s like having a central command center for your cloud resources spread out across different cloud services. Multi-cloud gives you the freedom to use the strengths of different cloud providers. You can choose the best service for each specific workload, based on factors like cost, performance, or features. This flexibility allows you to easily scale your applications up or down as required by you. Managing a complex environment with resources spread across multiple cloud providers can be a challenge. Multi-cloud management tools simplify this process by providing a unified view and standardized management interface.
14. Blockchain in Cloud Computing
Cloud computing provides flexible storage and processing power that can grow or shrink as needed. Blockchain keeps data secure by spreading it across many computers. When we use them together, blockchain apps can use the cloud’s power for big tasks while keeping data safe and transparent. This combo boosts cloud data security and makes it easy to track data. It also lets people manage their identities without a central authority. However, there are challenges like making sure different blockchain and cloud systems work well together and can handle large amounts of data.
15. Cloud-Based Internet of Things (IoT)
Cloud-based Internet of Things (IoT) refers to the integration of cloud computing with IoT devices and systems. This integration allows IoT devices to leverage the computational power, storage, and analytics capabilities of cloud platforms to manage, process, and analyze the vast amounts of data they generate. The cloud serves as a central hub for connecting and managing multiple IoT devices, regardless of their geographical location. This connectivity is crucial for monitoring and controlling devices remotely.
Also Read Cloud computing Research challenges 7 Privacy Challenges in Cloud Computing Difference Between Cloud Computing and Fog Computing
Cloud computing has helped businesses grow by offering greater scalability , flexibility , and saving money by charging less money for the same job. As cloud computing is having a great growth period right now, it has created lots of employment opportunities and research work is done is different areas which is changing the future of this technology. We have discussed about the top 15 cloud computing research topics . You can try to explore and research in these areas to contribute to the growth of cloud computing technology .

Please Login to comment...
Similar reads.
- Cloud-Computing
- How to Get a Free SSL Certificate
- Best SSL Certificates Provider in India
- Elon Musk's xAI releases Grok-2 AI assistant
- What is OpenAI SearchGPT? How it works and How to Get it?
- Content Improvement League 2024: From Good To A Great Article
Improve your Coding Skills with Practice
What kind of Experience do you want to share?
Securing data and preserving privacy in cloud IoT-based technologies an analysis of assessing threats and developing effective safeguard
- Open access
- Published: 27 August 2024
- Volume 57 , article number 269 , ( 2024 )
Cite this article
You have full access to this open access article

- Mayank Pathak 1 ,
- Kamta Nath Mishra 1 &
- Satya Prakash Singh 1
1 Altmetric
The Internet of Things (IoT) is a powerful technology adopted in various industries. Applications of the IoT aim to enhance automation, productivity, and user comfort in a cloud and distributive computing environment. Cloud computing automatically stores and analyzes the large amounts of data generated by IoT-based applications. Cloud computing has become a crucial component of the information age through easier data administration and storage. Currently, government agencies, commercial enterprises, and end users are rapidly migrating their data to cloud environments. This may require end-user authentication, greater safety, and data recovery in the event of an attack. A few issues were discovered by authors after analysis and assessments of various aspects of the published research papers. The research analysis reveals that the existing methods need to be further improved to address the contemporary dangers related to data security and privacy. Based on the research reports, it can be stated that safe end-to-end data transmission in a cloud-IoT environment requires modifications and advancements in the design of reliable protocols. Upcoming technologies like blockchain, machine learning, fog, and edge computing mitigate data over the cloud to some level. The study provides a thorough analysis of security threats including their categorization, and potential countermeasures to safeguard our cloud-IoT data. Additionally, the authors have summarized cutting-edge approaches like machine learning and blockchain technologies being used in the data security privacy areas. Further, this paper discusses the existing problems related to data privacy and security in the cloud-IoT environment in today’s world and their possible future directions.
Explore related subjects
- Artificial Intelligence
Avoid common mistakes on your manuscript.
1 Introduction
The speedy development of technology and Internet of Things (IoT)-based devices in organizations and enterprises give rise to progressive increases in various types of data. IoT has become a vital part of human life and it can be sensed in our day-to-day activities. It was said by Kumar et al. ( 2019 ) that IoT is a revolutionary approach that has changed numerous aspects of human life. It makes our lives easy and secure by handling various applications of smart city societies including pollution control , smart transportation , smart industries , smart home security systems , smart water supply , and many more systems. The small amount of data accumulates and gives rise to Big Data which is stored, processed, and analyzed by a set of technologies. Big Data is a large volume of data generated by IoT sensors , servers , social media , and medical equipment, etc . Cloud computing is internet-based computing that enables inexpensive, reliable, easy, simple, and convenient accessibility to the resource (Albugmi et al. 2016 ). Cloud computing provides service, and reduces infrastructure maintenance overheads. Apart from this it also provides better performance to the end users and flexibility for storing data over the cloud. However, storing highly confidential Big Data obtained from IoT devices , medical data , and server data over the cloud may pose threats to attackers. Therefore, data security is a most important concern when a large or bulk of confidential data is to be stored in the cloud (Sumithra and Parameswari 2022 ).
Cyber attacks target IoT devices that impact stakeholders, and they may damage physical systems, m-health, and economic systems severely. Earlier events show that IoT devices hold numerous vulnerabilities. Many manufacturers struggle to protect IoT devices from vulnerabilities (Schiller et al. 2022a ). Cloud computing integrates distributed computing, grid computing, and utility computing to establish a shared virtual resource pool (Sun 2019 ). There are privacy and security issues in these cases because the owners have no control over the information and tasks carried out on the platform. Various privacy protection methods have been introduced such as encryption , access control , cryptography , and digital signature but they are not strong enough, as a result, attackers easily break through the security wall and harm the data over the cloud.
The authors of the research papers reviewed various methods and suggested some measures and directions to protect the data in cloud computing and edge computing environments (Ravi Kumar et al. 2018 ; Zhang et al. 2018 ). Through this study, the author found that data privacy , data remoteness , data leakage , and data segregation are crucial problems that may exist. The survey paper (Hong-Yen and Jiankun 2019 ) addressed modern privacy and preserving models to focus on numerous privacy-interrelated frameworks to be implemented in practice.
As a contribution, the current paper aims to accomplish the following objectives:
To examine existing security frameworks , standards , and techniques that incorporate different standards across multiple areas of cloud-IoT technologies.
To explore and discuss open-ended challenges in a Cloud-IoT-based environment concerning securities and privacy.
To present and discuss the classification of challenges in Cloud-IoT environments after evaluating the performance of existing literature. It also provides solutions for the identified open-ended challenges and addresses future security concerns related to Cloud-IoT technologies.
The following are the Research Questions ( RQs ) that the researchers tried to investigate through the current research paper:
RQ 1 : To Investigate how IoT , Big Data , and Cloud computing technologies are interconnected, and how security can be a major concern when data is stored in a cloud environment.
RQ 2 : What are the security objectives for the data security and privacy domain?
RQ 3 : What are the privacy concerns for end-users in cloud-IoT-based environments?
RQ 4 : What is the role of edge computing in enhancing privacy in a cloud-IoT environment?
RQ 5 : What are vulnerabilities that exist in the cloud-IoT infrastructure?
RQ 6 : What are the current research trends and areas of focus?
RQ 7 : What are Advancements in security threat detection and avoidance ?
RQ 8 : How machine learning can be a useful tool in detecting vulnerabilities within a cloud-IoT environment?
RQ 9 : How can blockchain technology be an effective measure of data security and privacies?
RQ 10 : What are Current Issues in Data Security and Privacy?
Regarding the remaining portion of the document, Sect. 2 describes the methodology of this research work. Section 3 discusses the characteristics of a research paper and explains how the current paper differs from others. Section 4 talks about security goals in the Cloud-IoT environment. Section 5 discusses the taxonomy related to Cloud-IoT environment which includes Big Data and IoT along with its applications in various domains. Section 6 is a comprehensive study of various attacks in the Cloud-IoT environment. Section 7 (A) explores the study of various research trends through Table 1 . Section 7 (B) describes attack vectors and mitigation strategies through Table 2 . Section 8 presents an in-depth analysis of digital forensics. Section 9 talks about the machine learning and Blockchain technologies-based approaches used for threat detection and recovery. Section 10 covers the current challenges in data security and privacy, and it provides a brief description of possible solutions listed in Table 3 . Further, this section highlights the research gaps identified by the author in Table 4 . Conclusions and future research work are discussed in Sect. 11 .
2 Methodology: a systematic approach
The methodology is the systematic approach that is used by the author to conduct research, analyze the data, and frame conclusions. The methodology section covers the boundary area of methods and approaches that are followed by the author to write the current research paper. The methodology of this research paper is as follows: To examine IoT security challenges and threats author searched numerous kinds of literature on IoT security. For this keyword IoT, Cloud-IoT security was used for standard survey papers that were published in reputed journals like IEEE, Elsevier, Springer, and many more. After completing this task, the author examined numerous techniques and methodologies presented in those survey papers critically analyzed the facts, and algorithms, and selected a set of relevant topics that is important from a security perspective, provided with the help of the author’s individual experience in the sphere of security. In addition to this, the author introduced various standard approaches that are recognized in the sphere of security for protection against threats. At last, the author utilized Internet-based search techniques to find the most appropriate security products. The Methodology of the current paper is divided into three standard stages as follows.
Phase 1 Identification of the study area, formulation of the research questions, sampling, and establishing the primary search approach or standards.
Phase 2 Using the search strategy or criterion about existing literature, carrying out keyword searches, Boolean searches involving the combination of keywords and phrases with the operators “AND”, and “OR”, and database searches, assessing the results, and formulating selection criteria.
Phase 3 Finding and evaluating approved literature, articles, papers, websites, and web documents by the chosen primary research topic.
Figure 1 shows the distribution of references over the year. The figure portrays which year the researcher’s paper was selected to prepare the current paper. The author selected the previous research paper from year 2016 to 2024, a recently published paper. The author reviewed the paper which includes published journal and conference papers. The author searched, examined, and analyzed the paper was included in the references section of the manuscript.
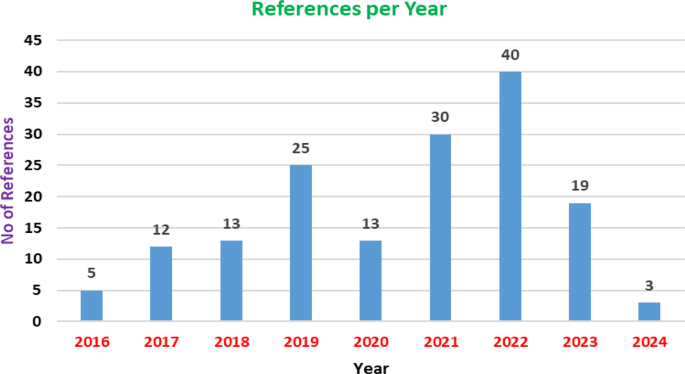
Reference timeline
2.1 Inclusion/exclusion criteria
The inclusion and exclusion criteria aim to identify the research studies that correspond with the questions under investigation. The primary studies were identified using the inclusion criteria that we are presenting. The exclusion criteria were left out since they represent the negative version of the inclusion criteria that were specified.
Inclusion Criteria
IC 1 : Publications released on and after the year 2016.
IC 2 : Publications that have been published in peer-reviewed journals, conferences, workshops, etc.
IC 3 : English-language articles published.
IC 4 : Articles that are required to contain an abstract and title.
IC 5 : Publication that specifically addresses the subject topic such as data security, privacies encryption decryption, machine learning, blockchain, or research problems.
IC 6 : Research with subject-specific keywords included.
IC 7 : Systematic reviews, theoretical analysis, and empirical study.
Exclusion Criteria
EX 1 : Articles that are loosely connected to the research question or do not answer it.
EX 2 : Articles whose complete text cannot be accessed.
EX 3 : Articles not available in English.
EX 4 : Articles that were released almost ten years ago.
EX 5 : Studies with poor ratings or serious methodological errors.
EX 6 : Articles that don’t explicitly address privacy and data security concerns is excluded.
EX 7 : To prevent prejudice from incorporating the same study more than once, remove duplicate publications.
2.2 Algorithms, tools, and techniques Implemented
Alogrithm 1 : RSA (Rivest-Shamir-Adleman), ECC (Elliptic Curve Cryptography), and AES (Advanced Encryption Standard) are a few examples of the particular encryption techniques used in the studies.
Alogrithm 2 : Determine which machine learning techniques—such as anomaly detection methods (e.g., k-means clustering, isolation forests)—are utilized to detect data breaches or to ensure data security.
Tool 1 : To manage and organize references, use programs like Scispace, Citation Gecko, and Open Knowledge Map.
Tool 2 : To create visual representations of the data in MS Excel (graph).
Tool 3 : To check Grammar and Spelling Grammarly software tools are used.
Tool 4 : To draw the picture tools such as Paint, Smart Draw, and Origin-Lab are used.
Tool 5 : iThenticate is used for Plagiarism detection.
Techniques for Search
Technique 1 : Use Boolean operators and specified keywords to search IEEE Xplore, Scopus, and Google Scholar. The following query is an example: “data security” AND “privacies” AND (encryption OR data protection) AND “2016–2024”.
3 Advancing IoT, Big Data, and cloud integration: novelty in current research
In the rapidly evolving landscape of technology, the convergence of the IoT, Big Data, and Cloud computing stands at the forefront of innovation. Each domain, when studied individually, offers significant advancements and benefits. However, the integration of these technologies opens up unprecedented possibilities, presenting both opportunities and challenges. This research work provides the novel aspects of combining IoT , Big Data , and Cloud computing . Further, the paper highlights the transformative impact on various industries and emerging security concerns. This study aims to uncover new insights and propose solutions to ensure the safe and efficient deployment of integrated systems by exploring how these technologies interact. The major contributions of the current research paper are as follows:
Integration of IoT, Big Data, and Cloud Computing : The paper examines the combined effects and security threats of integrating IoT, Big Data, and Cloud computing.
Role Analysis : It offers an in-depth analysis of how IoT, Big Data, and Cloud storage work together.
Data Flow : The paper explores the process where data generated from IoT devices becomes Big Data and is subsequently stored in the Cloud.
Security Threats : It highlights the potential security threats during the transmission and storage of data.
Proposed Protections : The authors propose standard approaches to protect against potential attacks that could compromise the data.
Digital Forensics : The paper discusses digital forensics as a method to preserve and analyze digital data post-attack, aiding in tracing the attacker’s footprint and identifying patterns and trends.
Recent Data Security Technologies : In this research work, the authors addressed new technologies that have the potential to significantly reduce threats in cloud-IoT environments.
Research Focus : Authors determine the researcher’s field of expertise methodically.
4 Security goals in Cloud-IoT environments: a comprehensive overview
Security in Cloud-IoT environments is paramount due to the interconnected nature of devices and the vast amount of sensitive data they generate and process. Ensuring the confidentiality, integrity, and availability of data and services has become a major challenge as cloud computing and IoT devices become more integrated into everyday life and vital infrastructure. In an ever-changing digital ecosystem, this comprehensive overview seeks to explore the major security objectives, difficulties, and tactics that are crucial for protecting Cloud-IoT environments.
Figure 2 shows security objectives in a cloud environment. To guarantee the confidentiality, integrity, availability, and general security of data, applications, and resources hosted in the cloud, security objectives for a cloud environment are essential. These goals assist businesses in defining their security objectives and directing the application of suitable security solutions. For the confidentiality, integrity, and availability of data and services hosted in the cloud, security objectives for the environment are crucial. These goals aid organizations in developing a framework for putting security measures in place and in defining their security objectives. To respond to changing threats and keep a solid security posture in the cloud, it is essential to regularly assess and update security goals and procedures.
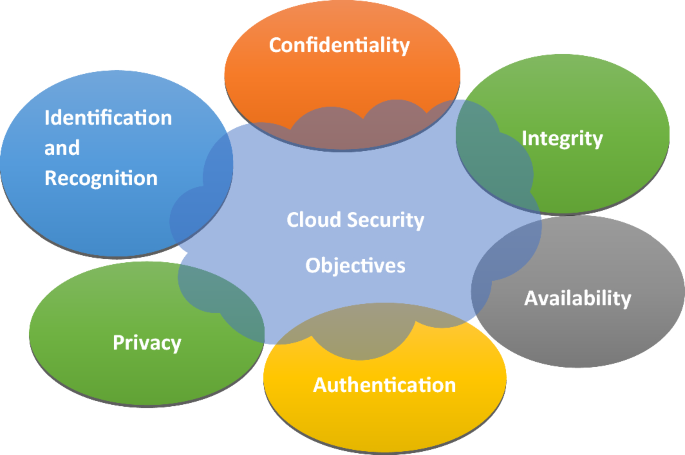
Security objective in cloud environment
Confidentiality Confidentiality refers to safeguarding or protecting critical data from unauthorized access. The information will only be revealed or accessible to those persons who are authorized (Schiller et al. 2022a ).
Identification and Recognition Identification is a unique way to provide attributes to users or devices to differentiate from other users. Recognition is related to the validation of the claimed identity. When a user gives a password, it matches with the saved password and identifies an individual (Schiller et al. 2022a ).
Privac: To safeguard the privacy of individual data, security measures are implemented. It also ensures that data must be responsibly handled. It involves protecting personnel information (Schiller et al. 2022a ).
Authentication: The authentication measures procedure involves confirming the identities of individuals and protecting against unauthorized access. It involves the user providing a username and password (Schiller et al. 2022a ).
Availability Availability refers to the accessibility and usage of data when required by an authenticated person. It involves maintaining availability includes protecting against denial of service, downtime, and disruptions that can hamper the availability of data (Schiller et al. 2022a ).
Integrity Integrity ensures that data should be consistent, accurate, and unchangeable throughout its lifecycle. It also ensures the trustworthiness of the data (Schiller et al. 2022a ).
Case studies that demonstrate how these security goals are implemented in practice are described below:
Estonia’s e-Residency Program: e-Residents receive a government-issued digital ID that is stored on a blockchain. This ID allows them to securely sign documents, access Estonian e-services, and run a business remotely.
MediLedger in Pharmaceutical Supply Chain: MediLedger uses blockchain, a decentralized ledger, to ensure data integrity and transparency.
Civic’s blockchain-based identity verification: It allows users to create and verify digital identities. Further, Enigma uses secure multi-party computation ( sMPC ) on the blockchain to ensure that data can be shared and analyzed without being exposed.
5 Taxonomy of Cloud-IoT environment
In the rapidly growing landscape of the Cloud-IoT environment, understanding the taxonomy is significant for navigating the complexities of connected devices and realizing their full potential in the swift diversification of the Cloud-IoT ecosystem.
5.1 The relationship between IoT, Big Data, and cloud computing
There is a strong synergistic relationship between Cloud Computing, Big Data, and the IoT, with each technology augmenting the other’s capabilities. IoT enables data collection which is uploaded to the cloud for storage and processing. These bulk data are accumulated in the cloud and form a large volume of data known as Big Data. Big Data tools and techniques are applied to these bulk data for processing and scrutiny of data on the cloud. Real-time monitoring and analysis are made possible by the convergence of cloud computing, Big Data, and IoT. This makes it possible to respond and act quickly, which optimizes processes, boosts productivity, and enhances user experiences.
Figure 3 illustrates the relationship between the IoT devices that are placed at remote locations. Data is generated from IoT devices which are stored and analysed on the cloud using Big Data tools. Finally, after processing data on the cloud decision is made. IoT, Big Data, and cloud computing work together to create a potent trio that propels efficiency and innovation in a wide range of sectors, including manufacturing, agriculture, smart cities, and healthcare.
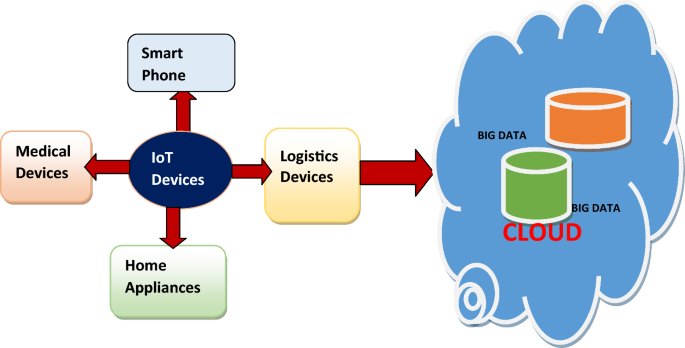
Relationship between IoT, Big Data, and cloud computing
5.1.1 Understanding the dynamics of Big Data
Big Data in a few years come out as an ideal that has provided an enormous amount of data and provided a chance to enhance and refine decision-making applications. Big Data offers great value and has been considered as being a driving force behind economic growth and technological innovation (Dutkiewicz et al. 2022 ). Machines and humans both contribute to data through online records, closed-circuit television streaming, and other means. Social media and smartphones create enormous amounts of data every minute (Ram Mohan et al. 2018 ). Big Data is a large amount of data that is fast and complex. These data are not easy to process using conventional methods. Today Giant Companies substantial portion of the value advanced from data generated by the company which is continually examined to produce better and advanced products. A prime example of Big Data is the New York Stock Exchange, which creates one terabyte of fresh trade data daily. Big Data characteristics are defined by the 4 V’s i.e. Volume, Variety, Velocity, and Veracity which is shown in the figure below. Big Data involves three main actions integration, managing, and analysis.
Figure 4 A and B illustrate the essential 4 V’s i.e. Variety, Volume Velocity, and Veracity of Big Data through 4 blocks. Volume block represents the size of data that grows exponentially such as Peta byte, Exa byte, etc. It represents how much information is present. The volume of data is increasing exponentially. Velocity block shows that data is streaming into the server for analysis and the outcome is only useful if the delay is short. It is used to portray how fast information can be available. Data must be generated quickly and should also be processed rapidly. For example, a healthcare monitoring system in which sensors record the activities that occur in our body and if an abnormal situation occurs needs a quick reaction. Variety blocks represent, a variety of data and various formats, types, and structures of data that exist such as sensor data, PDF, photo, video, social media data, time series, etc. The veracity block ensures that data should be consistent, relevant, and complete in itself. Hence, the error can be minimized accurate results can be produced and decisions can be taken through analysis of the result.
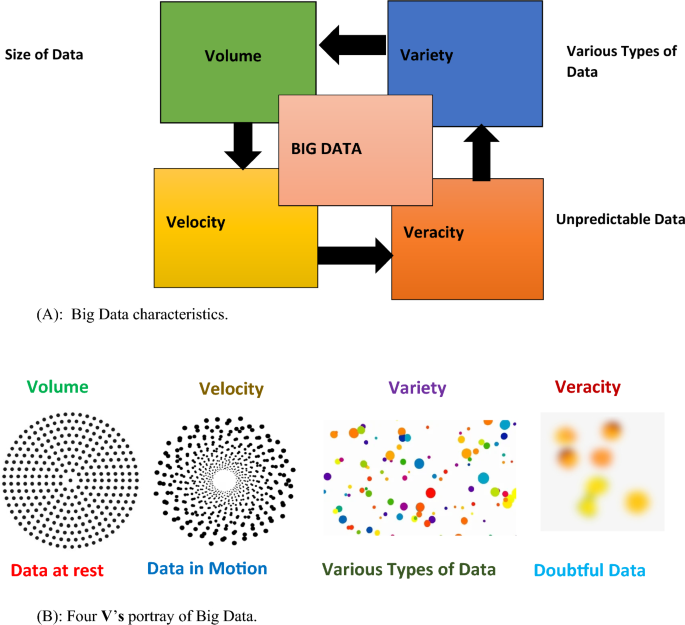
A Big Data characteristics. B Four V’s portray of Big Data
Apart from its several advantages Big Data faces security challenges as well such as attackers can damage or steal information where a large volume of data is stored such as cloud and fog. An attacker can steal data and he/she can attempt to study and analyze data and thereafter can change the outcome of the result accordingly. Therefore special protection and privacy of data such as cryptographic defense mechanisms should be provided so that data can be kept safe and secure (Kaaniche and Laurent 2017 ). The healthcare industry is one of the most promising areas where Big Data may be used to effect change. Large-scale medical data holds great promise for bettering patient outcomes, anticipating epidemics, gaining insightful knowledge, preventing avoidable diseases, lowering healthcare costs, and enhancing overall quality of life. To address security and privacy threats in healthcare, the author has provided some suggested strategies and approaches that have been documented in the literature, while also outlining their drawbacks (Abouelmehdi et al. 2018 ).
5.1.2 Connecting the world: the evolution and impact of the Internet of Things
The development of the Internet of Things has revolutionized the Internet market around the world. The Internet of Things is a device that when connected to the Internet transmits, receives, and stores data over the cloud. The Internet of Things is embedded with several devices such as sensors, physical devices, and software to control the devices. IoT can be device can include anything that contains a UID (Unique Identification Number) that can be used to in identify uniquely over the internet. IoT devices have several benefits such as high efficiency, providing more business opportunities, high productivity, increased mobility, and many more. Apart from the above-mentioned benefits, IoT devices can also be deployed to monitor tool execution and find and diagnose the issues before any major break happens in the functioning of the device, also in addition it reduces maintenance costs and thereby increases the throughput. IoT devices can able to gather large volumes of data beyond any human can think of it. As the world is developing data is considered to be an oil for the development of any country, so to cope with new challenges IoT devices should also be made smarter than traditional devices which can able to guide and make decisions. To achieve such objectives IoT devices should be accompanied by machine learning and artificial intelligence technology to enhance the performance of the device and to make sense of collected data.
Figure 5 illustrates the key components of IoT devices. The components are the building blocks of IoT which is shown in the diagram. These “DGCAU” components collectively facilitate the working of the IoT devices. Each component is significant in terms of productivity, data collection, monitoring, and connectivity. In Fig. 5 ‘D’ stands for IoT Device. IoT devices are those which are such as medical equipment, smart meters, home security systems, smart lights, etc. which are used to collect data. The second ‘G’ stands for Gateway which is similar to a centralized hub that is used to interconnect IoT devices and sensors to the cloud. Advanced gateway facilitates data flow in both directions between IoT devices and the cloud. ‘C’ indicates the cloud aids in the storage of data and simultaneously analyzing data. Rapid processing and strong control mechanisms enable cloud-enabled IoT devices to minimize the risk of attack. User identities and data are protected by strict authentication methods, encryption tools, and biometric authentication in Internet of Things devices. ‘A’ signifies the Analysis of data that was stored in the cloud to determine the outcome. Analysis tool studies large amounts of data and produces useful information, which is helpful in decision-making. The last component ‘U’ represents the user interface or UI module that facilitates the user to administer the IoT device with which they are interacting. it is generally a graphical user interface that includes a display screen, mouse, keyboard, etc.
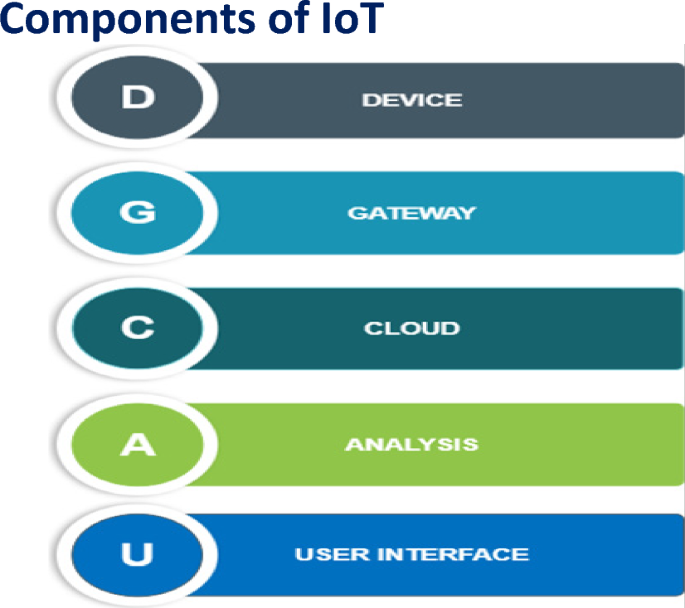
Key components of the Internet of Things
Figure 6 shows the various applications of the IoT which are technology paradigms used to interconnect the devices with the Internet, collect data, share data, transmit data, and act upon data. IoT has enormous application in day-to-day life therefore enabling us to perform our work widely and conveniently . Smart Lighting IoT can be used to operate the light remotely through a smartphone. Transportation IoT is used to track vehicles and goods in real-time. IoT finds application in health which enables doctors to monitor the patients remotely. In Logistics IoT helps to keep track of goods and vehicle devices. IoT is useful for smart framing because IoT sensors can monitor, measure, and track soil moisture, nutrients needed for crop fertilization, and irrigation needs. IoT devices used in retail monitor the department’s real-time inventory level and stock and forward orders when a product is discovered to be out of stock. With features like motion sensors, doorbell cameras, and video surveillance , smart home security systems employ the Internet of Things to monitor and secure houses. IoT is used by smart grids to increase the effectiveness and dependability of electricity delivery. Water quality indicators like pH, turbidity, chlorine levels, and pollutants are continuously monitored by IoT sensors. Smart meters with IoT capabilities allow for real-time monitoring of utility consumption. IoT equipment on autonomous vehicles processes sensor data in real time. This entails reading and assessing the environment to make deft choices regarding safety, navigation, and vehicle control. Wearable gadgets gather information on activities, health, and other topics before sending it for analysis to smartphones or the cloud for processing.
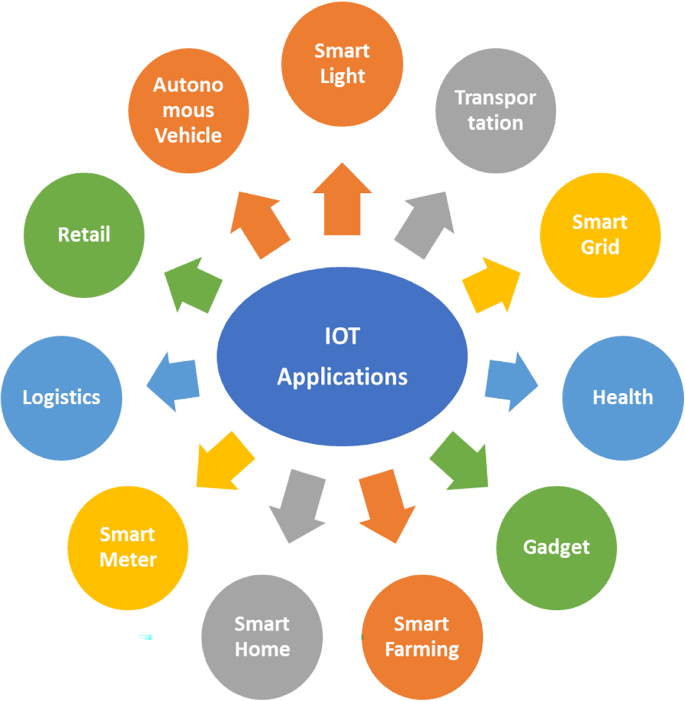
Internet of Things applications
Apart from the benefits of IoT devices in day-to-day life, IoT devices suffer security threats as well. The rapid growth of IoT devices has revolutionized how we interact with technology. As the number of IoT devices increases the security concern also increases simultaneously. The author addresses the issue of sharing sensitive data securely for designated recipients in the context of the Blockchain Internet of Things (B-IoT) (Yin et al. 2022 ). The author has scrutinized the security flaws in computer systems based on cloud, blockchain, IoT, and fog computing (Mishra et al. 2022 ; Yao 2022 ; Abdulkader 2022 ). Security challenges and threats in IoT and cloud environments addressed by various authors are presented in the papers (Pandey et al. 2023 ; Ray and Dutta 2020 ; Bedi et al. 2021 ). Cloud Computing and IoT Using Attribute-Based Encryption approaches are developed by authors found to be very effective in the security domain (Mihailescu et al. 2022 ; Henze et al. 2017 ). The author presents D-CAM, a solution for achieving distributed configuration, authorization, and management across borders between IoT networks (Simsek 2023 ). The study presented by the author is a novel handshake protocol for the broker-based publish/subscribe paradigm in the Internet of Things that offers key exchange-based authentication, authorization, and access control (Shin and Kwon 2020 ; Stergiou et al. 2018 ).The goal of a systematic literature review (SLR) paper is to examine the body of research on cloud computing security, risks, and difficulties that are presented by authors (Wang 2021 ). The primary issue in the cloud environment has been confirmed to be data access, despite the security measures being deemed dependable (Javid et al. 2020 ; Gai et al. 2021 ; Shukla 2022 ). We suggested an effective data access control method that uses optimal homomorphic encryption (HE) to get around this issue (Gnana Sophia et al. 2023 ). The paper highlights the edge computing security and privacy requirements (Yahuza et al. 2020 ). Multiple encryption techniques are presented by the authors which are significant in protecting privacy and data security (Sharma et al. 2019 ; Silva et al. 2018 ; Bertino 2016 ). The author proposes a distributed machine learning-oriented data integrity verification scheme (DML-DIV) to ensure the integrity of training data (Zhao and Jiang 2020 ). The researcher introduced an identity-based (ID-based) RDIC protocol including security against a malicious cloud server which is presented in the paper (Yu et al. 2017 ; Sookhak et al. 2018 ). The authors studied various security challenges concerning IoT devices, Big Data generated by IoT devices, and cloud and presented them in the paper (Akmal et al. 2021 ; Awaysheh et al. 2022 ; Tang 2020 ; Shi 2018 ).
5.2 Navigating the cloud: exploring the world of cloud computing
Cloud Computing refers to Internet-based computing, where shared resources data, software, and information are to the customer and devices on demand. The term “cloud” used to appear on the Internet. Huge memory space and inexpensive, high-performance computing are made possible by the cloud computing paradigm. Users can get cost savings and productivity benefits to manage projects and develop collaborations by moving their local data management system to cloud storage and utilizing cloud-based services. Information and knowledge extraction is greatly aided by computing infrastructure, particularly cloud computing. The services for cloud computing are provided using the network, generally the Internet. The characteristics of cloud computing include broad network access, on-demand service, rapid elasticity, and many more. With the help of the cloud, numerous services are accessible to clients. Broadly there are three types of services offered that enable the client to use software, platform, and infrastructure. Several types of cloud can be subscribed to by anyone as per the requirement of an individual or any organization. These include private cloud, public cloud, and hybrid cloud. Private cloud solely owned by any business houses. In this type of cloud infrastructure software is preserved on a private network and hardware and software entirely belong to the organization. Public clouds are commonly cloud services that are allotted to various subscribers. Third-party owned and operated the cloud resource.
The public cloud is mostly used for online office applications, testing, development, etc. A hybrid cloud is a combination of public and private clouds, which is implemented by a couple of interrelated organizations. Common types of cloud services are presented through the 3-layer architecture of Cloud Services in Fig. 7 and each one is discussed.
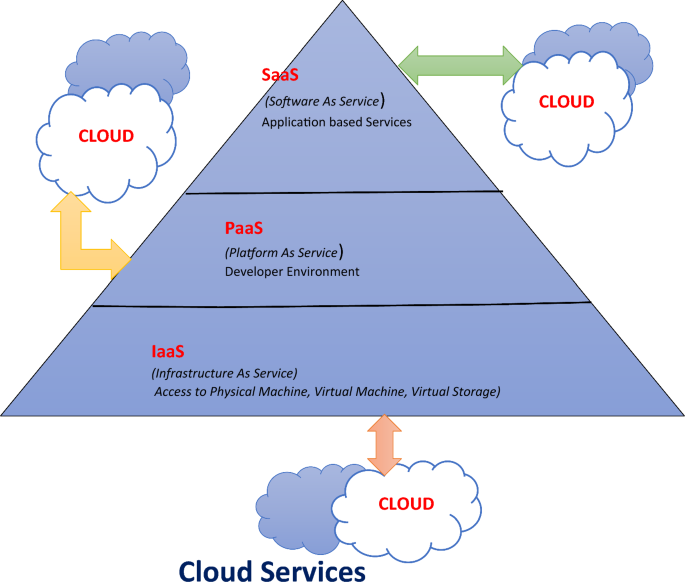
3-Layer architecture of cloud services
Figure 7 exhibits the different types of cloud and services provided by the cloud. The figure conveys the three-layer architecture of the cloud. IaaS makes virtualized computing resources available via the internet, enabling customers to pay-as-you-go access and manage the essential parts of the infrastructure. These resources often include storage, networking, virtual machines, and other things. Platform as a Service (PaaS) is a cloud computing architecture that offers developers a platform and environment to create, deploy, and manage applications. PaaS provides a variety of tools and services that speed up and improve the efficiency of the application development process. A cloud computing approach called Software as a Service (SaaS) allows users to access software programs online. SaaS has many benefits, including affordability, scalability, and accessibility.
Because crucial data is processed and stored on the cloud, for instance in Internet of Things applications, it also poses security and privacy issues (Alouffi et al. 2021 ; Hamzah Amlak and Kraidi Al-Saedi 2023 ; Yu et al. 2022 ). Cloud security is an important area where authors have tried to find the best possible solution through their research they have highlighted the challenges of possible solutions to the problem through finding and investigation in the paper (Gupta et al. 2022 ; Chaowei et al. 2017 ; Wang et al. 2021 ).
To ensure the integrity of data kept in the cloud, the author’s study proposes an effective public auditing technique that makes use of Third third-party auditor (TPA) (Reddy 2018 ; Hiremath and Kunte 2017 ; Yan and Gui 2021 ). The author proposes an efficient certificate-based data integrity auditing protocol for cloud-assisted WBANs (wireless body area networks (Li and Zhang 2022 ). The author proposed a secure architecture by associating DNA cryptography, HMAC, and a third-party auditor to provide security and privacy (Kumar 2021 ; Duan et al. 2019 ). Adversaries are always coming up with new ways to get access to users’ devices and data through developing technologies like the cloud, edge, and IoT. The author discussed various attacks along with security solutions (Pawlicki et al. 2023 ). The paper highlights the research challenges and directions concerning cyber security to build a comprehensive security model for Electronic health records (Chenthara et al. 2019 ; Hou et al. 2020 ; Ishaq et al. 2021 ; Jusak et al. 2022 ). The author mentioned the research and analysis of privacy-preserving data mining (PPDM) and classified using various approaches for data modification in the research paper (Binjubeir et al. 2020 ).
Even with all the benefits mentioned, there are security and privacy issues while using cloud computing (Nanda et al. 2020 ; Himeur et al. 2022 ). The issue of data security and privacy for Big Data is complicated by the use of cloud computing for Big Data management, storage, and applications. Since cloud services are typically offered on a common infrastructure, there is always potential for new attacks, both internal and external, such as password theft or application programming interface (API) flaws. The author has proposed a software architecture model by using approaches like hardware security extensions (Intel SGX) and homomorphic encryption. To improve data security in large data cloud environments and defend against threats, a virtualization design and related tactics are suggested by the author. The TID (Token Identification) model developed by the author provides security to the data. The user has various access rights as a client. The authentication access token establishes a connection with the user account after the user logs into the cloud network. The researchers have developed the Remote Data Checking (RDC) technique, which uses the sampling technique to evaluate the integrity of data that is outsourced across remote servers. Authors developed the techniques for remote data auditing that are very beneficial in ensuring the integrity and dependability of the data that is outsourced. Data, auditing, monitoring, and output these elements are all included in the DAMO taxonomy. The author in his paper offers a unique security-by-design framework for the implementation of BD (Big Data) frameworks via cloud computing (Big Cloud) (Ye et al. 2021 ). Various data security issues in the Big Data cloud computing environment are addressed by the authors in his paper. Various methods for safeguarding privacy and data security in public clouds are covered in the article (Jain et al. 2016 ). A multi-cloud architecture with privacy and data security enabled is suggested by the author. To increase user security on SNg (Social Networking) by utilizing techniques that can give data about BD technology (Big Data) greater privacy. This approach is described by the author in the paper along with various metrics and usage-related outcomes. The author examines financial risk analysis and related regulatory studies using blockchain and Big Data technologies. A secure cloud environment can be achieved by using a hybrid cryptographic system (HCS), which combines the advantages of symmetric and asymmetric encryption.
Figure 8 shows a hierarchical structure created to handle and process data and applications efficiently depending on how close they are to the user or the source of the data. “Hierarchical edge computing” refers to the interplay between these three layers, cloud, fog, and edge. The Cloud Layer is a centralized data processing center that provides abundant computing and storage capacity for handling and storing enormous volumes of data as well as running sophisticated applications. The growths of the Internet and its associated ideas, such as edge computing, cloud computing, and the Internet of Things, have had a permanent impact. The cloud layer is a highly scalable data center that is perfect for managing large-scale applications and services because they can extend horizontally to manage increased workloads.
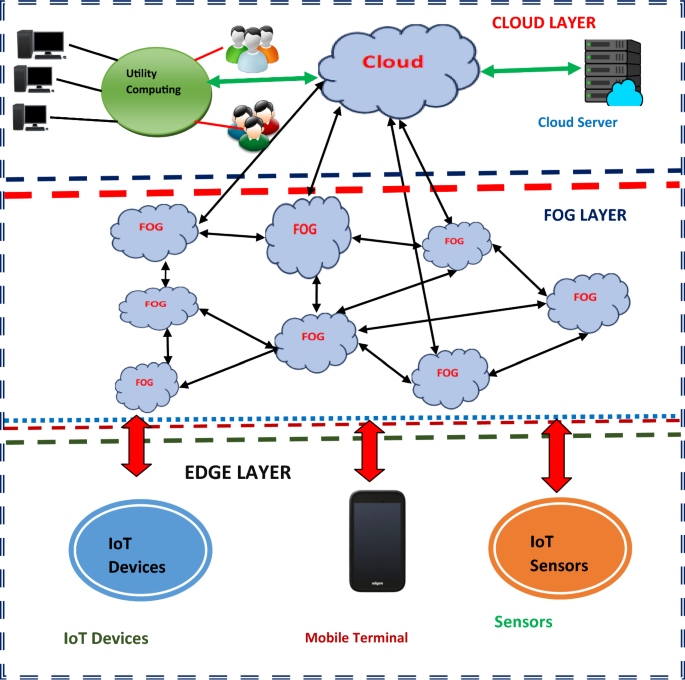
Hierarchical edge computing
The fog Layer is an intermediate layer after the cloud layer which spreads and distributes processing responsibilities among several local servers or devices, which can be very useful for IoT applications with many data sources. Fog computing is ideal for latency-sensitive applications that demand quick responses. Virtual components called cloudlets are employed in fog computing. Fog computing has emerged as a promising paradigm in overcoming the growing challenges (e.g., low latency, location awareness, and geographic distribution) arising from many real-world IoT applications, by extending the cloud to the network edge. To facilitate data offloading and computation, these virtual computers offer a micro data centre close to mobile devices (Lu et al. 2020 ). Fog computing offers new insights into the extension of cloud computing systems by procuring services to the edges of the network. It shortens the time it takes for data to go to the cloud and back by processing it closer to the source. The edge layer, which is frequently located adjacent to IoT medical devices themselves (Muzammal et al. 2018 ), is the one that is nearest to the data source or end users. A promising paradigm that expands on cloud computing capabilities is edge computing. It processes data instantly, allowing for extremely quick replies devices, sensor devices, and industrial machinery, mobile terminals are examples of edge devices that can function autonomously and make decisions in the present without relying on a central cloud infrastructure (Ghaffar et al. 2020 ; Jiang et al. 2016 ). Big Data applications are a risk for cyber security assaults, as these attacks directly affect applications utilized across several sectors, such as Big Data analytics. The authors presented a novel data encryption approach, which is known as Dynamic Data Encryption Strategy (D2ES) to protect and safeguard the data which proves promising in cloud computing. Encrypted data can be obtained by cryptography methods, enabling secure communication links within the networking system. Researchers suggested the blockchain-based Shamir threshold cryptography solution for IIoT (Industrial Internet of Things) data protection. An improved data security in mobile edge computing, the Fine-Grained Access Control mechanism (FGAC) is suggested to guarantee data security during data access (Ahmed et al. 2021 ).To analyze and investigate the data reduction at the fog level, researchers attempted to create a model. This researcher has successfully applied methods including artificial intelligence, principal component analysis (PCA), and the Naïve Bayesian classifier for data reduction.
6 Exploring the complex landscape of Cloud-IoT threats: an in-depth analysis
Security concerns are growing along with the integration of Cloud Computing and the IoT. Numerous dangers and vulnerabilities that might compromise the availability, confidentiality, and integrity of data and services are brought about by the junction of these two technologies. We examine the subtleties, possible effects, and vital necessity of strong security measures to protect against changing hazards in interconnected environments as we delve into the complex nature of Cloud-IoT security concerns in this analysis.
Figure 9 illustrates the numerous types of attacks that can take place in the cloud. These Attacks can harm the cloud service provider as well as cloud customers. The attacker is an individual who attempts to use a cloud infrastructure, platform, or service’s vulnerabilities or flaws for nefarious reasons in the world of cloud computing. Because they frequently house significant data and offer computational resources that may be used for a variety of purposes, such as launching cyber-attacks, stealing confidential information, or causing disruption, cloud systems are very alluring targets for attackers. For different purposes, including data theft, service interruption, or resource exploitation, attackers target cloud environments. To breach cloud systems, attackers use a range of methods and tactics. These attack methods can include insider threats, sniffer attacks password change SQL-Ingestion, Eavesdropping, malware, distributed denial-of-service (DDoS) attacks, phishing, and more (Basit et al. 2021 ; Ullah et al. 2019 ; Jahromi et al. 2021 ).
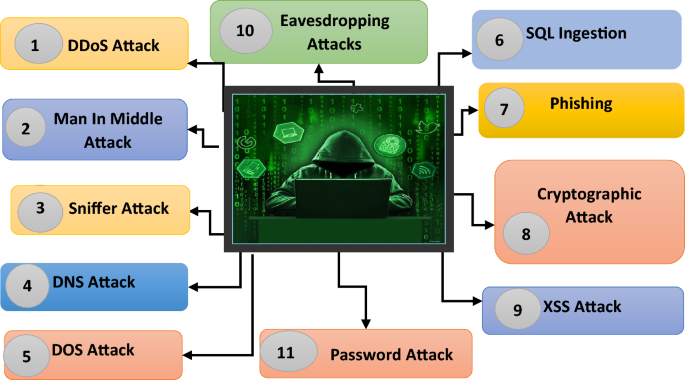
Threats in cloud computing environment
DDOS Attack A distributed denial-of-service attack aims to disrupt regular network operations by flooding the network with traffic. Denial-of-service attacks aim to prevent end users from accessing the network.
Man-in-Middle Attack In a man-in-middle attack, the attacker generally modifies the conversation between the two parties. In a man-in-the-middle attack, attackers generally eavesdrop on sensitive information and alter the conversation. The integrity and security of sensitive data are seriously threatened by MitM attacks.
Sniffer Attack It is an attack in which an unauthorized person intercepts and gains control over network traffic. The goal is to capture and examine the data when it passes over the network.
DNS Attack The domain name system attacks the domain name system, which is responsible for converting human name readable to IP address. DNS attacks have the potential to affect the DNS infrastructure’s availability, integrity, and confidentiality, which could cause interruptions to internet services.
DOS Attack A Denial of Service (DoS) assault involves the exploitation of a single source, typically a compromised device or computer, to overwhelm a target’s resources and cause a loss of service.
SQL Ingestion In SQL (Structure Query Language Ingestion), attackers ingest harmful code inside the parameters of a web application. The main goal of attackers is to manipulate SQL databases. In this type of attack, the attacker gains the advantage of bad input, which enables the attacker to execute the SQL command.
Phishing Attack In Phishing attackers use some trick to expose delicate information, for example, username, personal information, password, and credit card details. Phishing attacks sometimes use the personas of reliable companies, banks, or websites to trick people into doing things that could jeopardize their security.
Cryptographic Attacks Cryptography is important to ensure confidentiality and integrity and authenticate the user. The attacker exploits vulnerability or weakness in the existing system. Attackers compromise the security of cryptographic systems.
XSS Attacks Cross-site scripting (XSS) is one of the serious attacks that occur when vulnerable code which is in the form of a script is injected into the web page of the user. The objective of the attacker is to steal sensitive information about the user by running the scripting code in the user’s browse.
Eavesdropping Attacks Eavesdropping is a kind of attack in which attacker unauthorized person tries to listen to or sniff the conversation between two people and steal information. In this type of attack, the attacker even manipulates the information.
Password Change Request Interception Attack The assailant attempts to intercept legitimate users’ password changes. Interception of this kind could happen during a browser-server conversation.
7 Exploring research trends and areas of focus
As technology continues to evolve at a rapid pace, researchers and academics are continually exploring new trends and areas of focus within their respective fields. To keep ahead of new difficulties, seize opportunities, and encourage innovation, this investigation is essential. We explore the current research trends and areas of attention in a variety of disciplines in this overview, offering insight into the cutting-edge subjects that are influencing the direction of technological and scientific advancement. After scrutinizing the number of published research papers we came across various domains in which researchers have worked and proposed various security frameworks.
Table 1 represents the research work and focus of various researchers in field security. From the table above it can be concluded that researcher have focused on Cloud Computing and their finding are more concentrated on Cloud security and the Internet of Things. The researcher primarily focused on the development of security algorithms to protect the data from being damaged or corrupted by cyber attackers. Through study, it was found that researchers have developed innovative techniques by making use of machine learning techniques, and blockchain technology to safeguard data developed for the Internet of Things.
Cryptography is another eminent way to protect our data. Researchers have created algorithms to encrypt and decrypt data prominently so that data can be safely transmitted over the network. A method like PSEBVC: Provably Secure ECC and Biometric Based Authentication Framework is developed by the author as a countermeasure for attacks.
In the digital landscape, the risks of cyber-attacks are growing enormously which is becoming a challenge for both organizations and individuals. A comprehensive examination of attack vectors and mitigation strategies is essential for understanding and effectively countering these attacks (Wylde et al. 2022a , b ). Through an analysis of numerous attack pathways and related mitigation techniques including artificial intelligence-based solutions discussed in paper (Al Hamid et al. 2017 ; Abed and Anupam 2022 ). This research paper aims to offer important insights on how to enhance security and defend against cyber threats in a constantly changing security environment. The objective of this analysis is to provide individuals and organizations with the necessary knowledge and tools to improve their digital security and minimize risks in the constantly changing threat landscape. To do this, each attack mechanism is thoroughly examined, and appropriate remedies are explored through Table 2 .
Table 2 is a complete description of the investigation of the several research papers related to security threats that exist, various categories of attackers that occur on the cloud, and countermeasures that can be taken to prevent attacks summarized in the Table by the author. The table shows how attacks affect the data and what standard approaches were developed by researchers to protect data.
8 Unveiling the intricacies of digital forensics in Cloud-IoT environments
Digital Forensics is a branch of forensic science that concentrates on recovery of data, analysis of data and exhibit the digital evidence that is found on electronic devices. The IoT Forensics can be identified as part of Digital Forensics. The objective of IoT Forensics is to explore digital information in an authorized manner. IoT forensics data can be accumulated through IoT devices, sensors, networks, and cloud. There are some differences between security, IoT, and forensics. The protection against physical and logical security threats is provided by IoT security adopts multiple methods to protect from threats and minimize attacks (Unal et al. 2018 ). Forensics examines the data present in the devices and recreates the happenings by utilizing investigative methods to preserve and analyze digital data. Post-mortem examinations are the main focus of forensics i.e. discovering shortcomings that emerged from the event. Forensic experts obtain digital proof throughout the actual event with the help of standard approaches used in forensic analyses of physical proofs of electronic data to determine and reframe the events by storing and analysis of digital information using different methods of investigation. Some authors have presented detailed studies to investigate the forensic issues in cloud computing and provide possible solutions, and guidelines, including existing case studies (Morioka and Sharbaf 2016 ; Al-Dhaqm et al. 2021 ). The paper offers an enhanced blockchain-based IoT digital forensics architecture that builds the Blockchain’s Merkle tree using the fuzzy hash in addition to the traditional hash for authentication (Mahrous et al. 2021 ). Authors Almutairi and Moulahi ( 2023 ) trained models locally using federated learning on data stored on the IoT devices using a dataset created to simulate attacks in the IoT environment. In order to make the blockchain lightweight, the authors next carried out aggregation via blockchain by gathering the parameters from the IoT gateway (Almutairi and Moulahi 2023 ).
The IoT has revolutionized various sectors through seamless device interactions, yet it has introduced significant security and privacy challenges. Traditional security measures often fall short due to IoT’s distinct characteristics like heterogeneity and resource limitations. Danish Javed et al. ( 2024a ) explored the synergy of quantum computing, federated learning, and 6G networks to bolster IoT security. Quantum computing enhanced encryption, while federated learning preserved data privacy by keeping training data on local devices. Leveraging 6G’s high-speed, low-latency capabilities allows for secure, real-time data processing among IoT devices. The study also reviewed recent advancements, proposed a framework for integrating these technologies, and discussed future directions for IoT security. Recent innovations in network communication have revolutionized the industrial sector with automatic communication through the Industrial Internet of Things (IIoT) . Despite its benefits, the increased connectivity and use of low-power devices in IIoT heighten vulnerability to attacks, and its diverse nature complicates centralized threat detection. To tackle this, authors Javed et al. ( 2023 ) proposed a fog-based Augmented Intelligence (IA) defense mechanism that uses GRU and BiLSTM deep learning classifiers for anomaly detection and secure communication. This framework (Cu-GRU-BiLSTM), which achieved up to 99.91% accuracy, surpassed existing threat detection methods, proving its effectiveness for securing IIoT environments (Javeed et al. 2023 ).
Further, the hybrid approach proposed by Danish Javed et al. ( 2024b ) enhances intrusion detection in federated learning (FL) for IoT by addressing existing limitations. Here, CNNs identify local intrusion patterns by extracting spatial features, while BiLSTM captures sequential patterns and temporal dependencies. Using a zero-trust model, data stays on local devices, and only the learned weights are shared with the centralized FL server. The server then combines updates to improve the global model’s accuracy. Tests on CICIDS2017 and Edge-IIoTset datasets show this method outperforms centralized and federated deep learning-based IDS.
9 Advancements in security threat detection and avoidance
With the constant advancement in sophistication of cyber attacks, enterprises, and individuals alike are obliged to use innovative methods and technologies to detect, prevent, and mitigate potential security breaches. Threat detection is seeing tremendous breakthroughs, enabling defenders to keep one step ahead of malicious actors. These advancements include machine learning algorithms and behavior analysis methodologies. This ongoing change emphasizes how crucial it is to take preventative action to protect sensitive data and maintain digital trust in an environment where dangers are becoming more complicated.
9.1 Harnessing the power of machine learning
Machine learning is a subset of artificial intelligence (AI) that focuses on developing models and algorithms that enable computers to learn from data and make decisions or predictions without having to be explicitly programmed to do so. As a result, machine learning algorithms are beneficial when dealing with vast amounts of data since, after being trained on the data (Ali et al. 2020 ), the trained model uses its learning experience to present precise outcomes on new data. Data generated by IoT devices may suffer from threats (Safaei Yaraziz et al. 2023 ). Today Machine Learning proves to be one of the strongest tools to identify threats and maintain the integrity of data in transmission. The foundation of machine learning is the algorithms that are used to train the models. The first step in using machine learning to address a problem is gathering data. Next come tasks like data preparation, data analysis, training, testing, and eventually deploying the model for real-world application. Two types of ML problems can be solved by supervised machine learning algorithms: regression and classification. Classification is used to solve problems with binary target variables ( yes / no ), while Regression ML algorithms are used to address problems of similar nature when the target variable is continuous. A phishing attack has become one of the most prominent attacks faced by internet users, and governments. The attacker(s) transmits URL(s) to the intended victims via text messaging, social networking, or spam messages. They do this by mimicking the behavior of authentic websites when creating website pages. Malware attack during data in transit is a common type of attacks that can manipulate the data and damage the data. To prevent such attacks ML model can be one of the tools to identify such attacks and prevent them to such extents. Machine Learning algorithms have been used to build several intrusion detection systems, improving the systems’ ability to identify threats and enabling uninterrupted business operations (Pathak et al. 2023 ). Despite many benefits that SDN(Software-Defined Networking) offers such as offer nimble and adaptable network growth, malicious attacks that can eventually prevent network services are unavoidable (Unal et al. 2018 ). Machine learning has been used in several studies to detect distributed denial of service (DDoS) threats in SDN (Software-Defined Networking) environments (Morioka and Sharbaf 2016 ). ML models are being trained on numerous datasets to build models that can detect cloud attacks with elevated accuracy. Various classifier is implemented in the ML model to identify attacks such as SVM, Decision tree, K-NN (K-Nearest Neighbour), Convolutional Neural Networks (CNNs), Recurrent Neural Networks (RNNs), random forests, and many more. The use of random forest and K-NN classification approaches enables malware detection method proofs to be 99.7% accuracy and 99.9% in several cases (Abed and Anupam 2022 ; Morioka and Sharbaf 2016 ). These classifiers can be used with different feature engineering and feature selection strategies to create machine learning models that effectively handle certain security issues and enhance overall cyber security posture.
Figure 10 represents security threat detection using machine learning algorithms and models. The automatic detection of potential security threats and abnormalities within a file system using machine learning techniques uses a predictive model to identify the threat and classifies it as a malware file or harmless file over the system. Data breaches and other security problems can be prevented because of their ability to assist enterprises in detecting and responding to threats more quickly and effectively. In this process, it involves two important stages. The first stage is the Training stage where the model is being trained using different files. Files are sent as input to train the model. Numerous machine learning algorithms, such as decision trees, random forests, support vector machines (SVM), neural networks, and others, can be used for training the model. After the model is trained, then comes to the security stage where an unknown file is given to the model for analysis the file. For the detection of security threats, supervised learning techniques like classification and regression are frequently used. The machine learning model generates notifications for security professionals to investigate when it spots a potential security danger or abnormality. Automated responses to lessen or control the crisis may also be triggered based on how serious the threat is. Deep learning approach is used to detect pirated software and malware-infected files across the IoT network. Using color picture visualization, the deep CNN is utilized to identify harmful infections in Internet of Things networks. Secure video transmission over the cloud is discussed in the paper (Hossain et al. 2018 ). Researchers have developed Holistic Big Data Integrated Artificial Intelligent Modelling (HBDIAIM) to provide and improve privacy and security in data management (Chen et al. 2021 ). The previously developed model falls short in providing adequate data privacy and security, keeping this shortcoming in mind author (Yazdinejad et al. 2024a ) developed an Auditable Privacy-Preserving Federated Learning (AP2FL) model tailored for electronics in healthcare. AP2FL model provides secure training and aggregation processes on the server side as well as the client side. Thereby protecting and minimizing the risk of data leakage. Researchers primarily focus on Machine learning-based threat detection models to address the challenges within Consumer IoT. Using Federation Learning (FL) techniques data privacy in Consumer IoT is maintained (Namakshenas et al. 2024 ). The author suggests an approach to attack detection that makes use of deep learning (DL) algorithms to identify false data injection (FDI) assaults (Sakhnini et al. 2023 ). In the research paper, the author utilizes federated learning to automatically search for threats in blockchain-based IIoT (Industrial Internet of Things) networks using a threat-hunting framework we call block hunter (Yazdinejad et al. 2022 ).
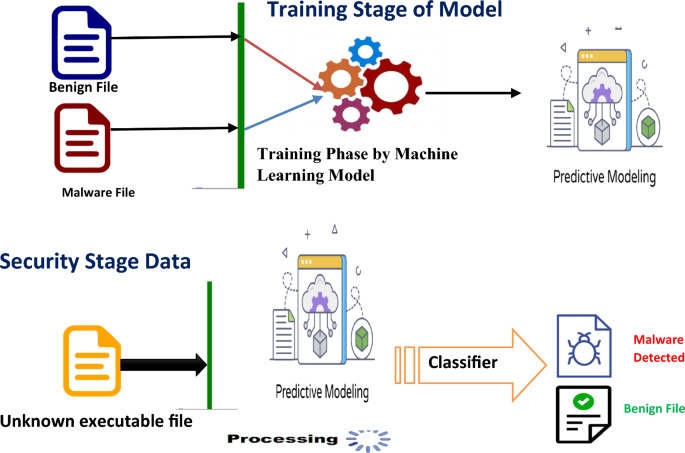
Security threat detection using machine learning technique
Real-life applications of machine learning in malware detection
AT&T Uses machine learning to protect networks and find malware that targets telecom infrastructure.
Mayo Clinic A healthcare organization that implements machine learning techniques to safeguard patient data from malware attacks and unauthorized access.
Bank of America Employs AI and machine learning to improve cyber security safeguards, identifying malware and averting breaches in data.
Cylance A cyber security firm that heavily relies on machine learning to identify and eradicate malware. To identify threats instantly, its algorithm is trained on an extensive dataset of both malicious and benign files.
Amazon Web Services (AWS) AWS uses machine learning techniques to identify threats, examining the logs and network traffic.
Symantec An American consumer-based software company that employs machine learning techniques to identify and categorize malware.
National Security Agency (NSA) To improve national cyber security, the National Security Agency (NSA) uses cutting-edge machine learning algorithms to identify and analyze malware.
9.2 Unlocking the power of blockchain: a cutting-edge safeguard technique for enhanced security in the digital landscape
Blockchain is an emerging decentralized technology that securely stores and authenticates transactions across a network of computers. Its decentralized and open structure makes it a viable option for many companies looking to improve digital security, efficiency, and trust. Although cloud computing is becoming more and more popular for processing and storing data, security, and privacy are still big issues because of the possibility of hostile assaults on wireless and mobile communication networks. Data transfer privacy and system security are improved by using blockchain technology. To put it briefly, a blockchain is auditable, can function as a distributed ledger with digitally signed data, and allows changes to be tracked back to the original data to ensure security. This demonstrates that the security of data may be guaranteed by blockchain technology (Safaei Yaraziz et al. 2023 ). The suggested IAS protocol is developed on top of blockchain technology to guarantee the security and authenticity of data transmission in cloud computing. A potential solution to the security and privacy problems in the Internet of Things is blockchain technology (Williams et al. 2022 ; Waheed et al. 2020 ). For every transaction including proper authentication, data can pass through the blockchain distributed ledger thanks to blockchain technology, which does away with the idea of an IoT central server. Blockchain technology could provide a more effective answer to the issues that IoT systems confront. Transactional privacy, decentralization, the immutability of data, non-repudiation, transparency, pseudonymity, and traceability, as well as integrity, authorization, system transparency, and fault tolerance, are the primary security features of blockchain technology. The Smart contact is verified, put into use, and then shared as a Distributed Ledger Technology (DLT) over a Pier-to-Pier (P2P) network as a function of blockchain (Wylde et al. 2022b ). The authors created and put into use smart, secure fuzzy blockchain architecture. This framework makes use of a unique fuzzy DL model, improved adaptive neuro-fuzzy inference system (ANFIS)-based attack detection, fuzzy matching (FM), and fuzzy control system (FCS) for network attack detection (Yazdinejad et al. 2023 ).
Figure 11 illustrates the specification of blockchain technology concerning cloud environment. Blockchain is a distributed ledger across a peer-to-peer network. Blockchain features can help cloud services reach their full potential and address the many problems that arise. A collection of connected building blocks that are coupled and arranged in an appropriate linear sequence is used to keep a detailed record of all transactions. Decentralization, Security, transparency, availability, traceability, and many more are the essential features of blockchain technology which is highlighted by the figure presented by the author.
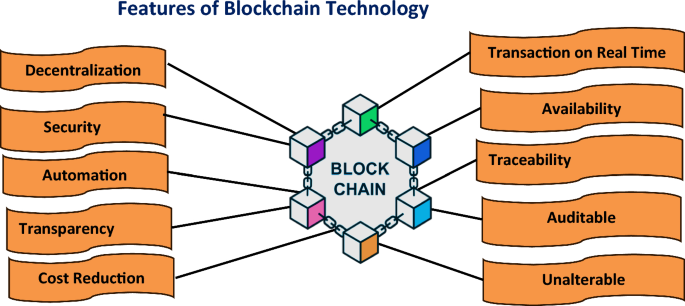
Specifications of blockchain technology
Decentralization Decentralization in blockchain technologies refers to the dividing of control and decision-making across the network users instead of concentrating on the centralized entity. It addresses the limitations of a centralized system in which security is compromised.
Security The network architecture of blockchain technology provides security by minimizing the risk of failure. The allocated characteristics of blockchain strengthen the security. Attacks on any nodes are less likely to put the entire network at risk.
Automation An intelligent system automates the carrying out of the consensus, and removes the requirement of human intervention. Smart contact enhances transaction efficiency. It automatically implements the terms and conditions of the agreement whenever conditions or terms are fulfilled.
Transparency The transactions made on blockchain appeared to every participant over the network. The method not only provides trust and security to the data but also promotes accountability which helps to gain the faith of the user.
Cost Reduction In conventional systems, the settlement of financial transactions might take several days, causing delays and capital lockups. Blockchain eliminates the need for drawn-out clearing and settlement procedures by enabling very immediate transaction settlement.
Transaction in Real Time Transactions in real time can be made over the network. Real-time transaction implements techniques like Proof-of-stake to attain quick acknowledgment of transactions. This technique permits fast agreement among nodes on the validity of transactions.
Availability Transaction availability guarantees a user’s ability to communicate with the network and complete transactions dependably. Availability may still be impacted by network maintenance, upgrades, and sporadic problems.
Traceability Traceability features of blockchain enable to provide of transparent transactions. The transaction can be can be traced by the user. Blockchain is helpful in industries where the origin, transportation, and ownership of assets need to be accurately recorded and validated because of its traceability capabilities.
Auditable Real-time transaction auditing is made possible by the blockchain ledger’s transparency and immutability. At any time, participants can check the transaction history.
Unalterable The ability of blockchain to keep a safe and impenetrable record of transactions is one of its unchangeable features. Once information is posted to the blockchain, it is impossible to change, guaranteeing the information’s integrity and immutability.
Figure 12 portrays the basic components of blockchain. These components work in agreement to form a secure ledger system. Blockchain technology comprises those elements that work in agreement to formulate a secure and decentralized ledger. Supply chain management, decentralized applications, voting systems, healthcare, and property registration are the major applications of technology. Each component plays an important role in blockchain functioning.
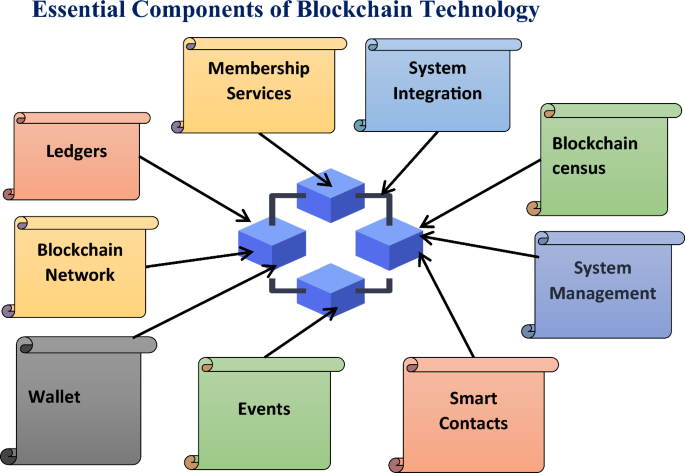
Basic building blocks for blockchain
Ledgers Ledgers in blockchain technology are used to maintain transparency of the record in transactions. Every node contains a replica of the complete ledger, protecting it from being altered or any kind of fraud. The ledger with the help of a chain of blocks carries out transactions; blocks represent every transaction in ledgers.
Blockchain Network In a Blockchain network, the user is referred to as nodes. All the users collectively validate the transaction and record the transaction in a synchronized manner. Blocks are depositors for a cluster of transactions. Blocks contain a timestamp, which is of location of preciously occurred transactions and a cryptographic has for the current blocks.
Wallet Blockchain technology wallets are tools that let users manage and store funds safely. It enables users to access the public and private keys, facilitating the blockchain’s ability to transfer and receive crypto-currency. There are two types of wallets Hot Wallets: Easy for frequent transactions and internet-connected. Cold wallets are offline and thought to be safer for storing money over time.
Events Events are essential for improving the automation, transparency, and usability of blockchain systems. They give decentralized networks a way to communicate and update in real time. The execution of smart contracts or modifications to the ledger’s current state is frequently linked to blockchain events.
Smart Contacts The blockchain records the complete history of smart contract execution, making it transparent and auditable. It has numerous applications such as in supply chain, finance, etc. Based on predetermined criteria, smart contracts carry out actions.
System Management Blockchain technology’s system management characteristics include a variety of operations and procedures meant to guarantee the safety, effectiveness, and appropriate operation of the blockchain network. These characteristics are essential to preserving the dependability and integrity of decentralized systems.
Blockchain Census The blockchain’s consensus techniques, like Proof of Work (PoW) and Proof of Stake (PoS), help make the system resistant to censorship. By requiring a distributed agreement from all network users, these mechanisms make it more difficult for one party to control or restrict transactions.
System Integration Establishing seamless connectivity between different blockchain networks and between blockchain technology and traditional systems is the aim of blockchain system integration. The successful communication and information sharing between diverse systems is greatly dependent upon standards, protocols, and APIs (Application Programming Interfaces).
Membership Services Membership services features of blockchain technology a functions and features for a member or participant management in a blockchain network. It is used to manage access control, rights, and user identity on the network. The elements of the blockchain ecosystem enhance its overall security, governance, and usefulness.
Figure 13 shows the internal workings of the blockchain technology which is used to perform any kind of transaction over the cloud securely. The figure above is a step-by-step explanation of how the transaction takes place over the cloud. In step 1 , first of all, the transaction is generated by any one of the users and request is the directed to the server for processing further. In step 2 , the server after receiving the transaction request creates a block that can appear for the transaction. Next step i.e. step 3 a chain or interconnect block is created using algorithms to authenticate the user and ensure that the request is being made by the authenticated user. Further, in step 4 , this block is distributed to other users or groups of users to grant permission for the transaction to happen. Once the group of users grants permission the transaction or block will be successfully added to the existing blocks that are shown in step 5 in the above figure. If any user disapproves or denies it, then the block will not be added to the existing chain. The modification that has taken place is permanent and cannot be modified further. Therefore, it ensures data security in the cloud environment.
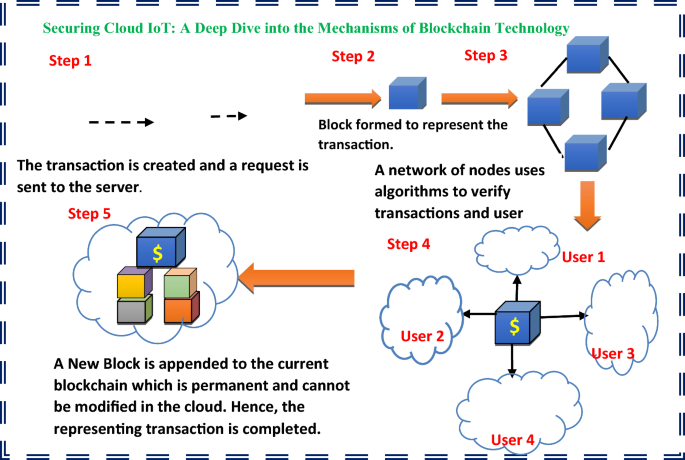
Functioning of blockchain technology in Cloud IoT systems
Real-World Applications of Blockchain Technology in Enhancing Security and Data Protection is as follows:
Walmart Walmart one of the retail companies collaborated with IBM to implement blockchain technology to track the movement of products, maintain food safety, and minimizes the possibility of contamination.
MedRec MedRec is an MIT-developed blockchain-based electronic medical record system that gives individuals more control over their health information while maintaining confidentiality and privacy.Allows for real-time transactions and decentralized energy management by utilizing blockchain to increase the security and efficiency of energy distribution.
Ripple Ripples operates in the financial sector. It uses blockchain techniques to protect the data and enables real-time secure payment.
Follow My Vote Follow My Vote creates a safe, open, and verifiable online voting system using blockchain technology.
uPort uPort is a blockchain-based self-governing identity platform that empowers people to take control of their online personas while improving security and privacy.
10 Unveiling the challenges: addressing current issues in data security and privacy within the Cloud IoT environment
10.1 open ended problems.
The open-ended problems and primary issues about data security and privacy in cloud IoT systems are summarized in Table 3 . Table 3 also provides targeted solutions to address each challenge, thereby ensuring a robust and secure cloud-IoT ecosystem.
10.2 Research gaps
The research gaps of data security and privacy preservation in cloud-IoT technologies are described in Table 4 .
11 Conclusions
The IoT is on the verge of substantial expansion, necessitating secure data transfer and robust cloud storage solutions. As IoT devices become more widespread, the need for enhanced cloud security is critical. Current methods, while helpful, do not fully address modern threats, thus requiring the development of more advanced protective systems. Manufacturers can improve security by creating products grounded in a detailed assessment of IoT security risks and objectives. Effective measures include the implementation of strong authentication methods like One Time Password (OTP) features and robust cryptographic systems. While Machine Learning (ML) is widely used for data protection in various sectors, it faces challenges such as scalability issues with small data sets. Integrating ML with homomorphic encryption shows promise but needs further development. The evolving sophistication of hackers compels reliance on ML and AI for defense strategies. Additionally, blockchain technology, supported by platforms like Ethereum and Hyper-ledger Fabric, offers considerable potential for enhancing security, though more research is necessary to standardize these techniques.
The authors recommend three key solutions:
Develop new security standards and frameworks for cloud-based and IoT devices to tackle modern security challenges.
Create more efficient ML models for real-time attack prediction.
Design robust privacy protection protocols for blockchain technology to safeguard sensitive data.
The authors encountered several limitations during their research, including restricted access to relevant literature, challenges in avoiding plagiarism, difficulties in summarizing a large body of research, integrating information logically, and keeping up with the latest studies.
Data availability
The data and material used in this paper are appropriately referred to and described in this paper.
Code availability
The source code/custom code/software application will be provided when required.
Abdulkader ZA (2022) Cloud data security mechanism using the lightweight cryptography. Optik 271:170084
Article Google Scholar
Abdulsalam YS, Hedabou M (2021) Decentralized data integrity scheme for preserving privacy in cloud computing. In 2021 International conference on security, pattern analysis, and cybernetics (SPAC), Chengdu, China, pp 607–612
Abed AK, Anupam A (2022) Review of security issues in the Internet of Things and artificial intelligence-driven solutions. Internet Technol Lett. https://doi.org/10.1002/spy2.285
Abouelmehdi K, Beni-Hessane A, Khaloufi H (2018) Big healthcare data: preserving security and privacy. J Big Data 5:1
Ahmed W et al (2021) Security in next generation mobile payment systems: a comprehensive survey. IEEE Access 9:115932–115950
Ahmad W, Rasool A, Javed AR, Baker T, Jalil Z (2022) Cyber security in IoT-based cloud computing: a comprehensive survey. Electronics 11:16
Akmal M, Syangtan B, Alchouemi A (2021) Enhancing the security of data in cloud computing environments using Remote Data Auditing. In: 2021 IEEE 6th International conference on innovative technology in intelligent system and industrial applications (CITISIA), Sydney, Australia, pp 1–10
Alabdulatif A, Thilakarathne NN, Kalinaki K (2023) A novel cloud enabled access control model for preserving the security and privacy of medical Big Data. Electronics 12:2646
Albugmi A, Alassafi MO, Walters R, Wills G (2016) Data security in cloud computing. 2016 Fifth International conference on future generation communication technologies (FGCT), London, UK, pp. 55–59
Al-Dhaqm A et al (2021) Digital forensics subdomains: the state of the art and future directions. IEEE Access 9:152476–152502
Al Hamid HA, Rahman SMM, Hossain MS, Almogren A, Alamri A (2017) A security model for preserving the privacy of medical Big Data in a healthcare cloud using a fog computing facility with pairing-based cryptography. IEEE Access 5:22313–22328
Ali J, Roh BH, Lee B, Oh J, Adil M (2020) A machine learning framework for prevention of software-defined networking controller from DDoS attacks and dimensionality reduction of Big Data. In: 2020 International conference on information and communication technology convergence (ICTC), Jeju, Korea (South), pp 515–519
Almutairi W, Moulahi T (2023) Joining federated learning to blockchain for digital forensics in IoT. Computers 12:157
Alnaim AK, Alwakeel AM (2023) Machine-learning-based IoT–edge computing healthcare solutions. Electron MDPI 12:1027
Google Scholar
Alouffi B, Hasnain M, Alharbi A, Alosaimi W, Alyami H, Ayaz M (2021) A systematic literature review on cloud computing security: threats and mitigation strategies. IEEE Access 9:57792–57807
Alrasheed SH, Aiedalhariri M, Adubaykhi SA, El Khediri S (2022) Cloud computing security and challenges: issues, threats, and solutions. In: 2022 5th Conference on cloud and Internet of Things (CIoT), Marrakech, Morocco, pp 166–172
Alzoubi YI, Ahmad AAA, Jaradat A (2021) Fog computing security and privacy issues, open challenges, and blockchain solution: an overview. Int J Electr Comput Eng (IJECE) 11(6):5081–5088
Andrew J, Karthikeyan J (2019) Privacy-preserving Internet of Things: techniques and applications. Int J Eng Adv Technol (IJEAT) 8(6):3229
Arora A, Khanna A, Rastogi A, Agarwal A (2017) Cloud security ecosystem for data security and privacy. In: 2017 7th International conference on cloud computing, data science & engineering - confluence, Noida, India, IEEE, pp 288–292
Atiewi S, Al-Rahayfeh AA, Almiani M, Yussof S, Alfandi O, Abugabah A, Jararweh Y (2020) Scalable and secure Big Data IoT system based on multifactor authentication and lightweight cryptography. IEEE Access 8:113498–113511
Awaysheh FM, Aladwan MN, Alazab M, Alawadi S, Cabaleiro JC, Pena TF (2022) Security by design for Big Data frameworks over cloud computing. IEEE Trans Eng Manage 69(6):3676–3693
Ayofe Azeez NA, Vyver CVD (2019) Security and privacy issues in e-health cloud-based system: a comprehensive content analysis. Egyptian Inform J 20(2):97–108
Basit A, Zafar M, Liu X et al (2021) A comprehensive survey of AI-enabled phishing attacks detection techniques. Telecommun Syst 76:139–154
Bedi RK, Singh J, Gupta SK (2021) An efficient and secure privacy-preserving multi-cloud storage framework for mobile devices. Int J Comput Appl 43:1–11
Bertino E (2016) Big Data security and privacy. In: 2016 IEEE International conference on Big Data (Big Data), Washington, DC, USA, pp 3–3
Binjubeir M, Ahmed AA, Ismail MAB, Sadiq AS, Khurram Khan M (2020) Comprehensive survey on Big Data privacy protection. IEEE Access 8:20067–20079
Butpheng C, Yeh K-H, Xiong H (2020) Security and privacy in IoT-cloud-based e-health systems—a comprehensive review. Symmetry MDPI 12:1191
Campos EM, Saura PF, González-Vidal A, Hernández-Ramos JL, Bernabé JB, Baldini G, Skarmeta A (2022) Evaluating federated learning for intrusion detection in Internet of Things: review and challenges. Comput Netw 203:108661
Cha SC, Hsu TY, Xiang Y, Yeh K-H (2019) Privacy enhancing technologies in the Internet of Things: perspectives and challenges. IEEE Internet Things J 6(2):2159–2187
Chaowei Y, Qunying H, Zhenlong L, Kai L, Fei H (2017) Big Data and cloud computing: innovation opportunities and challenges. Int J Digit Earth. https://doi.org/10.1080/17538947.2016.1239771
Chen J, Ramanathan L, Alazab M (2021) Holistic Big Data integrated artificial intelligent modelling to improve privacy and security in data management of smart cities. Microprocess Microsyst 81:103722
Chen Q, Wu L, Jiang C (2022) ES-PPDA: an efficient and secure privacy-protected data aggregation scheme in the IoT with an edge-based XaaS architecture. J Cloud Comp 11:20
Chenthara S, Ahmed K, Wang H, Whittaker F (2019) Security and privacy-preserving challenges of e-health solutions in cloud computing. IEEE Access 7:74361–74382
Choudhury T, Gupta A, Pradhan S, Kumar P, Rathore YS (2017) Privacy and security of Cloud-Based Internet of Things (IoT). In: 2017 3rd International conference on computational intelligence and networks (CINE), Odisha, India, pp 40–45
Duan H, Zheng Y, Wang C, Yuan X (2019) Treasure collection on foggy islands: building secure network archives for Internet of Things. IEEE Internet Things J 6(2):2637–2650
Dutkiewicz L et al (2022) Privacy-preserving techniques for trustworthy data sharing: opportunities and challenges for future research. In: Curry E, Scerri S, Tuikka T (eds) Data spaces. Springer, Cham
Gai K, Qiu M, Zhao H (2021) Privacy-preserving data encryption strategy for Big Data in mobile cloud computing. IEEE Transact Big Data 7(4):678–688
Ghaffar Z, Ahmed S, Mahmood K, Islam SH, Hassan MM, Fortino G (2020) An improved authentication scheme for remote data access and sharing over cloud storage in cyber-physical-social-systems. IEEE Access 8:47144–47160
Gnana Sophia S, Thanammal KK, Sujatha SS (2023) Secure storage and accessing the data in the cloud using optimized homomorphic encryption. J Control Decision. https://doi.org/10.1080/23307706.2022.2078436
Gupta I, Singh AK, Lee C-N, Buyya R (2022) Cloud computing research center, secure data storage and sharing techniques for data protection in cloud environments: a systematic review, analysis, and future directions. IEEE Access. https://doi.org/10.1109/ACCESS.2022.3188110
Hamzah Amlak GM, Kraidi Al-Saedi KH (2023) Data mining techniques for cloud privacy preservation. Int J Intell Syst Appl Eng 11(6s):246–256
Hassija V, Chamola V, Saxena V, Jain D, Goyal P, Sikdar B (2019) A survey on IoT security: application areas, security threats, and solution architectures. IEEE Access 7:82721–82743
Henze M, Wolters B, Matzutt R, Zimmermann T, Wehrle K (2017) Distributed configuration, authorization and management in the cloud-based Internet of Things. 2017 IEEE Trustcom/BigDataSE/ICESS, Sydney, NSW, Australia, pp 185–192
Himeur Y, Sohail SS, Bensaali F, Amira A, Alazab M (2022) Latest trends of security and privacy in recommender systems: a comprehensive review and future perspectives. Comput Secur 118:102746
Hiremath S, Kunte S (2017) A novel data auditing approach to achieve data privacy and data integrity in cloud computing. In: 2017 International conference on electrical, electronics, communication, computer, and optimization techniques (ICEECCOT), Mysuru, India, pp 306–310
Hong-Yen T, Jiankun H (2019) Privacy-preserving Big Data analytics a comprehensive survey. J Parallel Distribut Comput 134:207–218
Hossain MS, Muhammad G, Abdul W, Song B, Gupta BB (2018) Cloud-assisted secure video transmission and sharing framework for smart cities. Futur Gener Comput Syst 83:596–606
Hou Y, Garg S, Hui L, Jayakody DNK, Jin R, Hossain MS (2020) A data security enhanced access control mechanism in mobile edge computing. IEEE Access 8:136119–136130
Hurrah NN, Parah SA, Sheikh JA, Al-Turjman F, Muhammad K (2019) Secure data transmission framework for confidentiality in IoTs. Ad Hoc Netw 95:101989
Ishaq A, Qadeer B, Shah MA, Bari N (2021) A comparative study on securing electronic health records (EHR) in cloud computing. In: 2021 26th International conference on automation and computing (ICAC), Portsmouth, United Kingdom, pp 1–7
Jahromi AN, Karimipour H, Dehghantanha A, Choo K-KR (2021) Toward detection and attribution of cyber-attacks in iot-enabled cyber-physical systems. IEEE Internet Things J 8(17):13712–13722
Jain SK, Kesswani N (2023) A noise-based privacy-preserving model for the Internet of Things. Complex Intell Syst 9:3655–3679
Jain P, Gyanchandani M, Khare N (2016) Big Data privacy: a technological perspective and review. J Big Data 3:25
Jain P, Gyanchandani M, Khare N (2019) Enhanced secured map reduce layer for Big Data privacy and security. J Big Data 6:30
Javeed D, Gao T, Saeed MS, Khan MT (2023) FOG-Empowered augmented-intelligence-based proactive defensive mechanism for IoT-enabled smart industries. IEEE Internet Things J 10(21):18599–18608. https://doi.org/10.1109/JIOT.2023.3288563
Javeed D, Saeed MS, Ahmad I, Adil M, Kumar P, Najmul Islam AKM (2024a) Quantum-empowered federated learning and 6G wireless networks for IoT security: Concept, challenges and future directions. Futur Gener Comput Syst 160:577–597. https://doi.org/10.1016/j.future.2024.06.023
Javeed D, Saeed MS, Adil M, Kumar P, Jolfaei A (2024b) A federated learning-based zero trust intrusion detection system for Internet of Things. Ad Hoc Netw 162:103540. https://doi.org/10.1016/j.adhoc.2024.103540
Javid T, Faris M, Beenish H, Fahad M (2020) Cybersecurity and data privacy in the cloudlet for preliminary healthcare Big Data analytics. In: 2020 International Conference on Computing and Information Technology (ICCIT-1441), Tabuk, Saudi Arabia, pp 1–4
Jeong J, Joo JWJ, Lee Y, Son Y (2019) Secure cloud storage service using bloom filters for the Internet of Things. IEEE Access 7:60897–60907
Jiang Q, Kumar N, Ma J, Shen J, He D, Chilamkurti N (2016) A privacy-aware two-factor authentication protocol based on elliptic curve cryptography for wireless sensor networks. Int J Network Mgmt. https://doi.org/10.1002/nem.1937
Jusak J, Mahmoud SS, Laurens R, Alsulami M, Fang Q (2022) A new approach for secure cloud-based electronic health record and its experimental testbed. IEEE Access 10:1082–1095
Kaaniche N, Laurent M (2017) Data security and privacy preservation in cloud storage environments based on cryptographic mechanisms. Comput Commun 111:120–141
Kabir AA, Elmedany M, Sharif W, Saeed M (2023) Securing IoT devices against emerging security threats: challenges and mitigation techniques. J Cyber Secur Technol. https://doi.org/10.1080/23742917.2023.2228053
Karie NM, Sahri NM, Yang W, Valli C, Kebande VR (2021) A review of security standards and frameworks for IoT-based smart environments. IEEE Access 9:121975–121995
Kaur K, Syed A, Mohammad A, Halgamuge MN (2017) Review: an evaluation of major threats in cloud computing associated with Big Data. In: 2017 IEEE 2nd International conference on Big Data analysis (ICBDA), Beijing, China, pp 368–372
Khan S, Parkinson S, Qin Y (2017) Fog computing security: a review of current applications and security solutions. J Cloud Comp 6:19
Khan HK, Pradhan R, Chandavarkar BR (2021) Hybrid cryptography for cloud computing. In: 2021 2nd International conference for emerging technology (INCET), Belagavi, India, pp 1–5
Krishnaraj N, Sangeetha S (2022) A study of data privacy in Internet of Things using privacy preserving techniques with its management. Int J Eng Trends Technol 70(3):54–65
Kumar S, Tiwari P, Zymbler M (2019) Internet of Things is a revolutionary approach for future technology enhancement: a review. J Big Data 6:111
Kumar A (2021) Framework for data security using DNA cryptography and HMAC technique in cloud computing. In: 2021 Second International conference on electronics and sustainable communication systems (ICESC), Coimbatore, India, pp 898-903
Kumar V, Alameemi AMA, Kumari A, Ahmad M, Falah MW, Abd El-Latif AA (2022) PSEBVC: provably secure ECC and biometric based authentication framework using smartphone for vehicular cloud environment. IEEE Access 10:84776–84789
Kumar A, Khan SB, Pandey SK et al (2023) Development of a cloud-assisted classification technique for the preservation of secure data storage in smart cities. J Cloud Comp 12:92
Li Y, Zhang F (2022) An efficient certificate-based data integrity auditing protocol for cloud-assisted WBANs. IEEE Internet Things J 9(13):11513–11523
Lin J, Yu W, Zhang N, Yang X, Zhang H, Zhao W (2017) A survey on Internet of Things: architecture, enabling technologies, security and privacy, and applications. IEEE Internet Things J 4(5):1125–1142
Loai AT, Gokay S (2021) Reconsidering Big Data security and privacy in cloud and mobile cloud systems. J King Saud Univ Comput Inform Sci 33(7):810–819
Lone AN, Mustajab S, Alam M (2023) A comprehensive study on cybersecurity challenges and opportunities in the IoT world. Secur Privacy 6:e318
Lu X, Pan Z, Xian H (2020) An efficient and secure data sharing scheme for mobile devices in cloud computing. J Cloud Comp 9:60
Mahfoudhi S, Frehat M, Moulahi T (2019) Enhancing cloud of things performance by avoiding unnecessary data through artificial intelligence tools. In: 2019 15th International wireless communications & mobile computing conference (IWCMC), Tangier, Morocco, pp 1463–1467
Mahrous WA, Farouk M, Darwish SM (2021) An enhanced blockchain-based IoT digital forensics architecture using fuzzy hash. IEEE Access 9:151327–151336
Majeed A, Khan S, Hwang SO (2022) Toward privacy preservation using clustering based anonymization: recent advances and future research outlook. IEEE Access 10:53066–53097
Mei R, Yan HB, He Y, Wang Q, Zhu S, Wen W (2022). Considerations on evaluation of practical cloud data protection. CONCERT 2022. In: Communications in computer and information science, vol 1699. Springer, Singapore
Mihailescu MI, Nita SL, Asalomia BL, Rogobete MG, Racuciu C (2022) Customized authorization process for cloud computing and IoT using attribute-based encryption. In: 2022 14th International conference on electronics, computers and artificial intelligence (ECAI), IEEE Ploiesti, Romania, pp 1–4
Mishra JK, Janarthanan MC (2023) Cloud computing security: machine and deep learning models analysis. Macromol Symp 407:2100521
Mishra K, Bhattacharjee V, Saket S et al (2022) Cloud and Big Data security system’s review principles: a decisive investigation. Wireless Pers Commun 126:1013–1050
Mishra A, Jabar TS, Alzoubi YI, Mishra KN (2023) Enhancing privacy-preserving mechanisms in cloud storage: a novel conceptual framework. Concurr Computat Pract Exper. https://doi.org/10.1002/cpe.7831
Moqurrab SA, Tariq N, Anjum A et al (2022) A Deep learning-based privacy-preserving model for smart healthcare in Internet of medical things using fog computing. Wireless Pers Commun 126:2379–2401
Morioka E, Sharbaf MS (2016) Digital forensics research on cloud computing: An investigation of cloud forensics solutions. In: 2016 IEEE symposium on technologies for homeland security (HST), Waltham, MA, USA, pp 1–6
Moulahi T, El Khediri S, Ullah Khan R, Zidi S (2021) A fog computing data reduction level to enhance the cloud of things performance. Int J Commun Syst 34(9):e4812
Muzammal SM et al (2018) Counter measuring conceivable security threats on smart healthcare devices. IEEE Access 6:20722–20733
Nadian-Ghomsheh A, Farahani B, Kavian M (2021) A hierarchical privacy-preserving IoT architecture for vision-based hand rehabilitation assessment. Multimed Tools Appl 80:31357–31380
Namakshenas D, Yazdinejad A, Dehghantanha A, Srivastava G (2024) Federated quantum-based privacy-preserving threat detection model for consumer Internet of Things. IEEE Trans Consum Electron. https://doi.org/10.1109/TCE.2024.3377550
Nanda P, He X, Yang LT (2020) Security, trust and privacy in cyber (STPCyber): future trends and challenges. Futur Gener Comput Syst 109:446–449
Nasiraee H, Ashouri-Talouki M (2022) Privacy-preserving distributed data access control for CloudIoT. IEEE Trans Dependable Secure Comput 19(4):2476–2487
Navin Prasad S, Rekha C (2023) Blockchain-based IAS protocol to enhance security and privacy in cloud computing. Measur Sens 28:100813
Niu L, Wang F, Li J, Han T, Liu D (2019) Development of agricultural Internet of Things monitoring system combining cloud computing and WeChat technology. In: 2019 IEEE 8th Joint international information technology and artificial intelligence conference (ITAIC), Chongqing, China, pp 1457–1460
Ogunniye G, Kokciyan N (2023) A survey on understanding and representing privacy requirements in the Internet-of-Things. J Art Intell Res 76:163–192
Pandey NK, Kumar K, Saini G et al (2023) Security issues and challenges in a cloud of things-based applications for industrial automation. Ann Oper Res. https://doi.org/10.1007/s10479-023-05285-7
Pathak M, Mishra KN, Singh SP, Mishra A (2023) An automated smart centralised vehicle security system for controlling the vehicle thefts/hacking using IOT and facial recognition. In: 2023 International conference on computational intelligence and knowledge economy (ICCIKE), Dubai, United Arab Emirates, pp 516–521
Pawlicki M, Pawlicka A, Kozik R, Choraś M (2023) The survey and meta-analysis of the attacks, transgressions, countermeasures, and security aspects common to the Cloud Edge and IoT. Neurocomputing 551:126533
Pioli L, Dorneles CF, de Macedo DDJ et al (2022) An overview of data reduction solutions at the edge of IoT systems: a systematic mapping of the literature. Computing 104:1867–1889
Quach S, Thaichon P, Martin KD et al (2022) Digital technologies: tensions in privacy and data. J of the Acad Mark Sci 50:1299–1323
Rachit BS, Ragiri PR (2021) Security trends in Internet of Things: a survey. SN Appl Sci 3:121
Radoglou Grammatikis PI, Sarigiannidis PG, Moscholios ID (2019) Securing the Internet of Things: challenges, threats and solutions. Internet of Things 5:41–70
Rahman SMM, Hossain MA, Hassan MM, Alamri A, Alghamdi A, Pathan M (2016) Secure privacy vault design for distributed multimedia surveillance system. Futur Gener Comput Syst 55:344–352
Ram Mohan P, Murali Krishna S, Siva Kumar AP (2018) Privacy preservation techniques in Big Data analytics: a survey. J Big Data 5:33
Ravi Kumar P, Herbert Raj P, Jelciana P (2018) Exploring data security issues and solutions in cloud computing. Procedia Comput Sci 125:691–697
Ray SM, Dutta S (2020) Big Data security issues from the perspective of IoT and cloud computing: a review. Recent Adv Comput Sci Commun. https://doi.org/10.2174/2666255813666200224092717
Reddy Y (2018) Big Data security in cloud environment. In: 2018 IEEE 4th International Conference on Big Data Security on Cloud (BigDataSecurity), IEEE International conference on high performance and smart computing, (HPSC) and IEEE international conference on intelligent data and security (IDS), Omaha, NE, USA, pp 100–106
Rejin PR, Paul RD, Alavi AH (2019) Verification of data integrity and co-operative loss recovery for secure data storage in cloud computing. Cogent Eng. https://doi.org/10.1080/23311916.2019.1654694
Rodríguez E, Otero B, Canal R (2023) A survey of machine and deep learning methods for privacy protection in the Internet of Things. Sensors 23:1252
Roslin Dayana K, Shobha Rani P (2023) Secure cloud data storage solution with better data accessibility and time efficiency. Automatika J Control Measur Electron Comput Commun 64(4):751–758
Sadhu PK, Yanambaka VP, Abdelgawad A (2022) Internet of Things: security and solutions survey. MDPI Sens 22:7433
Safaei Yaraziz M et al (2023) Recent trends towards privacy-preservation in the Internet of Things, its challenges and future directions. IET Circuits Devices Syst 17(2):53–61
Sakhnini J et al (2023) A generalizable deep neural network method for detecting attacks in industrial cyber-physical systems. IEEE Syst J 17(4):5152–5160
Sarwar K, Yongchareon S, Jian Yu, Rehman SU (2021) A survey on privacy preservation in fog-enabled Internet of Things. ACM Comput Surv 55(1):2
Schiller E, Andy A, Jara F, Jonathan S, Michael Z, Burkhard S (2022a) Landscape of IoT security. Comput Sci Rev 44:100467
Schiller E, Aidoo A, Fuhrer J, Stahl J, Ziörjen M, Stiller B (2022b) Landscape of IoT security. Comput Sci Rev Internet Things 44:100467
Selvarajan S, Srivastava G, Khadidos AO et al (2023) An artificial intelligence lightweight blockchain security model for security and privacy in IIoT systems. J Cloud Comp 12:38
Sharma Y, Gupta H and Khatri S. K. (2019) A Security Model for the Enhancement of Data Privacy in Cloud Computing. 2019 Amity international conference on artificial intelligence (AICAI), Dubai, United Arab Emirates, IEEE, pp 898–902
Shi Y (2018) Data security and privacy protection in public cloud. In 2018 IEEE International Conference on Big Data (Big Data), Seattle, WA, USA, pp 4812–4819
Shin S, Kwon T (2020) A privacy-preserving authentication, authorization, and key agreement scheme for wireless sensor networks in 5G-integrated Internet of Things. IEEE Access 8:67555–67571
Shukla RS (2022) IoT based designing of secure data storage system in distributed cloud system with Big Data using cryptography algorithm. In: 2022 11th International conference on system modeling & advancement in research trends (SMART), Moradabad, India, pp 264-270
Sicari S, Rizzardi A, Coen-Porisini A (2022) Insights into security and privacy towards fog computing evolution. Comput Secur 120:102822
Silva LV, Barbosa P, Marinho R (2018) Security and privacy aware data aggregation on cloud computing. J Internet Serv Appl 9:6
Simsek I (2023) Zero-knowledge and identity-based authentication, authorization, access control, and key exchange for publish/subscribe in Internet of Things. In: 2023 6th conference on cloud and Internet of Things (CIoT), Lisbon, Portugal, pp 47–54
Singh N, Singh AK (2018) Data privacy protection mechanisms in cloud. Data Sci Eng 3:24–39
Sookhak M, Yu FR, Zomaya AY (2018) Auditing Big Data storage in cloud computing using divide and conquer tables. IEEE Trans Parallel Distrib Syst 29(5):999–1012
Stergiou C, Psannis KE, Xifilidis T, Plageras AP, Gupta BB (2018) Security and privacy of Big Data for social networking services in the cloud. IEEE INFOCOM 2018—IEEE conference on computer communications workshops (INFOCOM WKSHPS), Honolulu, HI, USA, pp 438–443
Sumithra R, Parameswari R (2022) Data privacy and data protection security algorithms for Big Data in the cloud. Int J Health Sci 6(S2):7613–7621
Sun PJ (2019) Privacy protection and data security in cloud computing: a survey, challenges, and solutions. IEEE Access 7:147420–147452
Tahirkheli AI, Shiraz M, Hayat B, Idrees M, Sajid A, Ullah R, Ayub N, Kim K-I (2021) A survey on modern cloud computing security over smart city networks: threats, vulnerabilities, consequences, countermeasures, and challenges. Electronics 10:1811
Tang Z (2020) A preliminary study on data security technology in Big Data cloud computing environment. In: 2020 International conference on Big Data & artificial intelligence & software engineering (ICBASE) IEEE, Bangkok, Thailand, pp 27–30
Thabit F, Alhomdy S, Jagtap S (2021) A new data security algorithm for cloud computing based on genetics techniques and logical-mathematical functions. Int J Intell Netw Sci Direct 2:18–33
Tian Y, Kaleemullah MM, Rodhaan MA, Song B, Al-Dhelaan A, Ma T (2019) A privacy-preserving location service for cloud-of-things system. J Parallel Distrib Comput 123:215–222
Ullah F et al (2019) Cyber security threats detection in Internet of Things using deep learning approach. IEEE Access 7:124379–124389
Unal E, Sen-Baidya S, Hewett R (2018) Towards prediction of security attacks on software defined networks: a Big Data analytic approach. In: 2018 IEEE International conference on Big Data (Big Data), Seattle, WA, USA, pp 4582–4588
Waheed N, He X, Ikram M, Usman M, Hashmi SS, Usman M (2020) Security and privacy in IoT using machine learning and blockchain: threats and countermeasures. ACM Comput Surv 53(6):122
Wang H (2021) Research on risk and supervision of financial Big Data application based on cloud computing. In: 2021 IEEE International conference on advances in electrical engineering and computer applications (AEECA), Dalian, China, pp 507–510
Wang F, Wang H, Xue L (2021) Research on data security in Big Data cloud computing environment. In: 2021 IEEE 5th advanced information technology, electronic and automation control conference (IAEAC), Chongqing, China, pp 1446–1450
Wang Y, Ni K, Wang X, Zhu J (2022) Design of automatic weather monitoring and forecasting system based on Internet of Things and Big Data. In: 2022 International conference on sustainable computing and data communication systems (ICSCDS), Erode, India, pp 979–982
Wazid M, Das AK, Hussain R, Succi G, Rodrigues JJPC (2019) Authentication in cloud-driven IoT-based Big Data environment: survey and outlook. J Syst Architect 97:185–196
Williams P, Dutta IK, Daoud H, Bayoumi M (2022) A survey on security in the Internet of Things with a focus on the impact of emerging technologies. Internet Things 19:100564
Wylde V, Rawindaran N, Lawrence J et al (2022a) Cybersecurity, data privacy, and blockchain: a review. SN Comput Sci 3:127
Wylde V, Rawindaran N, Lawrence J, Balasubramanian R, Prakash E, Jayal A, Khan I, Hewage C, Platts J (2022b) Cybersecurity, data privacy, and blockchain: a review. SN Comput Sci 3:127
Xiao Y, Jia Y, Liu C, Cheng X, Yu J, Lv W (2019) Edge computing security: state of the art and challenges. Proc IEEE 107(8):1608–1631
Xie Q, Zhang C, Jia X (2023) Security-aware and efficient data deduplication for edge-assisted cloud storage systems. IEEE Trans Serv Comput 16(03):2191–2202
Yahuza M et al (2020) Systematic review on security and privacy requirements in edge computing: state of the art and future research opportunities. IEEE Access 8:76541–76567
Yan H, Gui W (2021) Efficient identity-based public integrity auditing of shared data in cloud storage with user privacy preserving. IEEE Access 9:45822–45831
Yao H (2022) Data storage security system based on cloud computing. In: 2022 IEEE 2nd International conference on electronic technology, communication and information (ICETCI), Changchun, China, pp 1220–1223
Yazdinejad A, Dehghantanha A, Parizi RM, Hammoudeh M, Karimipour H, Srivastava G (2022) Block hunter: federated learning for cyber threat hunting in blockchain-based IIoT networks. IEEE Trans Industr Inf 18(11):8356–8366
Yazdinejad A, Dehghantanha A, Parizi RM, Srivastava G, Karimipour H (2023) Secure intelligent fuzzy blockchain framework: effective threat detection in IoT networks. Comput Ind 144:2023
Yazdinejad A, Dehghantanha A, Srivastava G (2024a) AP2FL: auditable privacy-preserving federated learning framework for electronics in healthcare. IEEE Trans Consum Electron 70(1):2527–2535
Yazdinejad A, Dehghantanha A, Srivastava G, Karimipour H, Parizi RM (2024b) Hybrid privacy-preserving federated learning against irregular users in next-generation Internet of Things. J Syst Architect 148:103088
Ye C, Cao W, Chen S (2021) Security challenges of blockchain in Internet of Things: systematic literature review. Trans Emerging Tel Tech 32:e4177
Yin H, Chen E, Zhu Y, Zhao C, Feng R, Yau SS (2022) Attribute-based private data sharing with script-driven programmable ciphertext and decentralized key management in blockchain Internet of Things. IEEE Internet Things J 9(13):10625–10639
Yu Y et al (2017) Identity-based remote data integrity checking with perfect data privacy preserving for cloud storage. IEEE Trans Inf Forensics Secur 12(4):767–778
Yu K et al (2022) A blockchain-based shamir’s threshold cryptography scheme for data protection in industrial Internet of Things settings. IEEE Internet Things J 9(11):8154–8167
Zaman S et al (2021) Security threats and artificial intelligence based countermeasures for Internet of Things networks: a comprehensive survey. IEEE Access 9:94668–94690
Zarandi MA, Dara Rozita A, Evan F (2020) A survey of machine learning-based solutions to protect privacy in the Internet of Things. Comput Secur 96:101921
Zhang J, Chen B, Zhao Y, Cheng X, Hu F (2018) Data security and privacy-preserving in edge computing paradigm: survey and open issues. IEEE Access 6:18209–18237
Zhang W, Jin S (2020) Research and application of data privacy protection technology in cloud computing environment based on attribute encryption. In: 2020 IEEE International conference on power, intelligent computing and systems (ICPICS), Shenyang, China, pp 994–996
Zhao X-P, Jiang R (2020) Distributed machine learning oriented data integrity verification scheme in cloud computing environment. IEEE Access 8:26372–26384
Zhou J, Cao Z, Dong X, Vasilakos AV (2017) Security and privacy for cloud-based IoT: challenges. IEEE Commun Mag 55(1):26–33
Zhu H et al (2019) A secure and efficient data integrity verification scheme for Cloud-IoT based on short signature. IEEE Access 7:90036–90044
Download references
Author information
Authors and affiliations.
Department of Computer Science & Engineering, Birla Institute of Technology, Jharkhand, India
Mayank Pathak, Kamta Nath Mishra & Satya Prakash Singh
You can also search for this author in PubMed Google Scholar
Contributions
Mayank Pathak, Kamta Nath Mishra and Satya Prakash Singh have equally contributed in writing this paper after having various discussions.
Corresponding author
Correspondence to Kamta Nath Mishra .
Ethics declarations
Conflicts of interest.
Being the corresponding author I declare that there is no conflict of interest with any person or organization for this paper.
Additional information
Publisher's note.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/ .
Reprints and permissions
About this article
Pathak, M., Mishra, K.N. & Singh, S.P. Securing data and preserving privacy in cloud IoT-based technologies an analysis of assessing threats and developing effective safeguard. Artif Intell Rev 57 , 269 (2024). https://doi.org/10.1007/s10462-024-10908-x
Download citation
Accepted : 06 August 2024
Published : 27 August 2024
DOI : https://doi.org/10.1007/s10462-024-10908-x
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Blockchain technologies
- Cloud computing
- Data breach
- Data securities
- Digital forensic
- Fog computing
- Internet of Things
- Machine learning
- Privacy protection
- Find a journal
- Publish with us
- Track your research
MIT Technology Review
- Newsletters
The rise of the data platform for hybrid cloud
A move from siloed storage to data platforms unleashes the potential of AI-driven business.
- MIT Technology Review Insights archive page
In partnership with Hitachi Vantara
Whether pursuing digital transformation, exploring the potential of AI, or simply looking to simplify and optimize existing IT infrastructure, today’s organizations must do this in the context of increasingly complex multi-cloud environments. These complicated architectures are here to stay—2023 research by Enterprise Strategy Group , for example, found that 87% of organizations expect their applications to be distributed across still more locations in the next two years.

Scott Sinclair, practice director at Enterprise Strategy Group, outlines the problem: “Data is becoming more distributed. Apps are becoming more distributed. The typical organization has multiple data centers, multiple cloud providers, and umpteen edge locations. Data is all over the place and continues to be created at a very rapid rate.”
Finding a way to unify this disparate data is essential. In doing so, organizations must balance the explosive growth of enterprise data; the need for an on-premises, cloud-like consumption model to mitigate cyberattack risks; and continual pressure to cut costs and improve performance.
Sinclair summarizes: “What you want is something that can sit on top of this distributed data ecosystem and present something that is intuitive and consistent that I can use to leverage the data in the most impactful way, the most beneficial way to my business.”
For many, the solution is an overarching software-defined, virtualized data platform that delivers a common data plane and control plane across hybrid cloud environments. Ian Clatworthy, head of data platform product marketing at Hitachi Vantara, describes a data platform as “an integrated set of technologies that meets an organization’s data needs, enabling storage and delivery of data, the governance of data, and the security of data for a business.”
Gartner projects that these consolidated data storage platforms will constitute 70% of file and object storage by 2028, doubling from 35% in 2023. The research firm underscores that “Infrastructure and operations leaders must prioritize storage platforms to stay ahead of business demands.”

A transitional moment for enterprise data
Historically, organizations have stored their various types of data—file, block, object—in separate silos. Why change now? Because two main drivers are rendering traditional data storage schemes inadequate for today’s business needs: digital transformation and AI.
As digital transformation initiatives accelerate, organizations are discovering that having distinct storage solutions for each workload is inadequate for their escalating data volumes and changing business landscapes. The complexity of the modern data estate hinders many efforts toward change.
Clatworthy says that when organizations move to hybrid cloud environments, they may find, for example, that they have mainframe or data center data stored in one silo, block storage running on an appliance, apps running file storage, another silo for public cloud, and a separate VMware stack. The result is increased complexity and cost in their IT infrastructure, as well as reduced flexibility and efficiency.
Then, Clatworthy adds, “When we get to the world of generative AI that’s bubbling around the edges, and we’re going to have this mass explosion of data, we need to simplify how that data is managed so that applications can consume it. That’s where a platform comes in.”

Download the full report .

How to break free of Spotify’s algorithm
By delivering what people seem to want, has Spotify killed the joy of music discovery?
- Tiffany Ng archive page

Move over, text: Video is the new medium of our lives
We are increasingly learning and communicating by means of the moving image. It will shift our culture in untold ways.
- Clive Thompson archive page

Inside the long quest to advance Chinese writing technology
Two books on Chinese writing illustrate how tumultuous technological evolution can be.
- Veronique Greenwood archive page

Happy birthday, baby! What the future holds for those born today
An intelligent digital agent could be a companion for life—and other predictions for the next 125 years.
- Kara Platoni archive page
Stay connected
Get the latest updates from mit technology review.
Discover special offers, top stories, upcoming events, and more.
Thank you for submitting your email!
It looks like something went wrong.
We’re having trouble saving your preferences. Try refreshing this page and updating them one more time. If you continue to get this message, reach out to us at [email protected] with a list of newsletters you’d like to receive.
- Search for: Toggle Search
AI Chases the Storm: New NVIDIA Research Boosts Weather Prediction, Climate Simulation
As hurricanes, tornadoes and other extreme weather events occur with increased frequency and severity, it’s more important than ever to improve and accelerate climate research and prediction using the latest technologies.
Amid peaks in the current Atlantic hurricane season, NVIDIA Research today announced a new generative AI model, dubbed StormCast, for emulating high-fidelity atmospheric dynamics. This means the model can enable reliable weather prediction at mesoscale — a scale larger than storms but smaller than cyclones — which is critical for disaster planning and mitigation.
Detailed in a paper written in collaboration with the Lawrence Berkeley National Laboratory and the University of Washington, StormCast arrives as extreme weather phenomena are taking lives, destroying homes and causing more than $150 billion in damage annually in the U.S. alone.
It’s just one example of how generative AI is supercharging thundering breakthroughs in climate research and actionable extreme weather prediction, helping scientists tackle challenges of the highest stakes: saving lives and the world.
NVIDIA Earth-2 — a digital twin cloud platform that combines the power of AI, physical simulations and computer graphics — enables simulation and visualization of weather and climate predictions at a global scale with unprecedented accuracy and speed.

In Taiwan , for example, the National Science and Technology Center for Disaster Reduction plans to predict fine-scale details of typhoons using CorrDiff , an NVIDIA generative AI model offered as part of Earth-2.
CorrDiff can super-resolve 25-kilometer-scale atmospheric data by 12.5x down to 2 kilometers — 1,000x faster and using 3,000x less energy for a single inference than traditional methods.
That means the center’s potentially lifesaving work, which previously cost nearly $3 million on CPUs, can be accomplished using about $60,000 on a single system with an NVIDIA H100 Tensor Core GPU . It’s a massive reduction that shows how generative AI and accelerated computing increase energy efficiency and lower costs.
The center also plans to use CorrDiff to predict downwash — when strong winds funnel down to street level, damaging buildings and affecting pedestrians — in urban areas.
Now, StormCast adds hourly autoregressive prediction capabilities to CorrDiff, meaning it can predict future outcomes based on past ones.
A Global Impact From a Regional Focus
Global climate research begins at a regional level.
Physical hazards of weather and climate change can vary dramatically on regional scales. But reliable numerical weather prediction at this level comes with substantial computational costs. This is due to the high spatial resolution needed to represent the underlying fluid-dynamic motions at mesoscale.
Regional weather prediction models — often referred to as convection-allowing models, or CAMs — have traditionally forced researchers to face varying tradeoffs in resolution, ensemble size and affordability.
CAMs are useful to meteorologists for tracking the evolution and structure of storms, as well as for monitoring its convective mode, or how a storm is organized when it forms. For example, the likelihood of a tornado is based on a storm’s structure and convective mode.
CAMs also help researchers understand the implications for weather-related physical hazards at the infrastructure level.
For example, global climate model simulations can be used to inform CAMs, helping them translate slow changes in the moisture content of large atmospheric rivers into flash-flooding projections in vulnerable coastal areas.
At lower resolutions, machine learning models trained on global data have emerged as useful emulators of numerical weather prediction models that can be used to improve early-warning systems for severe events. These machine learning models typically have a spatial resolution of about 30 kilometers and a temporal resolution of six hours.
Now, with the help of generative diffusion, StormCast enables this at a 3-kilometer, hourly scale.
Despite being in its infancy, the model — when applied with precipitation radars — already offers forecasts with lead times of up to six hours that are up to 10% more accurate than the U.S. National Oceanic and Atmospheric Administration (NOAA)’s state-of-the-art 3-kilometer operational CAM.
Plus, outputs from StormCast exhibit physically realistic heat and moisture dynamics, and can predict over 100 variables, such as temperature, moisture concentration, wind and rainfall radar reflectivity values at multiple, finely spaced altitudes. This enables scientists to confirm the realistic 3D evolution of a storm’s buoyancy — a first-of-its-kind accomplishment in AI weather simulation.
NVIDIA researchers trained StormCast on approximately three-and-a-half years of NOAA climate data from the central U.S., using NVIDIA accelerated computing to speed calculations.
More Innovations Brewing
Scientists are already looking to harness the model’s benefits.
“Given both the outsized impacts of organized thunderstorms and winter precipitation, and the major challenges in forecasting them with confidence, the production of computationally tractable storm-scale ensemble weather forecasts represents one of the grand challenges of numerical weather prediction,” said Tom Hamill, head of innovation at The Weather Company. “StormCast is a notable model that addresses these challenges, and The Weather Company is excited to collaborate with NVIDIA on developing, evaluating and potentially using these deep learning forecast models.”
“Developing high-resolution weather models requires AI algorithms to resolve convection, which is a huge challenge,” said Imme Ebert-Uphoff, machine learning lead at Colorado State University’s Cooperative Institute for Research in the Atmosphere. “The new NVIDIA research explores the potential of accomplishing this with diffusion models like StormCast, which presents a significant step toward the development of future AI models for high-resolution weather prediction.”
Alongside the acceleration and visualization of physically accurate climate simulations, as well as a digital twin of our planet , such research breakthroughs signify how NVIDIA Earth-2 is enabling a new, vital era of climate research.
Learn more about sustainable computing and NVIDIA Research, a global team of hundreds of scientists and engineers focused on topics including climate AI, computer graphics, computer vision, self-driving cars and robotics.
Featured image courtesy of NASA.
See notice regarding software product information.
Share on Mastodon

COMMENTS
This paper presents a meta-analysis of cloud computing research in information systems with the aim of taking stock of literature and their associated research frameworks, research methodology, geographical distribution, level of analysis as well as trends of these studies over the period of 7 years. ... Cloud computing research started to gain ...
Cloud computing has become integral to modern computing infrastructure, offering scalability, flexibility, and cost-effectiveness. Trust is a critical aspect of cloud computing, influencing user decisions in s... Jomina John and John Singh K. Journal of Cloud Computing 2024 13 :134. Research Published on: 21 August 2024.
A COMPREHENSIVE STUDY ON CLOUD. COMPUTING PARADIGM. Ab Rashid Dar 1, Dr. D. Ravindran 2. 1,2 Department of Computer Science, St. Joseph's College. (Autonomous), Tiruchirappalli Tamil Nadu, (Indi ...
The Journal of Cloud Computing: Advances, Systems and Applications (JoCCASA) will publish research articles on all aspects of Cloud Computing. Principally, articles will address topics that are core to Cloud Computing, focusing on the Cloud applications, the Cloud systems, and the advances that will lead to the Clouds of the future.
Cloud computing has become a widely exploited research area in academia and industry. Cloud computing benefits both cloud services providers (CSPs) and consumers. The security challenges associated with cloud computing have been widely studied in the literature. This systematic literature review (SLR) is aimed to review the existing research studies on cloud computing security, threats, and ...
This paper presents a meta-analysis of cloud computing research in information systems with the aim of taking stock of literature and their associated research frameworks, research methodology, geographical distribution, level of analysis as well as trends of these studies over the period of 7 years. A total of 285 articles from 67 peer review journals from year 2009 to 2015 were used in the ...
The cloud literature is analyzed systematically from the management and business point of view. The review is limited with journal articles and papers published between 2014 and 2019. This ...
We present a meta-analysis of cloud computing research in information systems. The study includes 152 referenced journal articles published between January 2010 to June 2023. We take stock of the literature and the associated research themes, research frameworks, the employed research methodology, and the geographical distribution of the articles.
Abstract: Cloud computing stands at the forefront of a technological revolution, fundamentally altering the provisioning, utilization, and administration of computing resources. This paper conducts a comprehensive examination of the visionary aspects, obstacles, and possibilities inherent in cloud computing. It delves deep into the foundational principles and distinguishing features of this ...
Adaptive Two-Stage Cloud Resource Scaling via Hierarchical Multi-Indicator Forecasting and Bayesian Decision-Making. floating-ly/harmony1 • • 2 Aug 2024 The surging demand for cloud computing resources, driven by the rapid growth of sophisticated large-scale models and data centers, underscores the critical importance of efficient and adaptive resource allocation.
Jan 2024. K. B. Aruna. C. Arunachalaperumal. Cloud computing is performed by hosting the data of data owners on cloud servers, where the data consumers (users) are able to get the data over ...
Big Data and Cloud Computing as two mainstream technologies, are at the center of concern in the IT field. Every day a huge amount of data is produced from different sources. This data is so big in size that traditional processing tools are unable to deal with them. Besides being big, this data moves fast and has a lot of variety. Big Data is a concept that deals with storing, processing and ...
Next generation cloud computing systems are aimed at becoming more ambient, pervasive and ubiquitous given the emerging trends of distributed, heterogeneous and ad hoc cloud infrastructure and associated computing architectures. This will impact at least the following four areas considered in this paper.
This research paper presents what cloud computing is, the various cloud models and the overview of the cloud computing architecture, and analyzes the key research challenges present in cloud computing and offers best practices to service providers and enterprises hoping to leverage cloud service to improve their bottom line in this severe economic climate.
This paper investigates the organizational adaptation for cloud computing technology - reviewing case studies from various institutions and companies worldwide to provide a detailed analysis of innovative techniques with cloud computing. ... Finally, we investigate the future research directions for cloud computing and expand this paper into ...
The paper further compares and reviews different layout model for the discovery of services, selection of services and composition of services in Cloud computing. Recent research trends in service composition are identified and then research about microservices are evaluated and shown in the form of table and graphs. Download Full-text.
This paper surveys the two frontiers - Big Data and cloud computing - and reviews the advantages and consequences of utilizing cloud computing to tackling Big Data in the digital earth and relevant science domains. ... This review introduces future innovations and a research agenda for cloud computing supporting the transformation of the ...
This study aims to synthesise the findings of research on cloud computing adoption and use in libraries. This systematic literature review is based on Preferred Reporting Items for Systematic Revie...
Cloud computing today has now been growing as new technologies and new business models. In distributed technology perspective, cloud computing most like client-server services like web-based or web-service but it used virtual resources to execute. Currently, cloud computing relies on the use of an elastic virtual
Cloud Computing is situated to industrialize the IT conveyance of the future. It is a common advancement of the broad selection of numerous specialized progresses in the conveyed computing range ...
The transition to cloud computing in universities is an important step in terms of online education, economic crisis, globalization, and high and constantly changing requirements, especially in the COVID-19 period. Cloud computing can play a very important role in quickly solving the problems faced by universities during this coronavirus period.
Cloud computing technology delivers services, resources, and computer systems over the internet, enabling the easy modification of resources. Each field has its challenges, and the challenges of data transfer in the cloud pose unique obstacles for forensic analysts, making it necessary for them to investigate and adjust the evolving landscape of cloud computing.
This topic is one of the IoT and cloud computing research papers which aims to share a wider range of information. The authors categorize the research into IoT-based systems, cloud-based systems, and integrated systems using both IoT and the cloud. They discussed the pros of real-time data collection, improved care coordination, automated ...
We've compiled 15 important cloud computing research topics that are changing how cloud computing is used. 1. Big Data. Big data refers to the large amounts of data produced by various programs in a very short duration of time. It is quite cumbersome to store such huge and voluminous amounts of data in company-run data centers.
The Internet of Things (IoT) is a powerful technology adopted in various industries. Applications of the IoT aim to enhance automation, productivity, and user comfort in a cloud and distributive computing environment. Cloud computing automatically stores and analyzes the large amounts of data generated by IoT-based applications. Cloud computing has become a crucial component of the information ...
Student. , M.Sc. I.T., I.C.S. College, Khed, Ratnagri. Abstract: Cloud Computing has come of age later Amazons introduce the first of its kind of cloud services in2006. It is. particularly ...
Finding a way to unify this disparate data is essential. In doing so, organizations must balance the explosive growth of enterprise data; the need for an on-premises, cloud-like consumption model ...
Learn more about sustainable computing and NVIDIA Research, a global team of hundreds of scientists and engineers focused on topics including climate AI, computer graphics, computer vision, self-driving cars and robotics. Featured image courtesy of NASA. See notice regarding software product information.